MEET RUXIE
Accurate defense
at AI speed
Ruxie, the AI that runs our SOC, handles the volume. Our analysts handle the judgment. Together, they close the gap faster than either could alone.
EXPEL’S AI PHILOSOPHY
AI-intentional beats AI-hype
Speed without accuracy is reckless. Accuracy without speed is useless. We’ve spent years building for both.
Out of a million events, I would say 99.5% of them are filtered out in triage by AI, machine learning, and automation before we actually need to have eyes on the actual issue.
OUR APPROACH
Faster decisions. Better outcomes.
Ruxie handles what slows analysts down. Analysts handle what requires judgment. Humans watching AI, and AI watching humans.
In security, that balance isn’t optional.
Proven Results
Speed matters for AI cybersecurity
Expel MDR powered by Ruxie
Other SOCs
Mean time to detect (MTTD)
5 minutes
Minutes to months
Mean time to remediate (MTTR)
14 minutes
Hours to days
Alerts investigated
100%
~ 30%
Investigation time spent per alert
~3 minutes
~ 30 minutes
Your time spent triaging
~0%
~ 80% on Tier-1 triage
WHITEPAPER
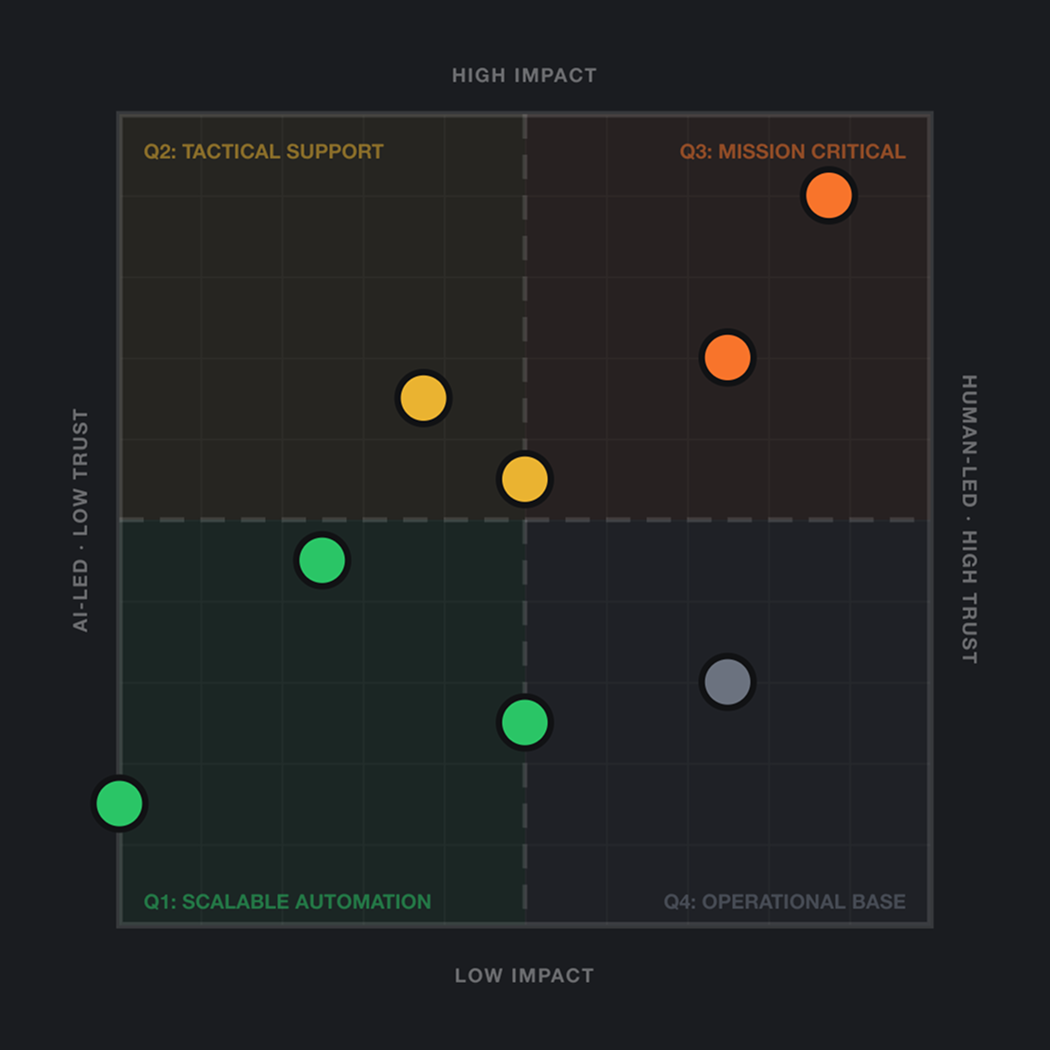
Trust vs. Impact Framework
The question isn’t whether to use AI. It’s where to trust it—and where the stakes are too high to find out.
