WHY EXPEL?
Security without compromise
Experience security operations that’s proactive, resilient, and built to last.
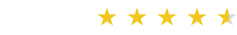
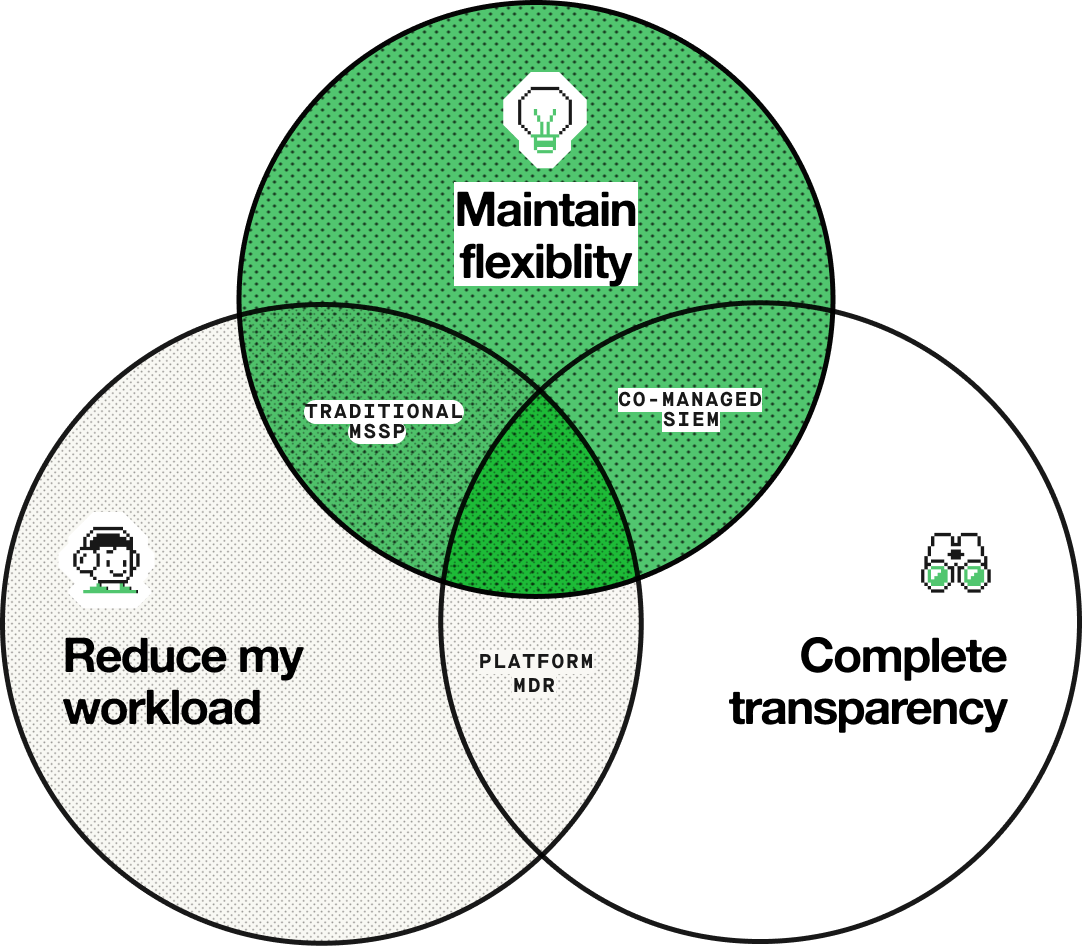
MDR Challenge?
Traditional MDR models force you to choose
Every CISO plays the “pick two” game. Most MDR providers make you sacrifice flexibility for coverage, or transparency for speed.
OUTCOME-FIRST APPROACH
Built for practitioners, not the vendor
Expel is built by practitioners who’ve been in the SOC at 3 AM handling real incidents and know which compromises can break a team.
MDR Challenge?
Traditional MDR models force you to choose
Every CISO plays the “pick two” game. Most MDR providers make you sacrifice flexibility for coverage, or transparency for speed.
OUTCOME-FIRST APPROACH
Built for practitioners, not the vendor
Expel is built by practitioners who’ve been in the SOC at 3 AM handling real incidents and know which compromises can break a team.
