Cloud security
Cloud security | 2 min read
Cloud Decoded (part 3): Hey CISOs, stop guessing when it comes to cloud securityPart three of our Cloud Decoded blog series focuses on what you need to know about cloud detection and response (CDR).
Cloud security | 3 min read
Cloud Decoded (part 2): What attackers don’t want you to knowThis is part two of Expel's blog series on decoding the cloud. It dives in to what attackers don't want you to know.
Cloud security | 4 min read
Cloud Decoded (part 1): The cloud security mythbuster—what MDR really means for cloudThis is part one of Expel's blog series on decoding the cloud. The first one covers what MDR really means for cloud.
Cloud security | 3 min read
Comparison of cloud resources (part IV): Making a roadmap for cloud securityThis is part four of our four-part blog series on comparing cloud resources. Part four covers the roadmap for cloud security.
Cloud security | 14 min read
Comparison of cloud resources (part III): Demystifying cloud security tools in the platform and application layerThis is part three of our four-part blog series on comparing cloud resources. Part three defines tools used in the platform and app layers.
Cloud security | 8 min read
Comparison of cloud resources (part II): Demystifying cloud security toolsThis is part two of our four-part blog series on comparing cloud resources. Part two defines the types of tools used for cloud security.
Cloud security | 5 min read
Comparison of cloud resources (part I): Securing every layer of your cloud—from the control plane to appsThis is part one of our four-part blog series on comparing cloud resources. Part one covers the layers of the cloud infrastructure.
Cloud security | 9 min read
Vulnerability management for cloud environmentsVulnerability management in the cloud has its own unique challenges and strategies. Dive into the nuances and how Expel can help.
Cloud security | 8 min read
Cloud security: alert best practices (part II)This is part two of a two-part blog on cloud security alerts, including what makes them unique and best practices for management.
Cloud security | 8 min read
Cloud security: alerts vs. on-prem alerts (part I)This is part one of a two-part blog on cloud security alerts, including what makes them unique and best practices for management.
Cloud security | 6 min read
Part II: Fundamentals of Kubernetes securityLearn about the fundamentals of Kubernetes, including the four Cs of Kubernetes security and how Expel can help protect it.
Cloud security | 8 min read
Part I: Fundamentals of Kubernetes securityLearn about the fundamentals of Kubernetes, including its architecture, challenges, and false positives in part one of this two-part blog series.
Cloud security | 3 min read
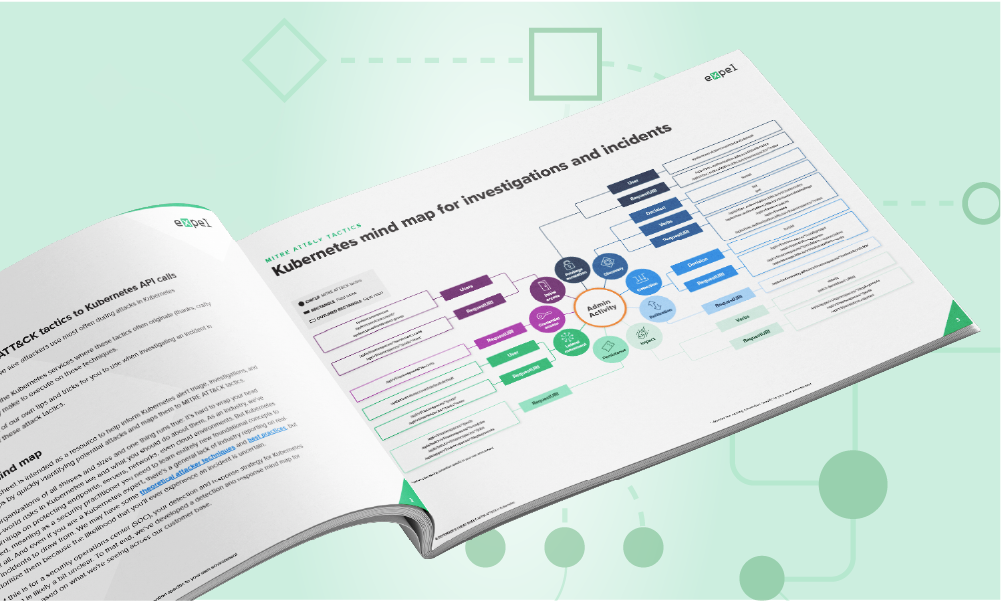
New mind maps & cheat sheets: Azure & KubernetesOur new Kubernetes mind map/cheat sheet show you which API calls are associated with different MITRE ATT&CK tactics in K8 environments.