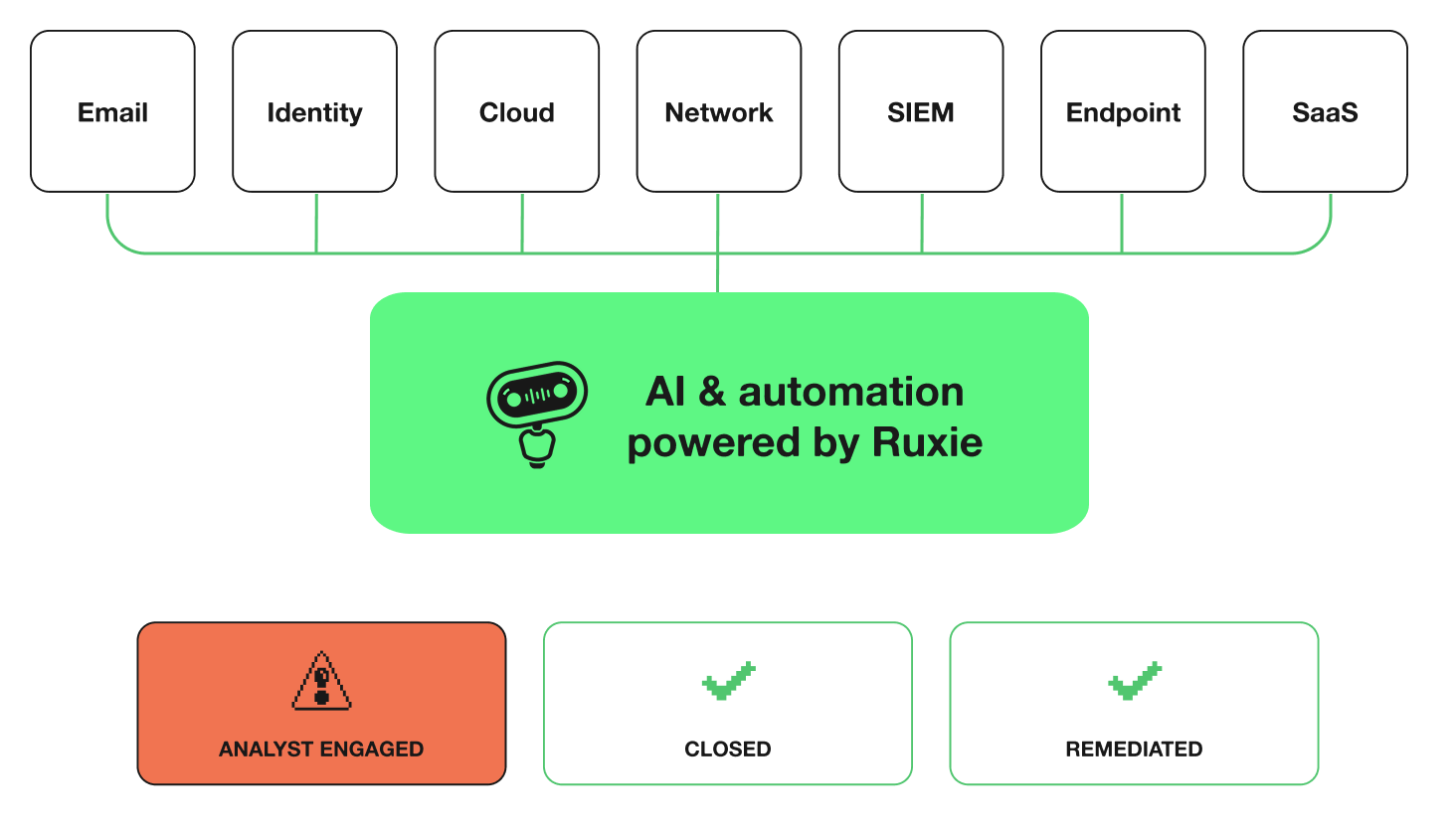
How Ruxie works
From signal to action. Faster.
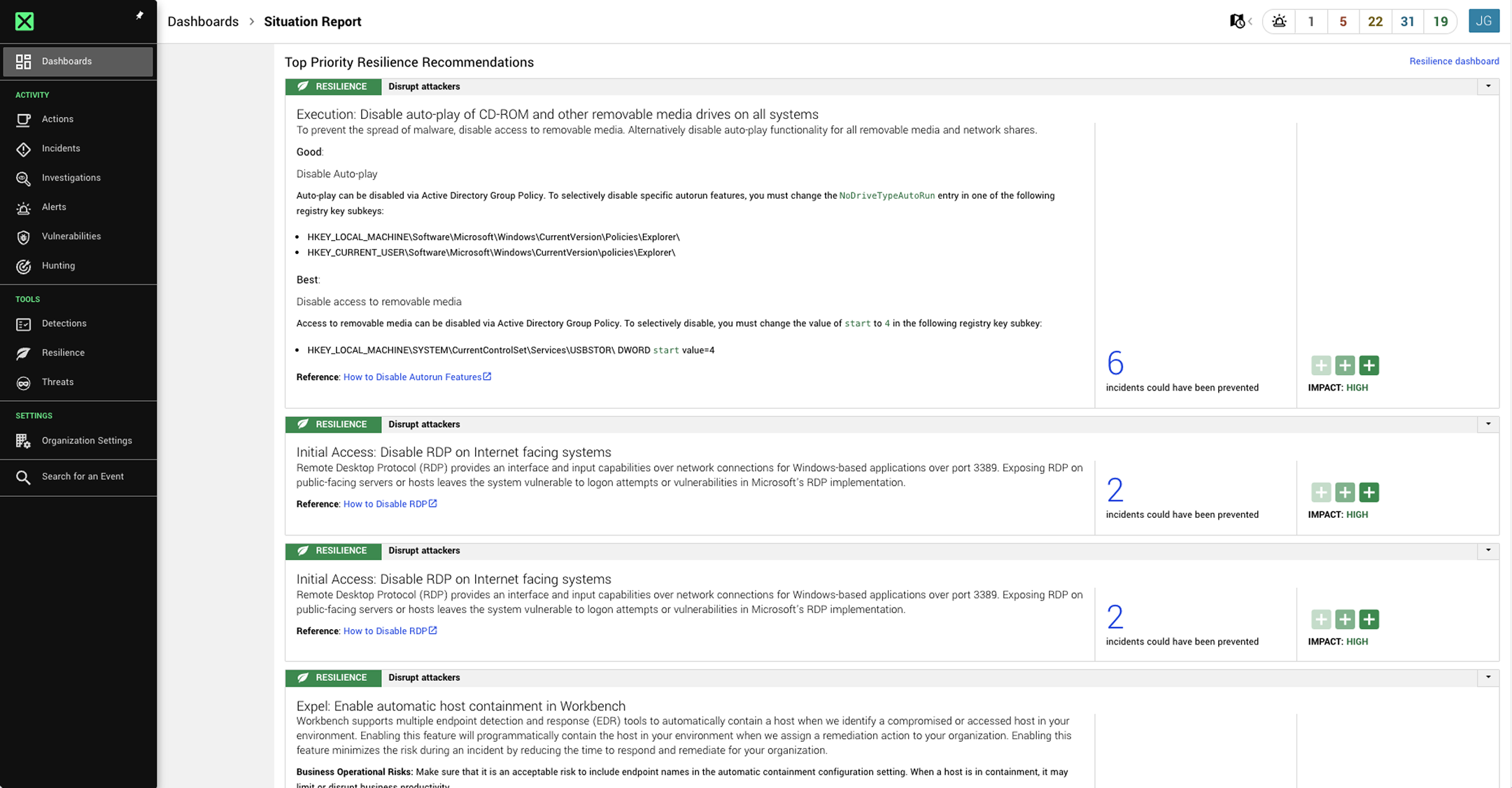
Every Ruxie capability is built to close the distance between seeing a signal and taking action. Faster decisions. More