Expel Phishing
Comprehensive phishing detection
and response services
We triage and respond to phishing threats. You focus on what matters.
HOW WE HELP
Investigation and response for your phishing inbox
Expel analysts triage and respond, so you can focus on what matters. We investigate every reported email, tell you when they’re malicious attempts, and close the loop with your employees.
HOW EXPEL IS DIFFERENT
Free up your team, while we prevent phishing
Your employees send potential phishing emails to us and we take it from there. Simply integrate your email provider into our security operations platform, Expel Workbench™, so our platform and our people can do all of the investigative work and let both you and the employee know if the email was malicious or not. We quickly detect and respond to phishing — so your team can focus on what matters most.
WHAT YOU GET
Expel Phishing
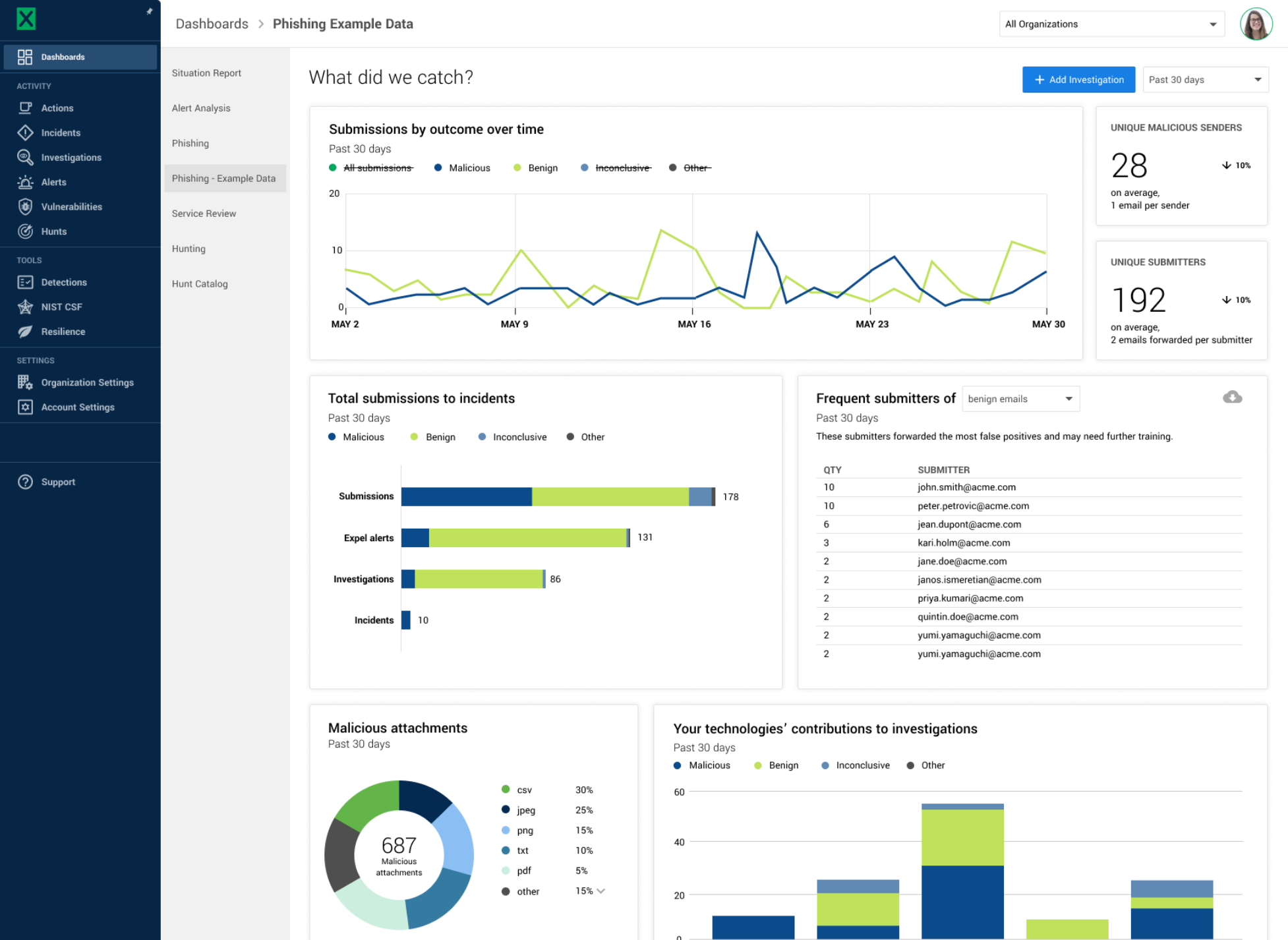
A detailed phishing dashboard with insights into trends, submitters, senders and their domains
Emails prioritized by potential risk to reduce noise and prevent malicious emails
Investigation of suspicious emails starts with our platform, automated rules and leverages Expel analysts
Remediation guidance with actions to improve your phishing prevention program