Cloud security | 3 min read
Cloud repatriation and cybersecurity challengesMany factors influence the decision to move data back on prem. Organizations must plan for security both during and after the move.
Cloud security | 3 min read
Staff, C-suite disagree on how security drives innovationThis 2023 CSA research report found that the C-suite and security staff are disconnected on the role security plays in innovation.
Cloud security | 3 min read
In the age of innovation, does security hold the key?A new report by the CSA showcases the results of research on getting a deeper understanding of areas of innovation and cloud use trends.
Cloud security | 3 min read
Kubernetes security checklist: what to look forLearn what to look for and get key suggestions for your future security strategy and tools with this Kubernetes security checklist.
Cloud security | 3 min read
Why MDR is great news for securing Kubernetes environmentsThis post discusses how managed detection and response (MDR) f helps organizations in securing Kubernetes environments.
Cloud security | 1 min read
Understanding the 3 Classes of Kubernetes RiskThe first step toward securing Kubernetes environments is understanding the risks they pose and identifying the ways in which those risks can be mitigated.
Cloud security | 2 min read
Tell Dr. Kubernetes where it hurtsKubernetes is growing fast, but so are its challenges. Get part 1 of our series, where we outline the most common hurdles you'll face.
Cloud security | 7 min read
Five common multi-cloud security challengesSwitching to multi-cloud is hard. An Expel engineer shares what you need to think about and how to stay sane during the transition.
Cloud security | 4 min read
Dr. Strangelog or: How I learned to stop worrying and love alertsHigher-fidelity data leads to better security alerts. Our advanced tech embeds more context and stability to provide more refined security signals.
Cloud security | 5 min read
Understanding role-based access control in KubernetesUnderstanding authorization is critical to securing Kubernetes. Learn how RBAC works and the rules that govern your access control.
Cloud security | 3 min read
Three Kubernetes events worth investigatingMonitoring your Kubernetes environment? Learn what to look for and how to use audit logs to secure your production workloads.
Cloud security | 3 min read
Kubernetes: the whale in the roomMore than half of our cloud customers use Kubernetes (k8s) to ship software faster and cut costs with elastic infrastructure.
Cloud security | 2 min read
A defender’s MITRE ATT&CK cheat sheet for Google CloudGet a head start on security. Our new guide maps GCP incident patterns to the MITRE ATT&CK Framework to help protect your organization.
Cloud security | 3 min read
GCP Incident report: Spotting an attacker in Google CloudOur guide details a GCP incident, from initial attacker access to resolution. Learn our key takeaways for securing your cloud environment.
Cloud security | 3 min read
5 pro tips for detecting in AWSCloud security is complex, but start with the basics. Get pro tips to help focus your lens for detecting threats in AWS effectively.
Cloud security | 4 min read
Attack trend alert: AWS-themed credential phishing techniqueAttackers are phishing with fake AWS log-in pages. See how our crew identified and triaged a malicious email to protect a customer.
Cloud security | 6 min read
How Expel goes detection sprinting in Google CloudBuilding detections in GCP? Our engineers demystify the process for you. Learn how to get strategic with your cloud detection and response.
