You've spent hundreds of thousands (or more) on security tools. Okta, CrowdStrike, your SIEM, cloud security—the whole stack. But here's the thing: integrations ≠ outcomes.
VIDEOS
Stop guessing where AI belongs in your SOC.
Take your assessmentVIDEOS
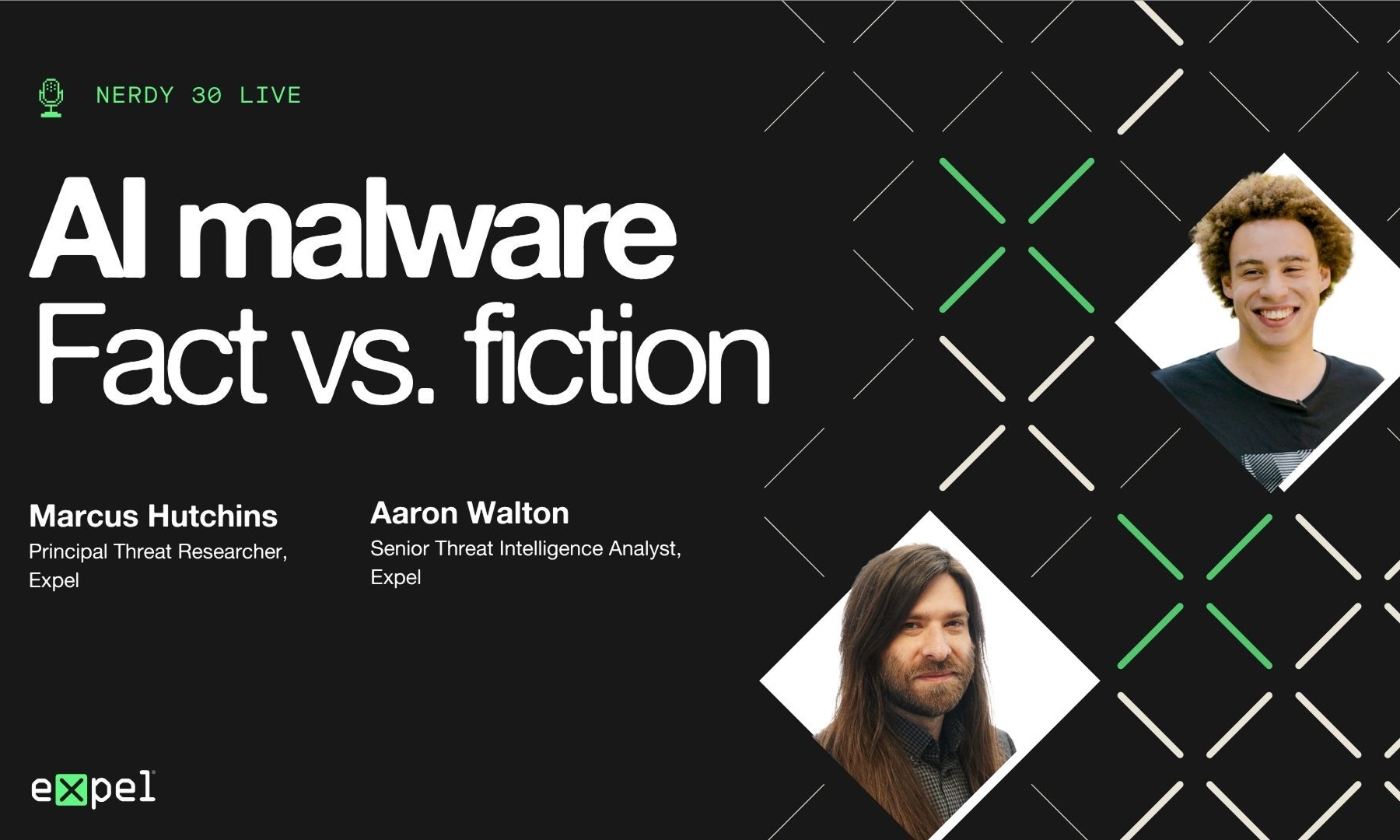
The headlines say AI is rewriting the malware playbook. The reality is a little more complicated. AI-generated phishing is real. AI-assisted code is real. But “autonomous AI malware wrecking cybersecurity”? That’s a…

Why IAM is fundamentally fragmented, how attackers are bypassing MFA, and what identity security actually requires in a world of AI agents and non-human identities Date: March 17, 2026 Duration: 24 minutes Format:…

Video: Watch the full briefing Primary focus: Iran cyber threats and defensive recommendations Date: March 2026 Featuring: James Shank, Director of Threat Operations, Expel Steph Shample, Iran Intelligence Expert, Adjunct Professor at…