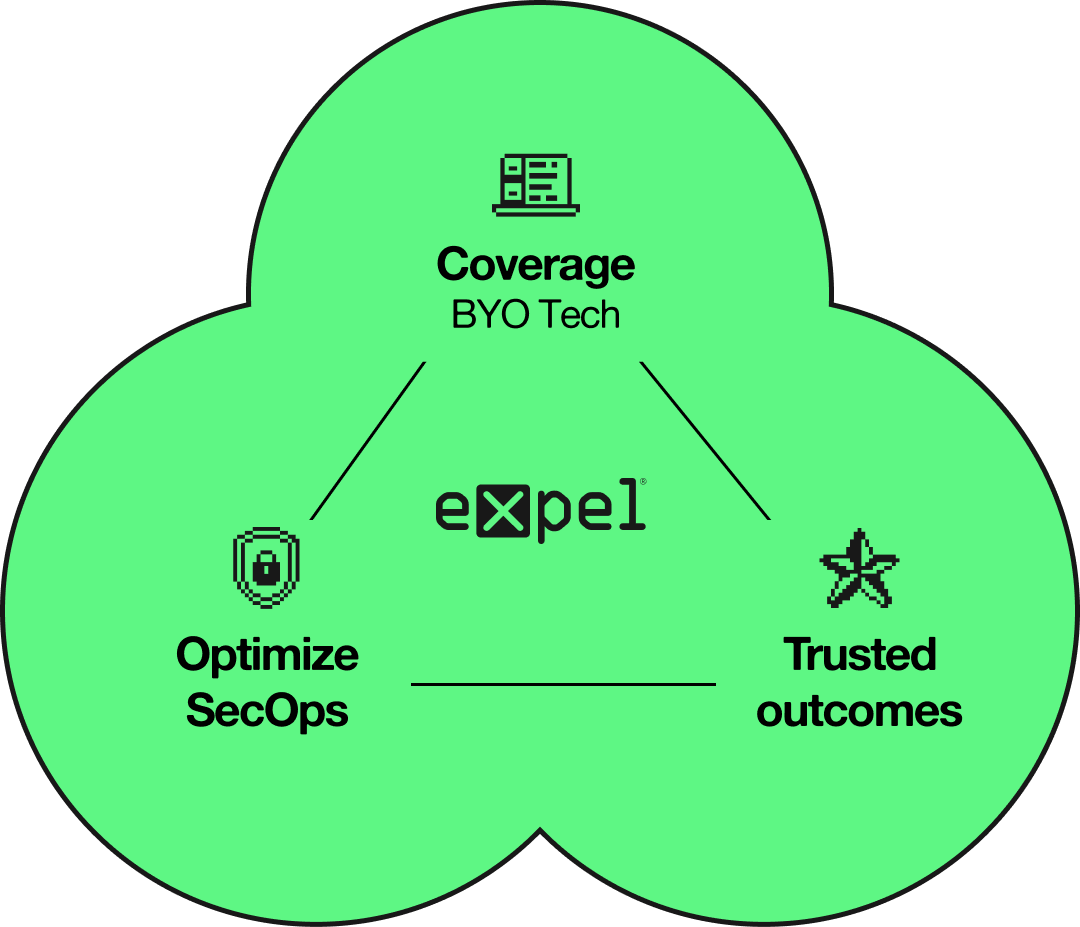
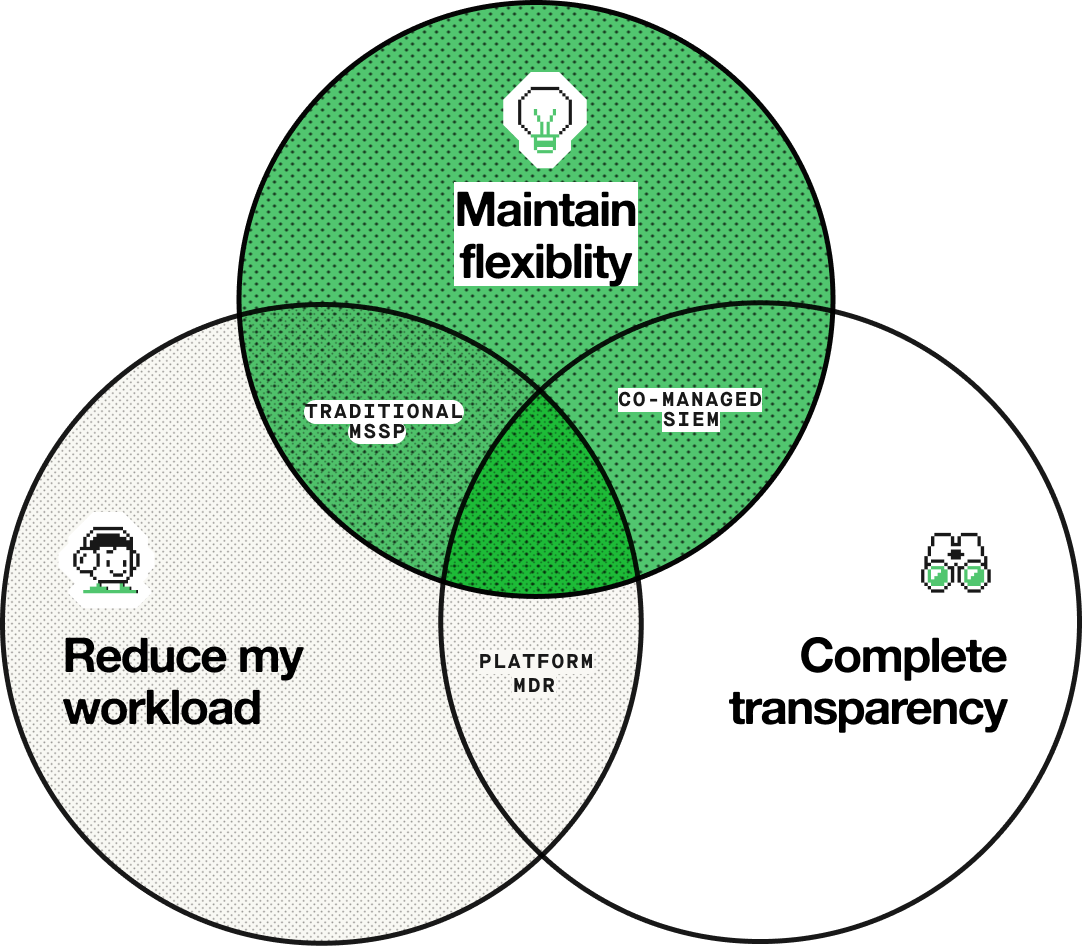
THE EXPEL DIFFERENCE
Security operations built to grow with your program
Your needs change. Expel is constant. Whether you’re building 24x7 coverage or scaling an existing operation, you get the same thing from us: fast detection, faster response.
Analyst Report
Leader in the Forrester Wave™
The only MDR vendor to receive 5 stars in cloud detection in The Forrester Wave™: Managed Detection and Response Services, Q1 2025
By the numbers
Outcomes you can measure
We don't just promise security—we prove it. Here's what Expel delivers: speed to remediate, automation effectiveness, and comprehensive coverage.
14
minute MTTR
on critical/high incidents with auto-remediation
87%
MTTR reduction
with auto-remediation
10
attack surfaces
covered with over 160+ integrations
What Customers Say
Real results from real security teams.
Don’t take our word for it—here’s what happens when security teams partner with practitioners who show their work and deliver on what they promised.

“Expel’s platform has significantly streamlined our security operations. Expel’s AI-driven triage system effectively prioritizes alerts, allowing our analysts to focus on the most critical issues. This has greatly improved our overall operational efficiency.”
“Without Expel, we would have needed to hire at least two or three times our current security engineering team to achieve this centralization.”

“Out of a million events, I would say 99.5% of them are filtered out in triage by AI and machine learning before we actually need to have eyes on the actual issue.”

“Security really is a team sport. With Expel, we have another set of eyes looking at this thing and backing us up. We’re backstopping each other at the end of the day. Because we’re all working from the Expel platform, Workbench, we can collaborate effectively and ensure nothing falls through the cracks.”
INDUSTRY RECOGNITION
Validated by people who understand security.
Forrester does not endorse any company, product, brand, or service included in its research publications and does not advise any person to select the products or services of any company or brand based on the ratings included in such publications. Information is based on the best available resources. Opinions reflect judgment at the time and are subject to change. For more information, read about Forrester’s objectivity here .