Videos
Videos
AI malware: Fact vs. fiction (with Marcus Hutchins) | Nerdy 30, Episode 6The headlines say AI is rewriting the malware playbook. The reality is a little more complicated. AI-generated phishing is real. AI-assisted code is real. But “autonomous AI malware wrecking cybersecurity”? That’s a…
Videos
Is your identity security strategy broken? | Very Important QuestionsWhy IAM is fundamentally fragmented, how attackers are bypassing MFA, and what identity security actually requires in a world of AI agents and non-human identities Date: March 17, 2026 Duration: 24 minutes Format:…
Videos
Iran cyber threats: What security teams need to know right now | Expel briefingVideo: Watch the full briefing Primary focus: Iran cyber threats and defensive recommendations Date: March 2026 Featuring: James Shank, Director of Threat Operations, Expel Steph Shample, Iran Intelligence Expert, Adjunct Professor at…
Videos
An insider’s look at the NIS2 directive and DORA | Very Important QuestionsA field CISO’s perspective on navigating EU cybersecurity regulations, exploring how managed detection and response capabilities support NIS2 directive and DORA compliance—from incident reporting requirements to the real-world challenges of regulatory oversight…
Videos
Reigning in cloud identity security: Expert insights | Nerdy 30, Episode 5A candid, expert-led discussion on the rapidly evolving challenges of cloud identity security—from identity sprawl and permissions creep to non-human identities and the coming wave of AI agents. With 74% of security…
Videos
Expel detection overview
You've spent hundreds of thousands (or more) on security tools. Okta, CrowdStrike, your SIEM, cloud security—the whole stack. But here's the thing: integrations ≠ outcomes.
Videos
The state of the managed detection and response vendor market | Nerdy 30, Episode 4A fast, candid look at the rapidly shifting managed detection and response vendor landscape. From the surge of AI SOC startups to platformization, consolidation, and the changing expectations of security teams, this…
Videos
Building effective threat detection engineering programs | Very Important QuestionsExploring how detection quality, alert enrichment, and strategic signal management reduce analyst burnout while improving security coverage Date: October 7, 2025 Duration: 31 minutes Format: Video interview Featuring: Ben Baker, Director of…
Videos
Account takeover detection: How we defended against an insider threat | SOC BytesExploring how security teams can detect and respond to compromised accounts before they lead to ransomware and business email compromise Date: October 2, 2025 Duration: 4 minutes Format: Video interview Featuring: Ben…
