Threat hunting
MDR | 3 min read
Four threat hunting fundamentals you need to masterLearn about the four threat hunting basics you need to master to successfully integrate it into your cybersecurity program.
MDR | 7 min read
Gonzo threat hunting: LapDogs & ShortLeashFollow along as a senior detection & response engineer locates threat actors using SOHO devices & ORB networks, Gonzo-style.
MDR | 6 min read
Scaling detection: When 1 + 1 = 3 (grouping IPs to find bad actors across orgs)Here's an overview of how at Expel, we group large data sets via IP information to identify bad actors working across multiple customers.
MDR | 6 min read
15 criteria Expel rocked a 5/5 score in The Forrester Wave™: MDR Services, Q1 2025Enjoy this complimentary playlist while diving into the fifteen reasons why Expel is the best option when it comes to MDR cloud providers.
Rapid response | 2 min read
Security alert: IngressNightmare (NGINX controller for Kubernetes)On March 24, 2025, five vulnerabilities in the Ingress NGINX controller for Kubernetes were publicly disclosed. Here's how to remediate.
Product | 2 min read
Expel MDR customers benefit from expanded threat intel experienceThreat Bulletins are now available in Expel Workbench™, including details on any threat hunting completed to resolve the issue.
Data & research | 2 min read
It’s here: Expel’s 2025 Annual Threat ReportThis year’s Annual Threat Report describes the major attack trends we saw last year, advice to safeguard your org, and predictions for 2025.
Product | 3 min read
Expel MDR has new advanced identity threat detection & responseExpel MDR's new auto remediation feature makes it easier to fix credential compromises in common tools, like Okta. Learn more.
MDR | 3 min read
Let your security maturity be your guideSecurity maturity is critical in determining your SecOps strategy. Learn how an Expel customer determined it was time to add threat hunting.
Data & research | 3 min read
Expel 2023 Q3 Quarterly Threat Report: the top five findingsThe 2023 Q3 Quarterly Threat Report findings are based on incidents our SOC identified. Here are a few of the top trends.
MDR | 3 min read
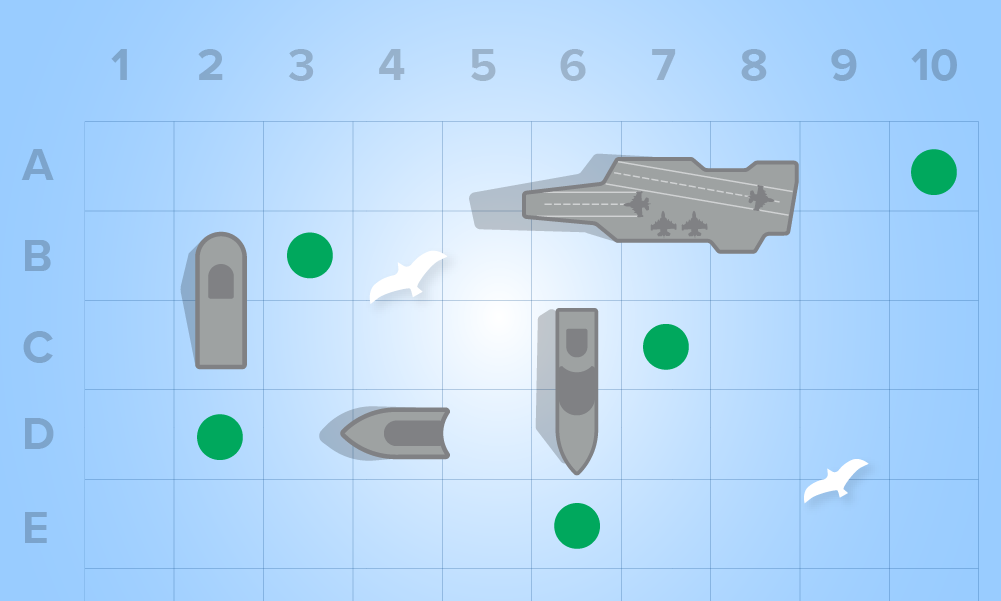
Hypothesis-based threat hunting: the what, why, and howYour threat hunting program should focus on TTPs, holes, and areas of concern around your security posture and create hunts to probe those areas.