accurate outcomes. Every time.
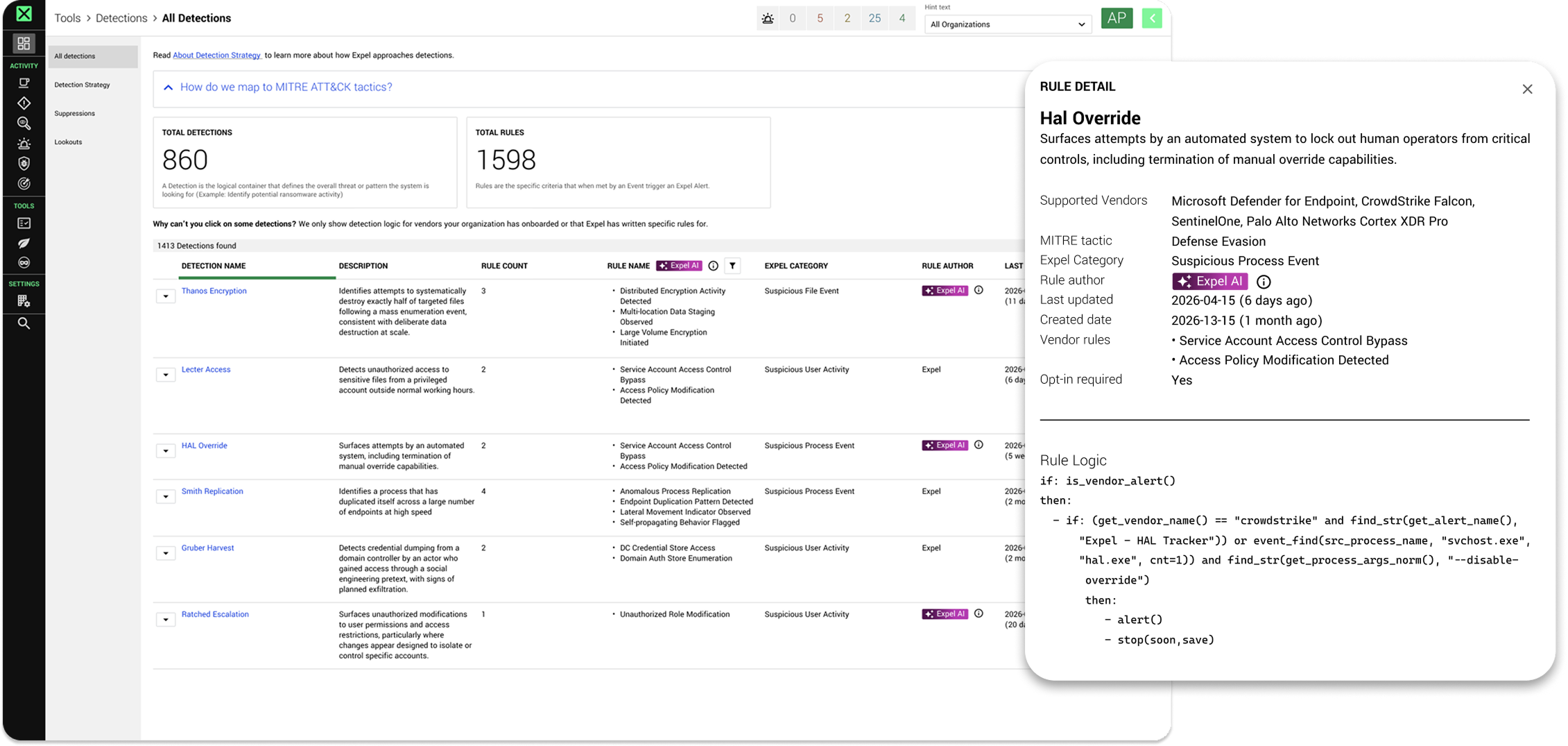
Faster coverage of what’s emerging
Ruxie drafts detection rules for newly seen alerts and flags MITRE ATT&CK gaps, ready for quick engineer approval and deployment.
