Last (but certainly not least) in our Q1 Quarterly Threat Report (QTR) blog series, we dig into vulnerability exploitation—a continuous, serious risk for organizations. Identifying and patching vulnerabilities is an onerous task for many security teams, and knowing which vulnerabilities to prioritize to reduce risk can be even more daunting.
In 2024, our security operations center (SOC) team has already seen 20 severe vulnerabilities identified and exploited. This quarter, we shine a light on the most dangerous: authentication bypass vulnerabilities.
Keeping patched and keeping secure
Authentication bypass vulnerabilities are weaknesses in the software design, allowing an attacker to circumvent normal authentication to access the software or device. This type of vulnerability can result in full application compromise and put the rest of the network at risk. This attacker activity is incredibly risky and difficult to detect because the attacker can leverage the normal functions of the application and hide behind an activity resembling ordinary usage.
Table 1: A sample listing of exploited critical vulnerabilities we observed this quarter
| CVE number | CVE name | CVSS score | EPSS score Exploitation probability |
| CVE-2023-46805 | Authentication Bypass Ivanti ICS and Ivanti Policy Secure | 8.2 | 96% |
| CVE-2024-1709 | Authentication Bypass ConnectWise | 10 | 93% |
| CVE-2024-27198 | Authentication Bypass JetBrains TeamCity | 9.8% | 97% |
The best approach to defend against these attacks is to limit external connectivity to systems in accordance with security best practices. Here’s how to be more proactive in identifying potential attack surfaces in your network.
How to protect your org:
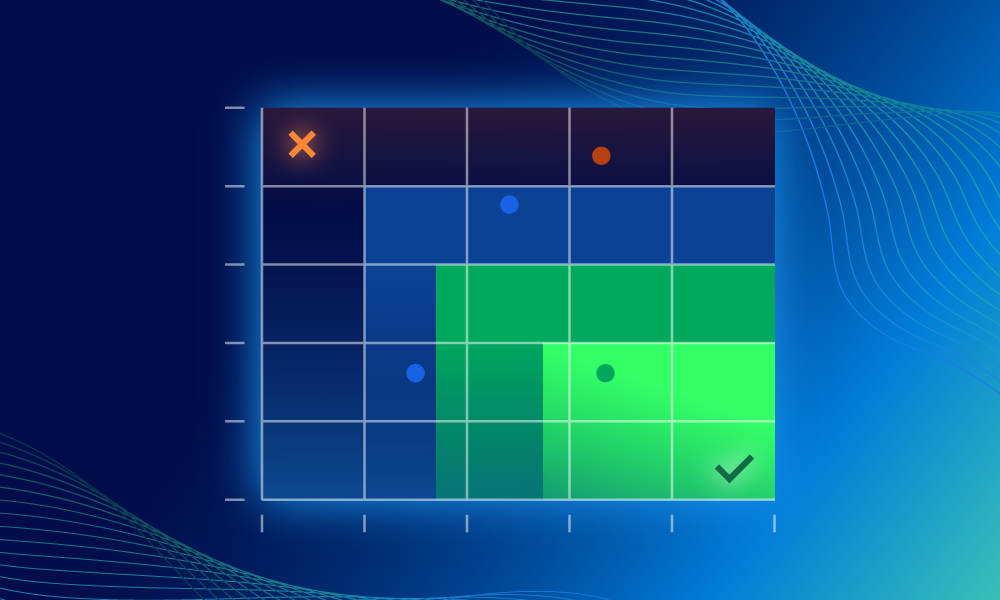
First, ensure your organizational asset management (ASM) is effectively maintained and accurately capturing asset inventories (i.e., adding new or removing decommissioned assets), as business needs evolve. Then, pivot to your vulnerability management (VM) scanning technology, so every asset is accurately risk assessed. VM technology must be configured to either frequently scan (subnet ranges) or install VM agents in your environment. Ask: does your scanning tool have complete visibility to your infrastructure’s assets?
Are your essential business applications also identified and scanned for vulnerabilities? If scanning technology discovers high-risk vulnerabilities on your assets and applications, does your organization have sufficient resources allocated to track the remediation and completion status?
Second, where possible, we recommend defining processes for monitoring assets (e.g., servers and endpoint devices) to ensure system and application logs are forwarded to a designated repository for retention and review. This helps to ensure logs can be monitored and are available in the event that the assets are compromised.
Finally, ensure your scanning practices include identifying any unmanaged devices on your networks too. Unmanaged devices continue to be a significant security risk because patching and monitoring the device is outside of your organization’s control, or it might conflict with established contractual obligations. It’s common for cybersecurity incidents to originate from vendors’ or users’ devices, which aren’t always kept up to the same standard as the rest of the organization. Consider leveraging your scanning tool’s ‘tagging’ structure to assign details such as: ownership (individual or group), locations, criticality, and/or custom labeling to address visibility gaps.
(And for what it’s worth, if the sheer number of vulnerabilities overwhelms your team, the Expel Vulnerability Prioritization solution can help sift through alerts, automatically surfacing the highest-risk vulnerabilities to help teams focus on the threats that matter most.)
That’s a wrap on Q1
One quarter into 2024 and our predictions are (unfortunately) ringing true. Already, threat actors are leveraging AI for social engineering attacks, enhanced spearphishing, and misinformation spreading. Notably, Deepfakes are making their way out of sci-fi and into the mainstream (for attackers, anyway). We expect all of the above to increase tenfold as we barrel toward the 2024 U.S. Presidential Election cycle.
But be wary of flashy headlines that distract from the threats of the past. Attackers are also sticking to the tried-and-true, and for good reason: it works. Malware dropper sites, MFA bypass, fudging geolocations with VPS, VPNs and TOR routing—all proven methods that may increase in complexity, but remain fundamentally the same.
Despite the doom and gloom, there’s hope. Just as attackers take advantage of emerging technologies, so do we. With the increased push for incident disclosures from government entities (recent SEC mandates in the U.S.; upcoming DORA regulations in the U.K.), the opportunity for information sharing among operators is encouraging. Exchanging knowledge and lessons-learned will only make us stronger as a defender community, and despite the threats of today, we’re optimistic for tomorrow.
That’s all for Q1 2024. Stay tuned for next quarter, as we continue to track data, identify patterns, and share insights to help you and your org stay protected. Questions about this series or just want to chat? Give us a shout.
Q1 QTR series quick links
Check out the other blogs in the series for more of our Q1 findings: