EXPEL SECOPS PLATFORM AI AND AUTOMATION
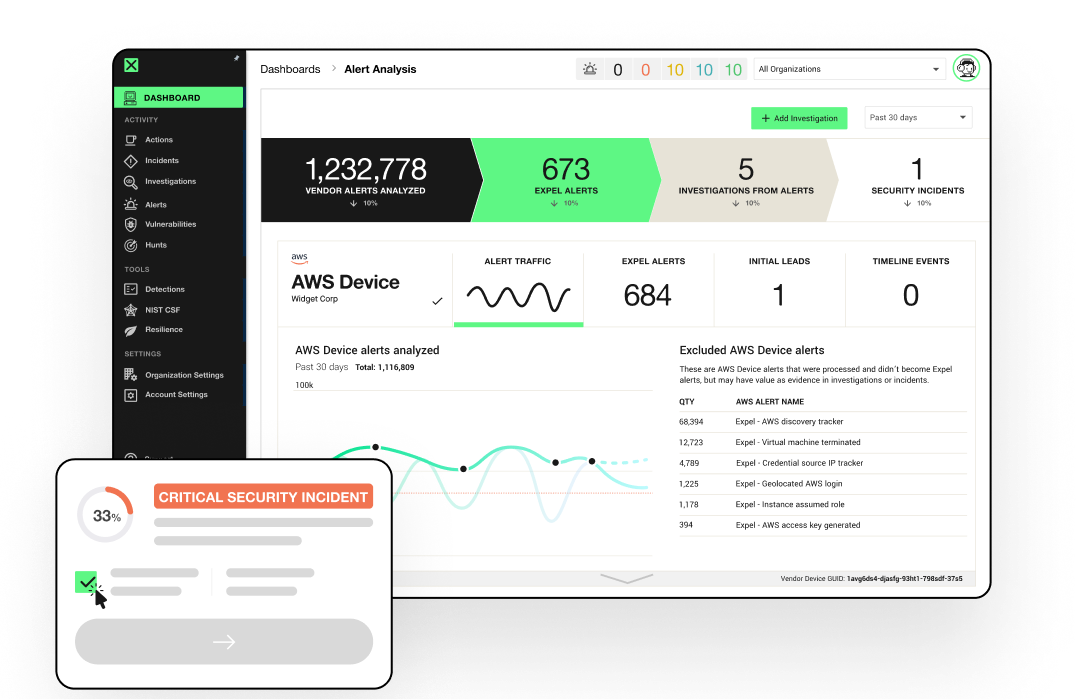
Our SOC’s digital command center
Our analysts use the AI-powered Expel Workbench™ to work more efficiently and silence the noise. The result: industry-leading MTTX numbers.
EXPEL’S SECURITY OPERATIONS PLATFORM
You bring the tech.
We’ll bring the results.
We unlock your security tools with Expel Workbench™ platform with built-in AI and automation that connects your tech and our experts for faster decisions and better outcomes.
WHAT WE USE
Our security platform that powers your security outcomes
Workbench fuels our analyst with the speed and intelligence needed to deliver exceptional results, while you have a front-row seat to the action.