Videos
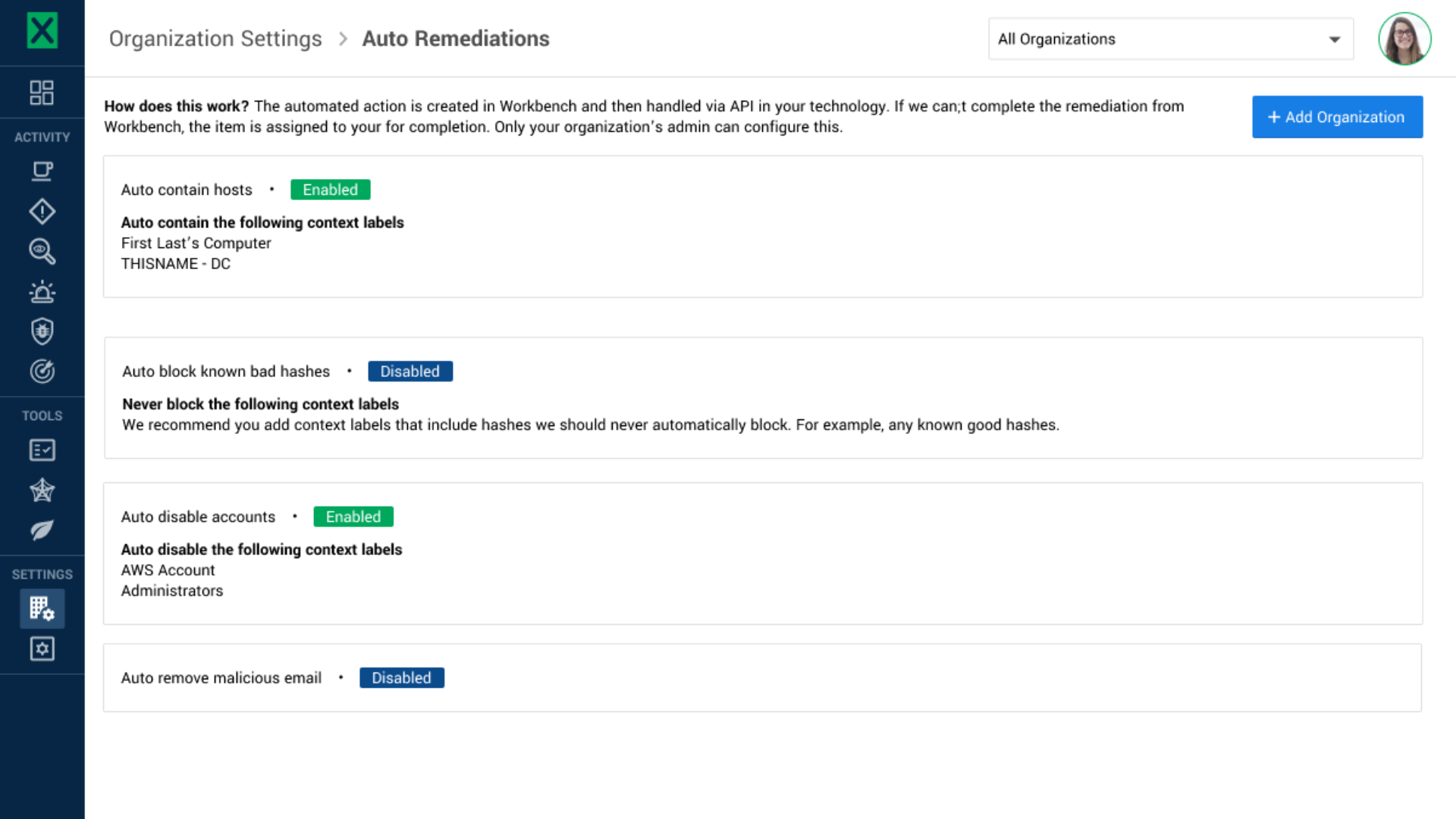
Why cybersecurity automation is critical for threat response | Very Important QuestionsExploring how automated remediation actions can reduce analyst burden while improving response times and consistency in security operations Date: August 19, 2025 Duration: 17 minutes Format: Video interview Featuring: Ben Baker, Director…
Videos
Storytelling in cybersecurity | Meet the Expletives: Hafsah MijinyawaWelcome back to “Meet the Expletives.” In this episode, Ben Baker chats with Hafsah Mijinyawa, Expel’s Senior Motion Designer. They dive into Hafsah’s creative journey, her love for storytelling and how it…
Videos
How AI can help overcome cybersecurity burnout | Nerdy 30, Episode 3Exploring the role of AI in cybersecurity and how artificial intelligence can help security teams reduce burnout while improving operational efficiency. Learn practical strategies for implementing AI in cybersecurity from industry experts.…
Videos
How to measure a SOC | Nerdy 30, Episode 2A comprehensive guide to measuring SOC efficiency and performance featuring proven strategies for balancing speed and quality in security operations from experienced SOC leaders. Date: July 30, 2025 Duration: 30 minutes Featuring:…
Videos
Mastering cybersecurity certifications exams | Nerdy 30, Episode 1A comprehensive guide to studying for cyber security certifications featuring proven learning strategies based on cognitive psychology and real-world experience from cyber security professionals. Date: July 16, 2025 Duration: ~30 minutes Featuring:…
Videos
Why humanity matters in cybersecurity | Meet the Expletives: Brooke McClaryIn this episode of Meet the Expletives, we sit down with Senior Communications Manager, Brooke McClary. Brooke shares her unconventional career journey, the value of hiring for traits over degrees, and what…
Videos
Expel MDR onboarding | Get up and running in 7 minutes or lessA live demonstration of Expel’s streamlined MDR onboarding process, showing how customers can integrate multiple security tools and begin monitoring in minutes, not weeks. Featuring: Paul Lawrence, Global Solutions Architect, Expel Executive…
Videos
Live from RSAC 2025: Dave Merkel on AI, identity, ransomware, and moreLearn why Kubernetes and security can be a tricky combination. Ethan Chen, Senior Product Manager at Expel, shares insights on Kubernetes, gaining Kubernetes security context, and how to get started with Kubernetes.