Full picture before analysts even ask
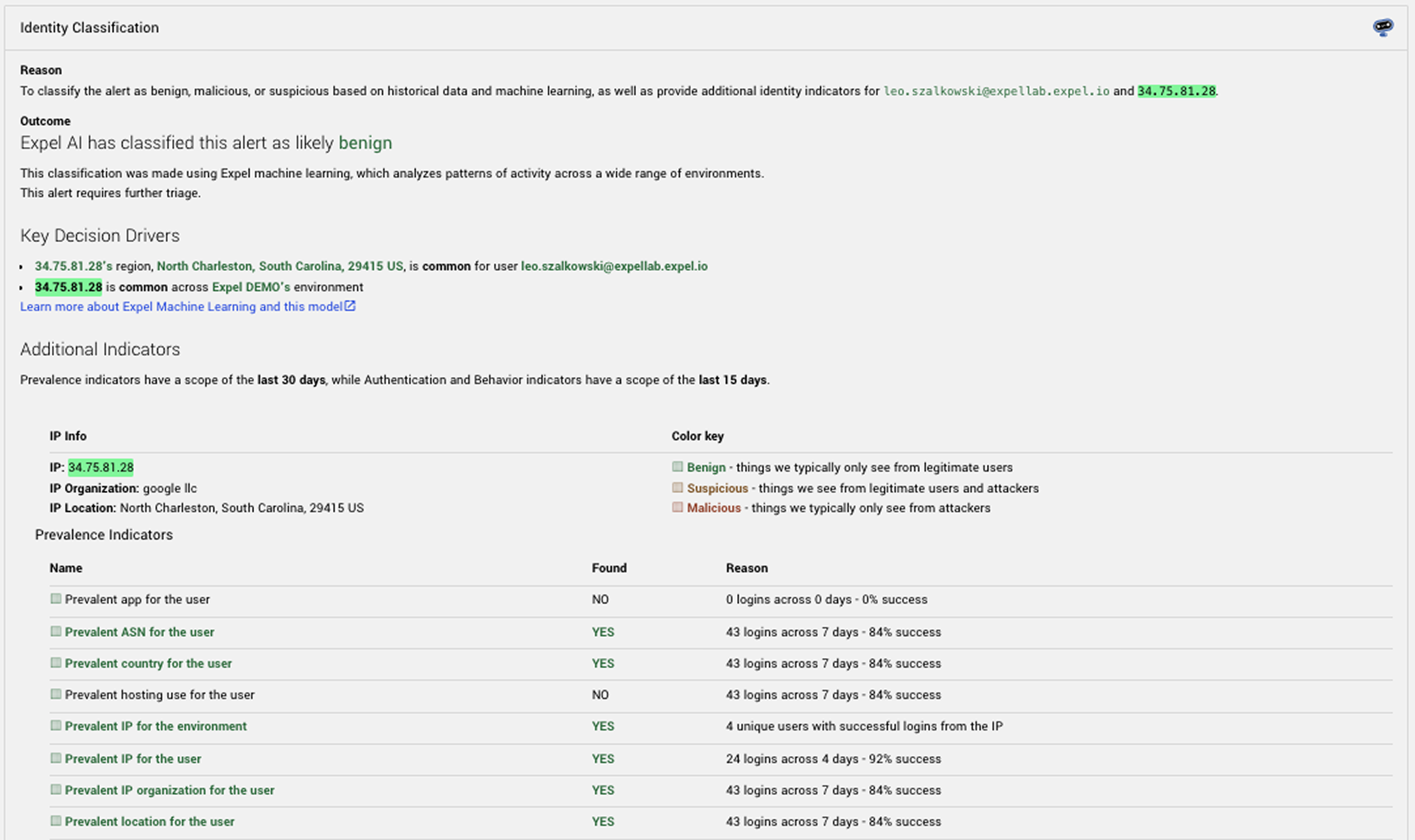
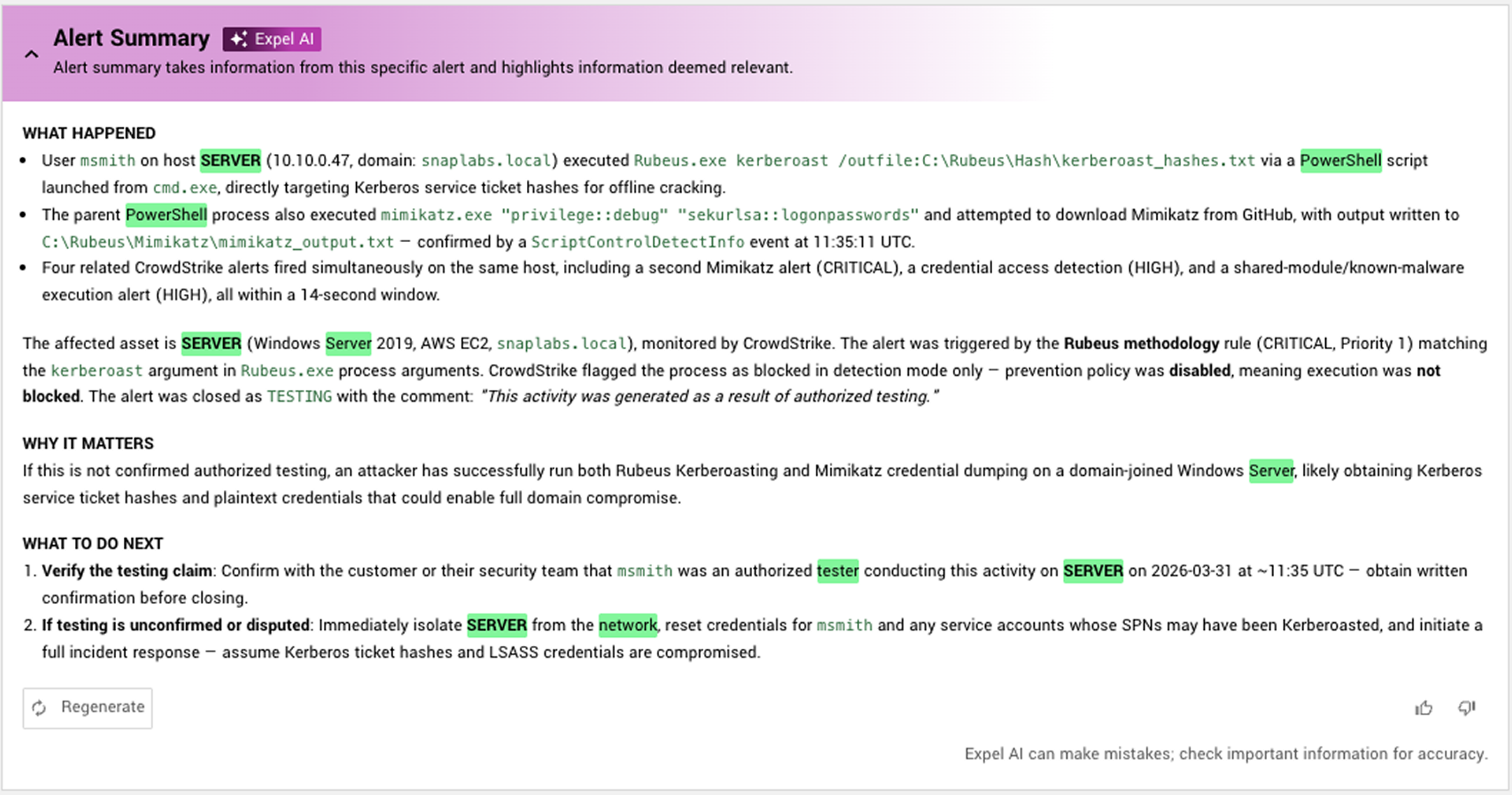
Ruxie adds environment, user, and business context before our analysts open an alert—so they can make the right call, not just the fast one.
