Expel Threat Hunting Service
Integrated for cloud, on-prem, and SaaS
Elevate your security: proactive cyber threat hunting mitigates risks.
How we help
Identify silent attacks. Improve visibility across your environment. Strengthen your security posture.
Extend the impact of your security team and optimize your current investments with Expel Managed Detection and Response (MDR), paired with Expel Threat Hunting for better protection across cloud, on-prem, and SaaS environments.
Detect and remediate advanced attacks that slipped past your automated detection tools and identify misconfigurations and gaps in your defensive posture for proactive risk mitigation.
How Expel is different
Hypothesis-based threat hunting across cloud, on-prem, and SaaS
Integrate your tools with our security platform, Expel Workbench™. Benefit from tech-driven automations, expert threat hunting, and hypothesis-based MITRE ATT&CK aligned hunts to uncover missed attacks. Get guidance on fixing gaps for instant defense improvement.
We hunt for unusual logins, patterns, user behaviors, and more, addressing undetected risks across environments. Assess emerging attack impact and enhance defense continuously. Paired with Expel Managed Detection and Response (MDR), you’ll protect your org from existing threats and future vulnerabilities.
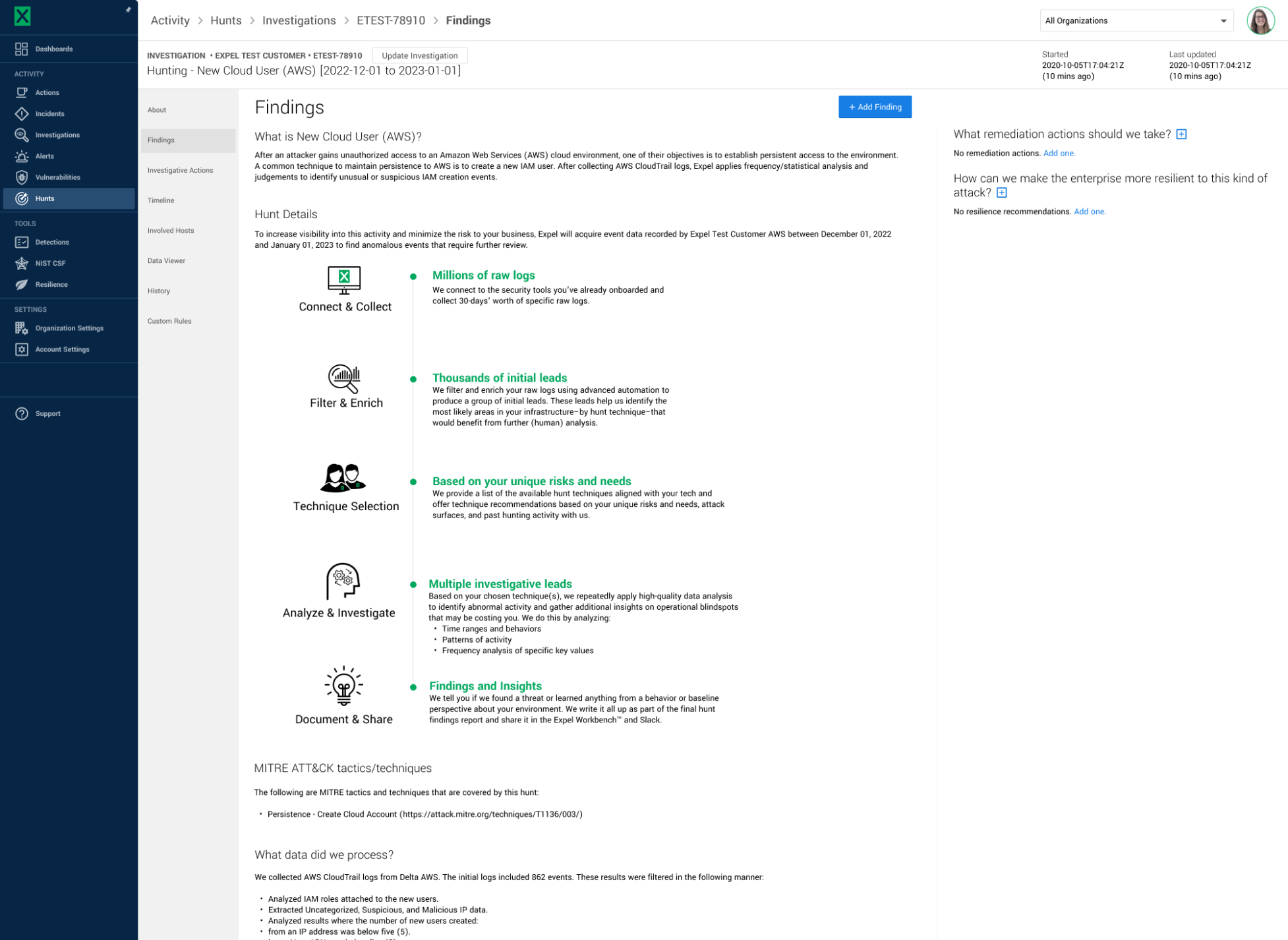
Systematic threat hunting for your security stack
We integrate with your existing security tools and collect 30-days worth of specific raw logs.
Automated filtering and enrichment of raw logs for better insight
Using automation in Expel Workbench™, we produce a group of initial leads targeting specific areas of interest for further hunting and analysis.
Analyzing suspicious activities: unraveling threat patterns
We identify abnormal activity, gather insights on blindspots, and analyze time ranges, behaviors, activity patterns, and more.
Transparent threat reporting and information sharing
Any malicious activity discovered will be instantly routed to our SOC team and yours for immediate response. All hunt findings and gaps uncovered are shared with your team in a monthly report.

What you get
Threat Hunting Service
Monthly hunts on the tools you’ve already invested in, whether it’s on-prem, cloud, or SaaS
Human-led, expert threat hunting assisted by Expel Workbench™ automations to quickly determine potential areas of risk
Hunt techniques aligned to your unique risks and MITRE ATT&CK, spanning from indicators of compromise (IOC) to new cloud user hunts
Clear, consistent guidance on current and future problems areas, so you can build better safeguards
Minimize dwell time and improve security posture with identification of threats that slipped in and immediate response from our MDR team