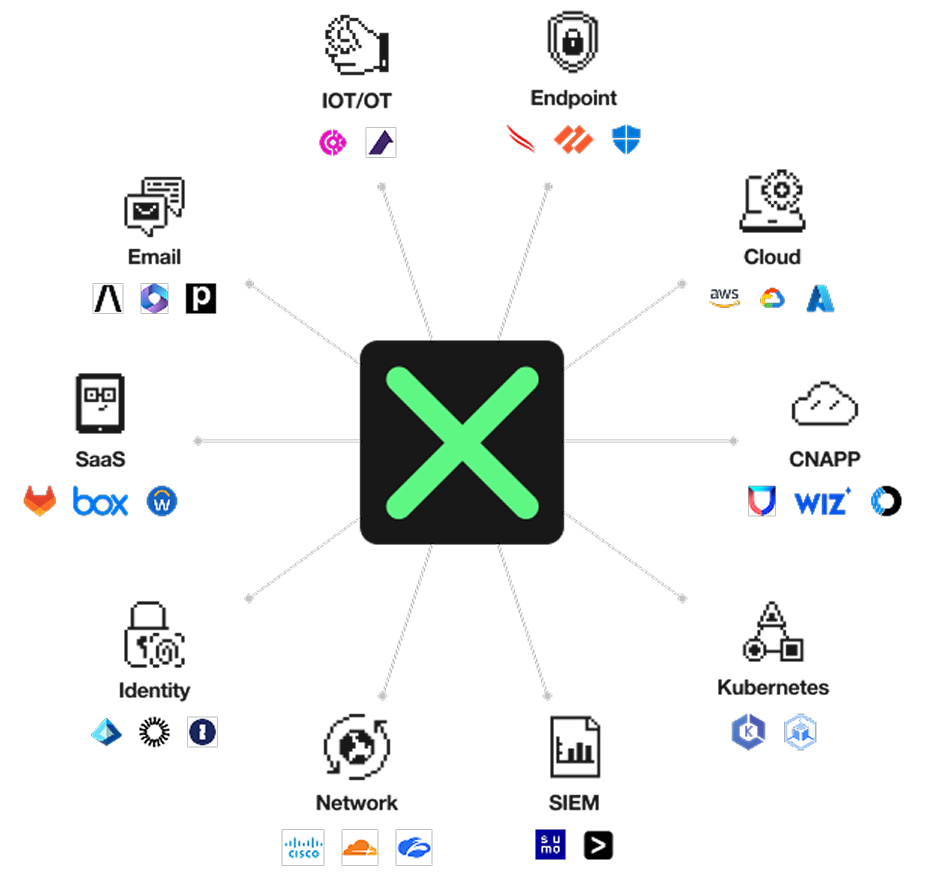
WHAT WE PROTECT
Secure everywhere.
No blind spots, no compromises.
Workbench connects to your entire tech stack, providing complete visibility and defense. Expel-written detections cover you from your endpoints to the cloud, including between your point solutions.
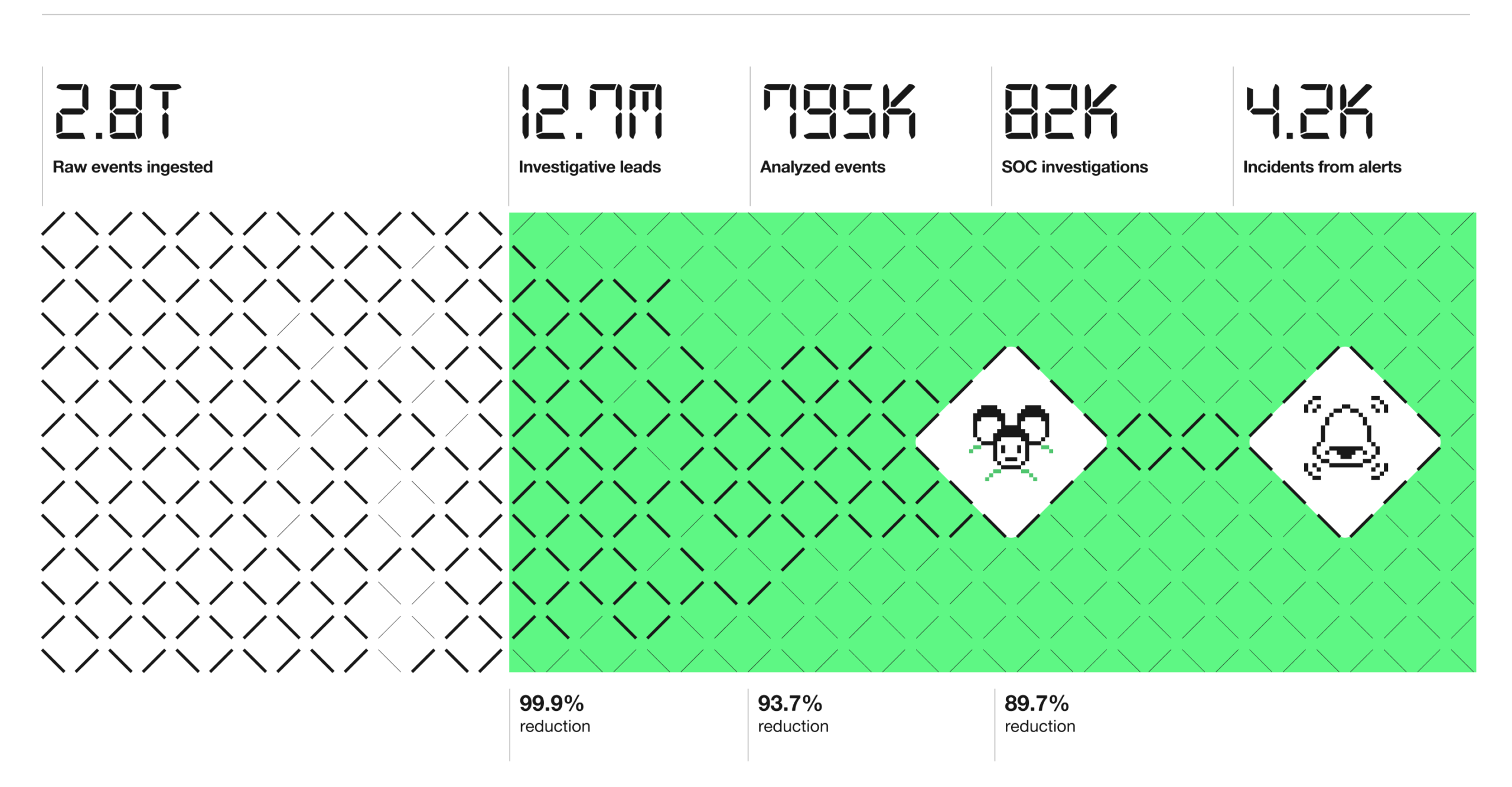
Next-Level MTTX
We’ve redefined MDR benchmarks
The numbers don’t lie. Workbench enables our SOC to deliver outcomes, faster.
14
minute MTTR
on critical/high incidents with auto-remediation
160+
integrations
across ten attack surfaces
87%
MTTR reduction
with auto-remediation
75
customer
NPS
AI-powered efficiency
AI and automation designed for the “human moment”
Expel Workbench uses AI and automation to provide SOC analysts with all the data and context they need for faster investigations, enabling faster answers and more time to collaborate with you.
Expel’s automation instantly provides critical decision support and filters out the noise so we focus on true threats
APIs allow easy query capabilities across a broad tech stack without the need for manual pivots
Analysts can easily aggregate data with the full context of your environment, helping answer the necessary investigative questions
Expert written incident reports provide a clear picture of what occurred and what was done to remediate the threat

WHAT OTHERS SAY
Here’s what our customers have to say

“Security really is a team sport. With Expel, we have another set of eyes looking at this thing and backing us up. We’re backstopping each other at the end of the day. Because we’re all working from the Expel platform, Workbench, we can collaborate effectively and ensure nothing falls through the cracks.”

“One major benefit of working with Expel is that I can use whatever security tools I want. Most legacy MSSPs require you to work with certain tech or purchase new tech in order to work with them. I appreciate that I had the flexibility to select whatever tech worked best for my org as opposed to what was convenient for the provider.”

“[Expel Workbench™] allows security analysts to follow investigations in real time, see every action taken, and communicate seamlessly with the Expel team. Shared information makes us all better, and the platform facilitates that in a way I never saw before.”