Answers ready at the moment they’re needed
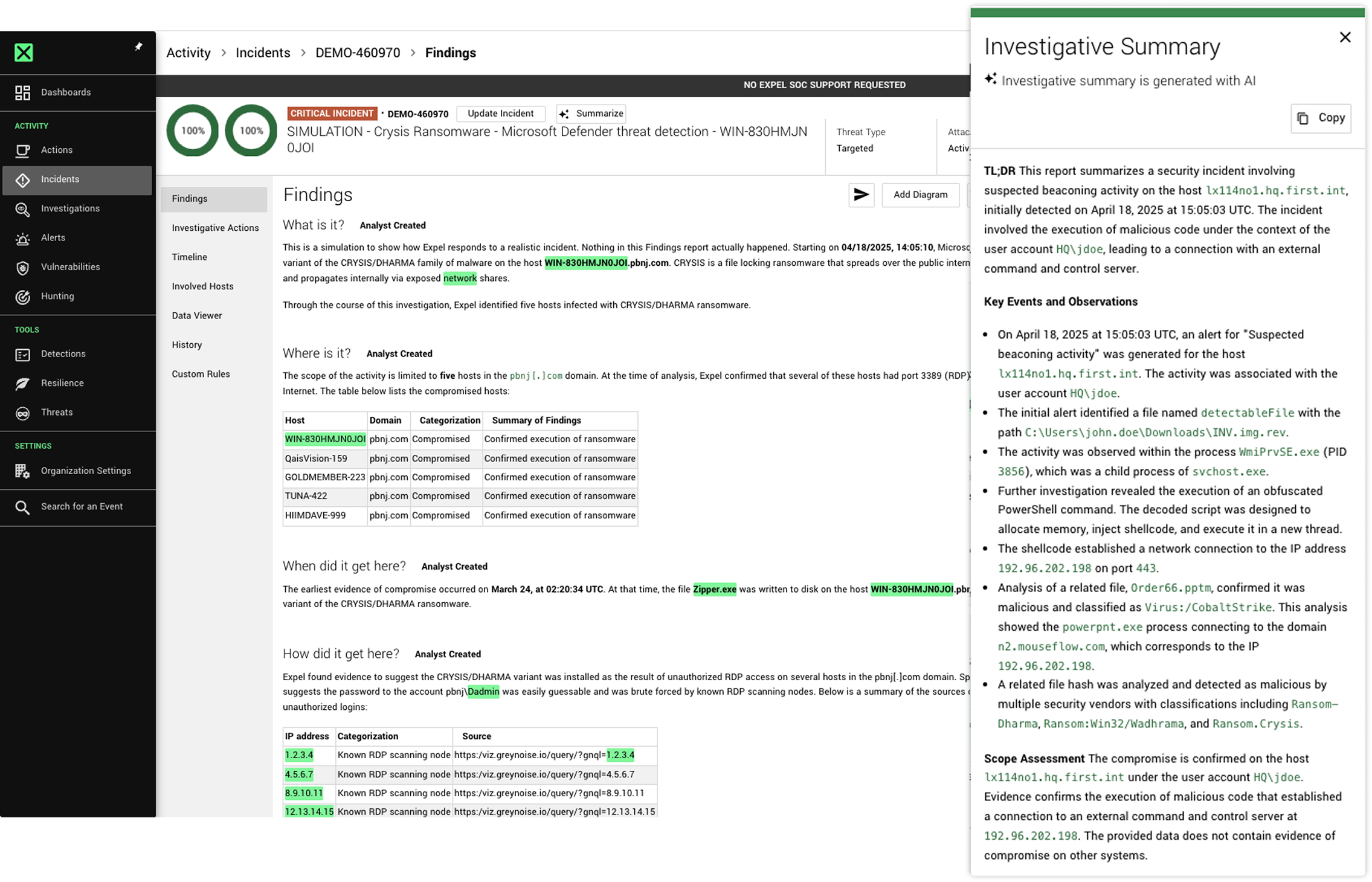
Ruxie synthesizes findings into plain-English analysis—what happened, what was done, what comes next—so analysts act on conclusions, not raw data.