MDR | 2 min read
Threat hunting basics: understanding key principlesThreat hunting basics—continuous monitoring, intel-driven, hypothesis testing, and collaboration—help you detect and smother threats faster.
MDR | 2 min read
Threat hunting complements MDR for a stronger defensive strategyLearn how an elite MDR operation works with threat hunting to rapidly uncover critical insights and stop threats faster.
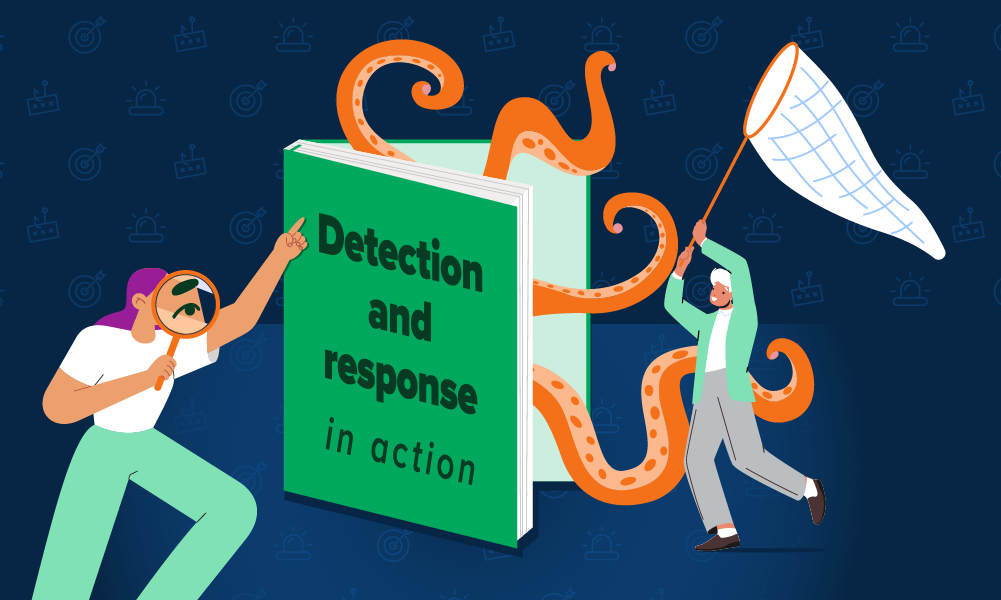
MDR | 12 min read
Detection and response in action: an end-to-end coverage storyThis dramatized case study illustrates how our MDR, phishing, and threat hunting services work, and most importantly, how they work together.
MDR | 5 min read
Threat hunting: Build or buy?Should you build your own threat hunting capability or get a partner? This post breaks down your options and the crucial cost considerations.
Product | 6 min read
Performance metrics, part 3: Success storiesReduce analyst burnout! Get our SOC team's success stories on creating efficiency and download a resource to measure performance.
Product | 3 min read
Expel Hunting: Now in the cloudWorried about cloud visibility gaps? Expel Hunting now features new cloud hunts to help you spot blind spots and secure your environment.
MDR | 4 min read
3 must-dos when you’re starting a threat hunting programSo you decided you want to build a threat hunting program...but where do you start? Here are our three must-dos when you’re planning your hunt.
MDR | 6 min read
How to find anomalous process relationships in threat huntingFinding anomalous process relationships--commands that don’t belong together--might indicate a problem within your environment. Here’s how to spot ‘em.
MDR | 7 min read
How to choose the right security tech for threat huntingDeciding which tech to use for your threat hunt? Get pro tips on when and how to use different security technologies for your mission.
MDR | 5 min read
What is (cyber) threat hunting and where do you start?What is cyber threat hunting? Learn how cyber hunting differs from alert management, and where to start building an effective cyber threat hunting program.