Videos
The power of culture and feedback | Meet the Expletives: Fred HouseIn this episode of “Meet the Expletives,” Ben Baker sits down with Expel’s Vice President of Detection Engineering and Innovation, Fred House. They discuss Fred’s career journey, what drew him to Expel,…
Videos
Roundtable | On Scattered Spider and the Atlas Lion threat groupA LinkedIn Live roundtable discussion featuring Expel security experts exploring a novel cloud attack by the Atlas Lion threat group, a subset of Scattered Spider. Date: April 30, 2025 Featuring: Ben Baker,…
Videos
Understanding Kubernetes and security with Ethan ChenLearn why Kubernetes and security can be a tricky combination. Ethan Chen, Senior Product Manager at Expel, shares insights on Kubernetes, gaining Kubernetes security context, and how to get started with Kubernetes.
Videos
Integrating partners and building culture | Meet the Expletives: Sami RidelGet to know Sami Ridel, Partner Integrations Manager at Expel. Sami joins the conversation to: share insights on partnership management and team security culture discuss Expel’s team culture and values talk about…
Videos
Roundtable | Inside the managed detection and response marketA LinkedIn Live roundtable featuring Expel experts discussing their recognition as a Leader in the Q1 2025 Forrester Wave for Managed Detection and Response (MDR) Services Date: March 12, 2025 Featuring: Ben…
Videos
Roundtable | 2025 Annual Threat Report key insightsA LinkedIn Live roundtable discussion featuring Expel security experts exploring the most significant cybersecurity trends from Expel's 2025 Annual Threat Report.
Videos
Best-in-class Security Operations with ExpelHear from our SOC leaders and analysts about how Expel makes partner-focused, technology-driven, best-in-class MDR service possible.
Videos
Mind map for AWS investigationsOur SOC team remediates quite a few incidents in Amazon Web Services (AWS). When running these incidents down, some common themes emerged about when and why attackers use different AWS APIs –…
Videos
Simplifying your multi-cloud security with ExpelManaging security across multiple clouds is a complex job. And the security tools provided by cloud service providers can add to the noise by generating a never-ending barrage of alerts (and very…
Videos
Maximize your existing SIEM investmentWith Expel Managed Detection and Response (MDR), you can transform alerts into answers for decision support with your existing SIEM investment.
Videos
Ep. 26 | IT Trendsetters Interview Series | Expel
Tune-in for a video interview with Jon Hencinski, VP, Security Operations, Expel, for IT Trendsetters.
Videos
How Expel customers see measurements improve over time
See how Expel dashboards help answer the question “are we getting better, together” through metrics.
Videos
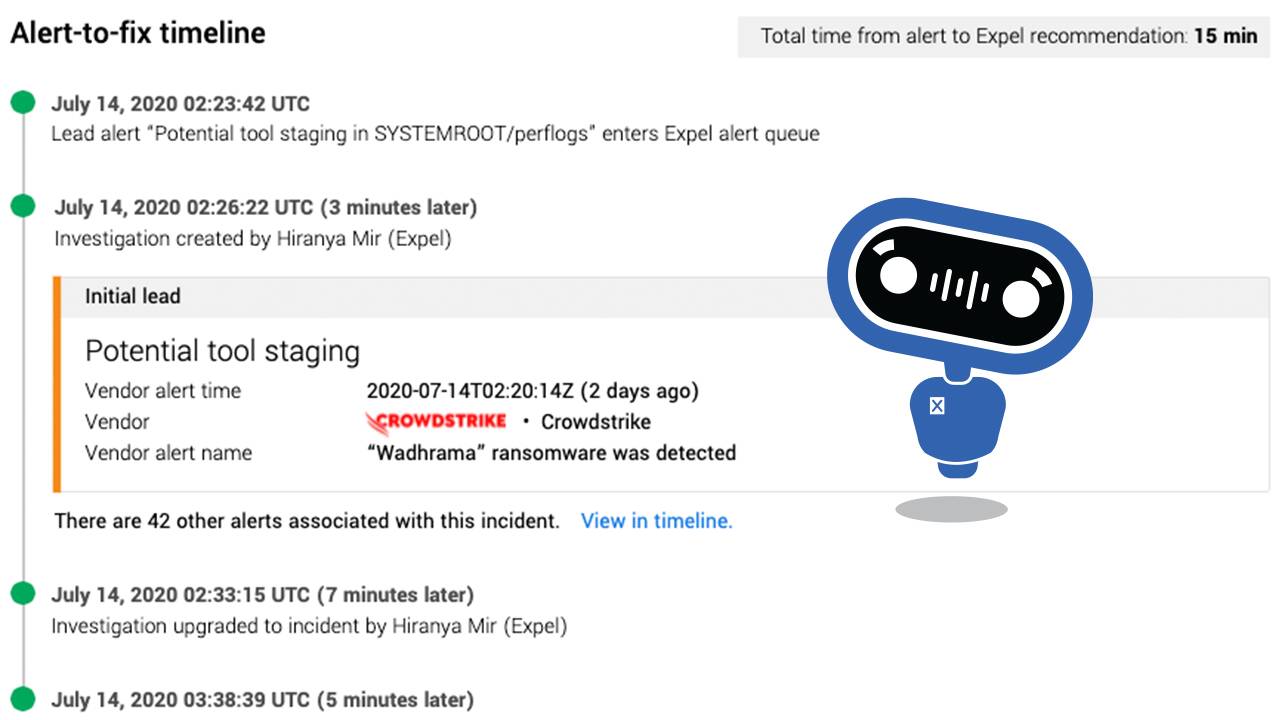
Inside an Expel response
See why our median alert-to-fix timelines are shorter than the time it takes to deliver a pizza.