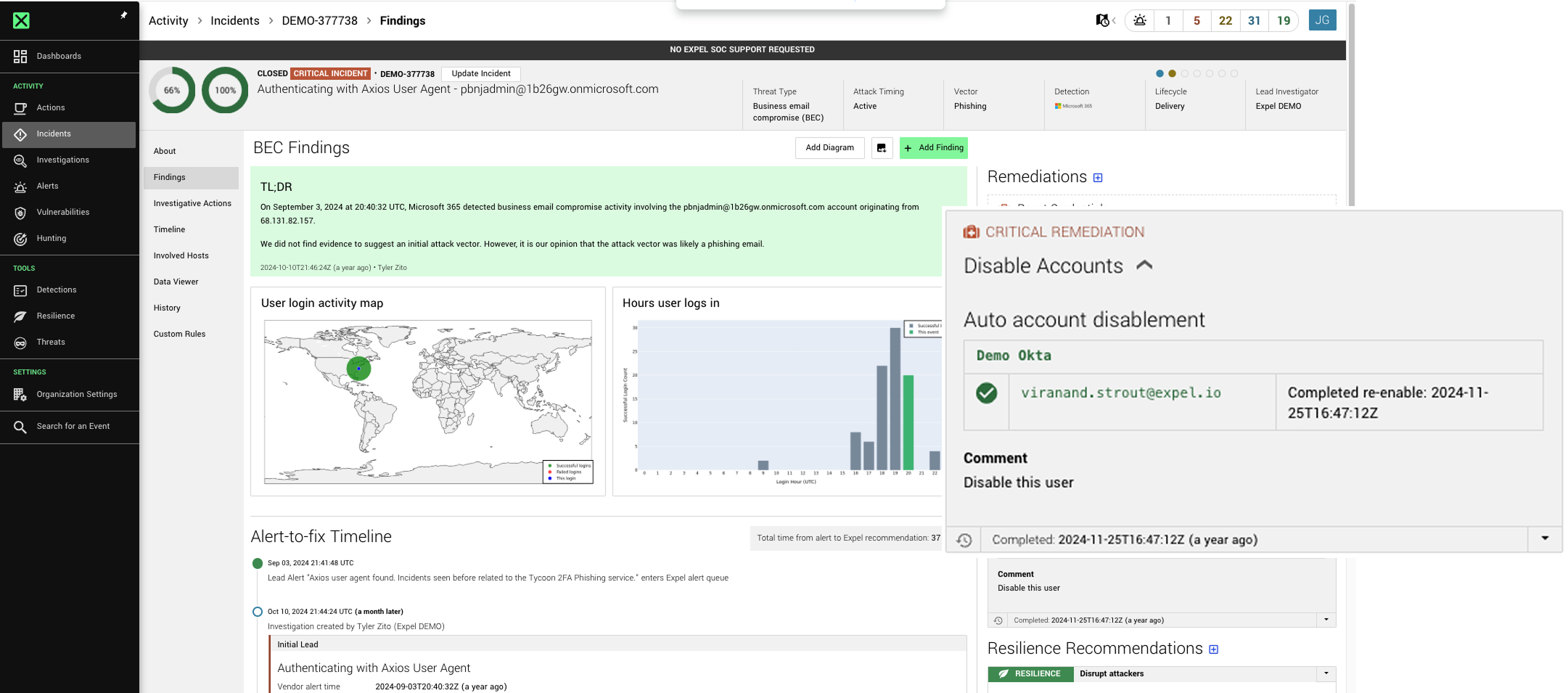
From decision to containment in seconds
Our analysts make the call. Ruxie executes—isolating hosts, disabling users, blocking IPs—so the time between alert and fix is measured in minutes, not hours.
Every action explained every time
Our analysts and Ruxie show their work. You see the reasoning behind every decision, every automated action, and every outcome. No black boxes.
Every closed case shortens the next one
Every decision our analysts make sharpens Ruxie’s model—so detection gets more accurate, triage gets faster, and the path from signal to action gets shorter over time.
RUXIE’S CAPABILITIES
Years of SOC work. Built into Ruxie.
Each capability targets a specific friction point between detecting a threat and acting on it. Built from years of watching where analysts lose time.
Third-party alert enrichment
Enriches alerts with risk scores and infrastructure intelligence from external feeds (VirusTotal, VMRay, Spur) for domains, IPs, and hashes.
Email risk & forensics context
Pulls forensic evidence, user context, rule metadata, and sender reputation from platforms like Abnormal AI, Proofpoint, and Sublime Security.
Asset & identity contextualization
Tags alerts with business-critical details, managed device status, user roles, and public intelligence to prioritize risk by business impact.
Dynamic context creation
Automatically populates customer context based on AWS ingested logs, used for detection and triage.
Historical activity baselines
Compiles 30-day behavioral profiles (login history, location trends, MFA activity) to establish a baseline for normal user behavior.
Network & web traffic analysis
Gathers granular network context from tools like Zscaler, Arista, and Palo Alto, mapping behavior across the environment and providing context for endpoint and cloud alerts.
SIEM telemetry aggregation
Organizes disparate logs such as process details, login history, and device metadata from existing SIEM tools into a single unified view.
Cloud telemetry analysis
Ingests and correlates AWS, Google Cloud, Azure, Oracle, and cloud workload logs to map user behavior and role usage across all cloud environments.
Endpoint & EDR telemetry automation
Instantly parses host timelines and verifies process execution across CrowdStrike, SentinelOne, Microsoft Defender, Cybereason, and more.
Agentic vendor alert detection generation
Evaluates new vendor alerts and generates specific detection rules for security teams to review and use.
Cloud perimeter monitoring
Proactively flags critical posture changes, such as new AWS/Azure security group rules allowing public inbound access or exposed S3 buckets.
Network behavior pattern analysis
Correlates network traffic over time to identify persistent beaconing patterns and suspicious outbound communications to malicious infrastructure.
SaaS alert triage
Audits SaaS app activities such as file sharing, sensitive data access, and authentications to identify malicious behavior or unauthorized data exposure.
Enterprise-wide email scoping
Scans O365 or Google Workspace to identify every recipient of a phishing campaign and removes malicious emails from all inboxes.
Marketing email triage for phishing
Uses machine learning (ML) models to identify marketing emails and automatically triages phishing alerts.
AI-generated related alert context
Summarizes findings from correlated alerts into a single narrative to speed up triage and reduce investigation time.
AI-generated alert summaries
Synthesizes alert details into plain-English summaries covering impact and recommendations for faster threat assessment.
Cloud identity & authentication analysis
Evaluates AWS/Azure/Google Cloud identity and access, Okta SSO, Duo, and Azure IDP events to provide context for historical user behavior and automatically triage known benign activities.
AI user context summaries
Summarizes identity and endpoint logs into a clear narrative of user roles and recent activity for faster triage.
ML identity alert classification
Leverages machine learning (ML) models trained on historical patterns to predict and auto-close benign login alerts, reducing the amount of manual triage needed by the security team for identity alerts.
Phishing & URL analysis
Safely submits indicators to a sandbox for safe detonation and automated reporting.
On-demand deep investigations
Executes automated and manual queries across many technologies to gather and provide analysts with additional context for suspicious behavior and potential blast radius.
Automated event timelining
Generates chronological timelines from SIEM, WAF, Active Directory, and cloud log sources to automatically surface user, IP, domain, and authentication activity to accelerate root-cause analysis.
Key findings generation
Generates plain-English summaries using LLMs of critical investigation findings to help teams understand and report security incidents quickly.
Disable user account
Disables compromised user accounts, resets credentials, and terminates active sessions to stop lateral movement.
Disable access key
Automatically revokes compromised AWS or cloud access keys to lock down environments during an active threat.
Kill process
Terminates malicious processes across endpoints.
Contain host
Isolates hosts from your network and severs all communication with other business applications.
Block bad hash
Blocks potentially malicious processes and files based on their hash values.
Delete malicious file
Deletes potentially malicious threat artifacts.
Delete registry key
Removes malicious persistence entries from Windows Registry.
Reset credentials
Invalidates user passwords and terminates active sessions.
Remove malicious email
Hunts down and purges confirmed malicious emails from inboxes.
Undo alert-driven auto containment
Uncontains a device once Expel confirms no threat is present (applicable only to assets preemptively isolated per customer request).
AI-powered incident narratives
Synthesizes alert details and key findings into a plain-English attack narrative, including detailed close comments for benign alerts.
AI-generated detection rule descriptions
Generates clear descriptions for every security rule to help you understand the specific logic behind each detection.
Real-time automation visibility
Displays the live status and progress of all automated investigation and remediation steps directly within Expel Workbench™.
AI close comment generation
Generates detailed close comments for benign alerts to provide clear context and transparency for security decisions.
Centralized evidence archive
Maintains a complete, auditable history of all chat threads, alert data, and automated Ruxie actions in one centralized incident record.
Automated customer verifications
Generates context-aware prompts asking users to confirm suspicious activity, auto-closing alerts if authorized or escalating if denied.
Bi-directional chat
Syncs Expel Workbench™ investigations directly with Slack and Microsoft Teams, allowing seamless collaboration without switching platforms.
Real-time multi-channel escalation
Pushes instant notifications for high-risk incidents and remediation actions directly to preferred tools.
WHAT CUSTOMERS SAY
The difference is clear to our customers

“Expel’s AI-driven triage system [and SOC team] effectively prioritizes alerts, allowing our analysts to focus on the most critical issues. This has greatly improved our overall operational efficiency.”

“The automation built into Expel takes all the noise, filters and shapes it, and adds context regardless of changes in tools or security architecture.”

“We chose Expel because it instantly multiplied our security operations capacity without adding headcount. When I saw how quickly we could integrate our existing security tools and automate our response capabilities, I knew this would transform how we protect our infrastructure.”
Frequently asked questions
Expel’s AI & automation engine, Ruxie, handles the heavy lifting across the full threat lifecycle—ingesting signals from your security stack, enriching alerts with context, correlating related events, and automating investigations end-to-end for lower-risk findings. Ruxie works with human analysts by providing them a complete picture so they can make faster, better-informed decisions. AI handles speed. Humans handle judgment—no shortcuts.
