Our security operations center (SOC) sees its share of attackers in Google Cloud. Seriously—check out this recent incident report to see what we mean.
Attackers commonly gain unauthorized access to a customer’s cloud environment through misconfigurations and long-lived credentials—100% of cloud incidents we identified in the first quarter of 2022 stemmed from this root cause.
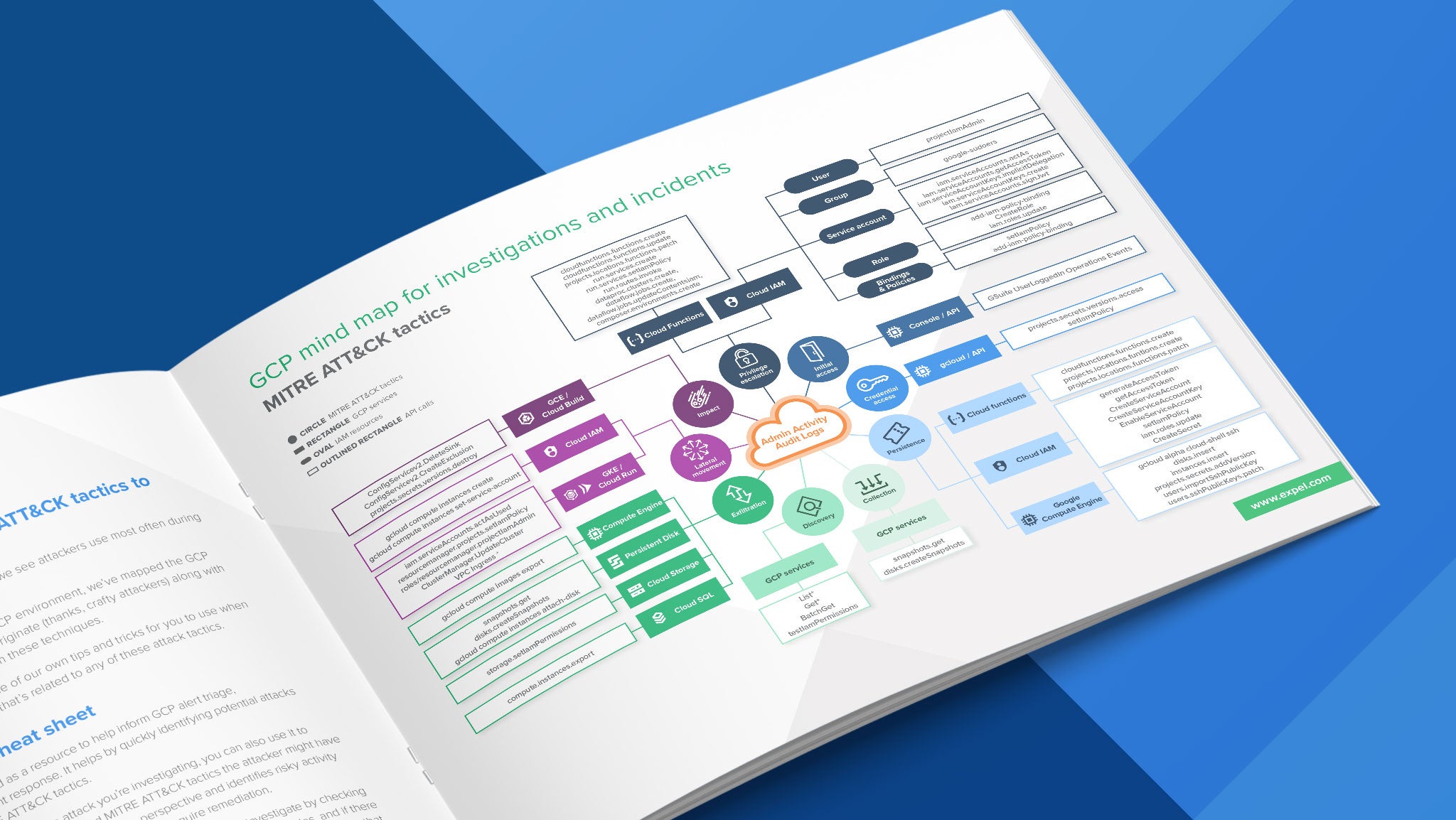
As we investigated these incidents, we noticed patterns emerge in the tactics attackers use most often in Google Cloud. We also noticed those patterns map nicely to the MITRE ATT&CK Framework… (See where we’re going with this?)
Cue: our new defender’s cheat sheet to MITRE ATT&CK in Google Cloud.
What’s inside?
In this handy guide, we mapped the Google Cloud services where these common tactics often originate to the API calls they make to execute on these techniques, giving you a head start on protecting your own Google Cloud environment.
We also sprinkled in a few tips and tricks to help you investigate incidents in Google Cloud. It’s an easy-to-use resource that informs your organization’s Google Cloud alert triage, investigations, and incident response.
Our goal? Help you identify potential attacks and quickly map them to ATT&CK tactics by providing the lessons learned and takeaways from our own investigations.
Depending on which phase of an attack you’re investigating, you can also use the cheat sheet to identify other potential attack paths and tactics the cyber criminal used, painting a bigger (clearer) picture of any risky activity and behaviors that can indicate compromise and require remediation.
For example, if you see suspected credential access, you can investigate by checking how that identity authenticated to Google Cloud, if they’ve assumed any other roles, and if there are other suspicious API calls indicating the presence of an attacker. Other tactics that an attacker may execute prior to credential access include discovery, persistence, and privilege escalation.
What’s the bottom line?
Chasing down Google Cloud alerts and combing through audit logs isn’t easy if you don’t know what to look for (and even if you do).
Full disclosure: the cheat sheet doesn’t cover every API call and the associated ATT&CK tactic. But it can serve as a resource during incident response and help you tell the story (to your team and customers) after the fact.
Knowing which API calls are associated with which attack tactics isn’t intuitive, and we don’t think you should have to go it alone. We hope this guide serves as a helpful tool as you and your team tackle Google Cloud incident investigations.
Want a defender’s cheat sheet of your own? Click here to get our GCP mind map!
P.S. Operating in Amazon Web Services (AWS) or Azure too? We didn’t forget about you—check out this AWS Mind Map and Azure Guidebook for more helpful guidance.
Special thanks to Ryan Gott for his contributions to this defender’s cheat sheet and mind map.