Videos
A message from our Expel founders
We’ve reached a valuation over $1 billion thanks to our Series E fundraising round, led by CapitalG. Check out what our founders have to say about this exciting news and what’s next for Expel.
Videos
Expel Detecting And Defending Against Ransomware
In this on-demand webcast, independent information security expert and author of the best-selling book Hacking For Dummies, Kevin Beaver, joins Expel to discuss this critical aspect of your information security program and what’s likely one of your greatest IT-related risks.
Videos · May 26, 2021
Why hunting is more than looking for threats
Expel’s Matt Peters, Chief Product Officer, and Bryan Geraldo, Senior Detection and Response Engineer, explain what we mean when we say hunting.
Videos
Inside an investigation: compromised AWS access keys
Hear how we caught an attacker that used a developer’s machine to gain access to AWS.
Videos
Stories from the SOC: Investigating a phishing attack
Expel’s Ray Pugh walks through a phishing investigation. Learn how our analyst determines if it was malicious, who has been compromised and how to get left of the threat.
Videos
Fighting the Good Fight: Your 30min Guide to Threat Hunting
Expel’s Matthew Hosburgh and VMware Carbon Black’s Greg Foss, demystify threat hunting and chat about what you can do to keep your org secure.
Videos · October 15, 2020
How to leverage security automation to identify malicious activity
Expel’s Anthony Randazzo and Exabeam’s Andrew Skrei talk about how you can gain visibility to determine what’s malicious and not - all while getting time back in your day.
Videos · October 13, 2020
BEC all grown up: What you need to know now
The three major “whys” behind BEC: Get money, get data, or get access to money/data later.
Bruce Potter and Tyler Fornes chat about what BEC is, types of attacks, how compromise can start with phishing, and best practices to minimize BEC for your business.
Videos · August 12, 2020
EXE Live | How to get started with a multi-cloud strategy
Expel's Andrew Pritchett and Lacework's Chris Pedigo help make sense of the gigantic security signals from the clouds and chat about some best practices.
Videos
EXE Live | Finding contrails: How to track data access in the cloud
Mary Singh and Andrew Pritchett will walk through different ways to track data access in the cloud and share configuration tips.
Videos
Conquering GCPs IAM hierarchy: Where to get started with Service Accounts
Andrew Pritchett and Peter Silberman walk through GCP Service Accounts best practices.
Videos
Following the CloudTrail: Where to get started with AWS security monitoring
Expel's Matt Peters and Peter Silberman walk through how to use AWS capabilities as part of your detection and response strategy.
Videos
ISMG Interview: Beyond the Black Box of MSSPs
Expel CTO Matt Peters talks to ISMG about the questions businesses should ask as they're evaluating MSSPs, and how MSSPs can be more proactive about making their customers more resilient.
Videos
Connecting network and endpoint data to find attackers
Watch this recorded webinar to see how to piece together evidence from endpoint & network detection and response tools -- like CarbonBlack and ProtectWise -- to tell the complete story of an incident.
Videos
How to build a detection and response program
Listen in as Endgame and Expel chat about what an effective detection and response program looks like, key metrics to measure whether your program is effective, and how a managed endpoint detection and response program can help you.
Videos
Investigating with Darktrace
Expel analysts get to use a lot of really cool network and endpoint technologies. In this video, we highlight some of our favorite investigative features of Darktrace.