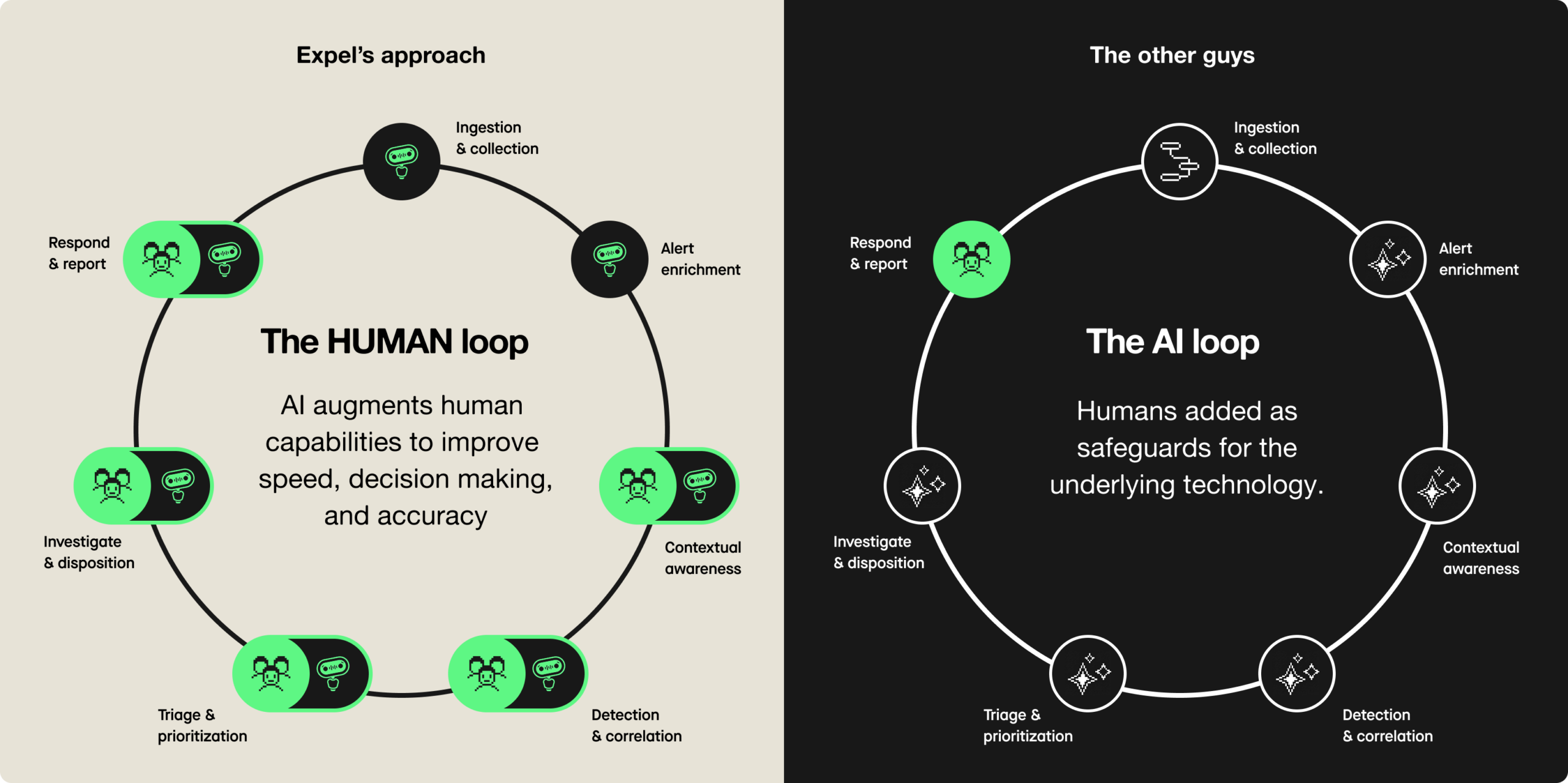
An AI SOC puts autonomous systems in charge of planning, investigating, and responding to threats with minimal human involvement. Some vendors propose replacing human analysts entirely with agentic SOC analysts that can plan, investigate, respond, and adapt autonomously. A human-led SOC flips that model: AI handles the data processing and grunt work, while experienced analysts make every consequential call. In an AI-augmented SOC, human analysts focus on the findings AI surfaces—exercising judgment on threat status, authorizing response, and managing complex investigations that require contextual knowledge and creative thinking. Expel’s approach is the latter: AI as a force multiplier, not a substitute for human expertise.
Agentic AI refers to systems that can autonomously pursue goals, take sequences of actions, and adapt their approach based on feedback, without requiring human direction at each step. In practice, that means an agentic system can receive an alert, query multiple data sources, correlate findings, and produce an investigation summary—all before a human analyst reviews it. The key distinction in responsible deployment is that agentic AI accelerates and informs human decisions rather than replacing them at high-stakes decision points.
AI platforms can process data fast, but they don’t bring context, judgment, or accountability. AI is only useful if you give it the right job to do—it isn’t some mystical force that fixes everything. MDR pairs AI speed with human expertise across the full threat lifecycle: detection, investigation, response, and continuous improvement. Expel’s model is designed with a human in the loop to ensure every investigation our expert SOC analysts close makes the AI smarter and the detections sharper. And unlike typical black-box MDRs, Expel Workbench™ shows AI-driven explanations of every step analysts and bots take. The result is faster outcomes and stronger security posture over time, not just faster alert processing.