Cloud security | 7 min read
Cloud attack trends: What you need to know and how to stay resilientTop pandemic attack trends are here. Learn how to remediate and use our crew’s tips to build resilience against these attacks.
Cloud security | 11 min read
Migrating to GKE: Preemptible nodes and making space for the Chaos MonkeysSee how Expel's internal teams migrated our core infrastructure to GCP with zero downtime. Learn the strategy behind the successful move.
Cloud security | 6 min read
5 best practices to get to production readiness with Hashicorp Vault in KubernetesFlying blind running Hashicorp Vault in Kubernetes? Get the best practices and tips to accelerate production without compromising on security.
Cloud security | 12 min read
Behind the scenes: Building Azure integrations for ASC alertsWe built a new detection strategy for ASC! Learn how Expel's teams integrated with Azure signal to provide more alert context and visibility.
Cloud security | 1 min read
Got workloads in Microsoft Azure? Read thisGot Microsoft Azure? Running Microsoft products in your org? Then you might want to get a free copy of our all-new Azure guidebook.
Cloud security | 6 min read
Supply chain attack prevention: Three things to do nowCan’t trust the internet? Supply chain attacks like SolarWinds are not new. Get actionable tips to prepare and guard against similar attacks.
Cloud security | 6 min read
Evilginx-ing into the cloud: How we detected a red team attack in AWSSee how we defeated a red team attack in AWS! We detail our defense strategy using open source tools and share tips to protect your org.
Cloud security | 2 min read
Introducing a mind map for AWS investigationsInvestigating in AWS? We created a mind map using CloudTrail insights to help your team. Check out this essential AWS security resource.
Cloud security | 8 min read
Terraforming a better engineering experience with AtlantisMake cloud provisioning easy. Learn how Expel leveraged Terraform and Atlantis to build a platform for simple, self-service infrastructure.
Cloud security | 8 min read
Behind the scenes in the Expel SOC: Alert-to-fix in AWSWonder what cloud investigation looks like? See how our team foiled a real-life coin-mining attack in AWS, from alert to fix.
Cloud security | 8 min read
Why the cloud is probably more secure than your on-prem environmentIs on-prem safer? Probably not. Get 5 reasons why the cloud offers better security than your on-prem environment.
Cloud security | 5 min read
Making sense of Amazon GuardDuty alertsRunning AWS workloads? You need GuardDuty. Get our pro tips on what it is and how to make sense of all its security signals.
Cloud security | 5 min read
MFA is not a silver bullet to secure your cloud emailLearn how dual or multi-factor authentication (MFA) are not an entirely secure solution for cloud email security on the Expel blog.
Cloud security | 7 min read
Generate Strong Security Signals with Sumo Logic & AWS CloudtrailLooking to get more or better security signals from AWS Cloudtrail? Learn how with Expel.io. See how we use the Sumo Logic SIEM for actionable data.
Cloud security | 5 min read
This is how you should be thinking about cloud security challengesModern IT isn't about servers—it's cloud. Get our pro tips for easily cracking the cloud security code and modernizing your defense.
Cloud security | 7 min read
How to build a useful (and entertaining) threat emulation exercise for AWSWant to test your analysts’ detection skills in the cloud? Here are our tips and tricks for building your own threat emulation exercise in AWS.
Cloud security | 8 min read
How to find Amazon S3 bucket misconfigurations and fix them ASAPWhy do Amazon S3 bucket breaches happen? Get the AWS pro tips you need to protect your org from making this costly mistake.
Cloud security | 3 min read
Three tips for getting started with cloud application securityIf you're feeling like your SaaS security knowledge is a bit cloudy, these three pro tips will get you started on the right path.
Cloud security | 7 min read
Getting a grip on your cloud security strategyCloud security is different. Get three key points from Expel that should inform and improve your modern cloud strategy.
Cloud security | 12 min read
A common sense approach for assessing third-party riskWalk through our lightweight third-party assessment process. Download the exact questionnaire and emails we use to vet vendors now.