Identity-based attacks remain the top threat; session cookie theft on the rise; hackers continue to exploit known software vulnerabilities.
Attention citizens of Troy:
The Greek invaders may attempt to infiltrate our city by building a great phish and hiding men inside it.
If you see a giant wooden phish:
- Report it to the nearest city guard immediately
- Do not, under any circumstances, open the gates and bring it inside
The ancient Greeks would have had a much harder time infiltrating the infrastructure of ancient Troy had the city’s fine citizens had access to the sort of intelligence and education available to organizations like yours.
Alas, the Trojans had no Quarterly Threat Report (QTR). You do, though, and the data and insights from our Q1 iteration—published today—detail the attacks we’re seeing, how to spot them, and, most importantly, how you can protect your organization.
Hackers sometimes innovate something completely new, but recent QTRs and our 2023 Great eXpeltations annual report make clear that they prefer the tried and true. As long as existing methods work, they’re satisfied with the same-old-same-old. And too many of the existing methods still work.
Here are some of the Q1 QTR’s top findings.
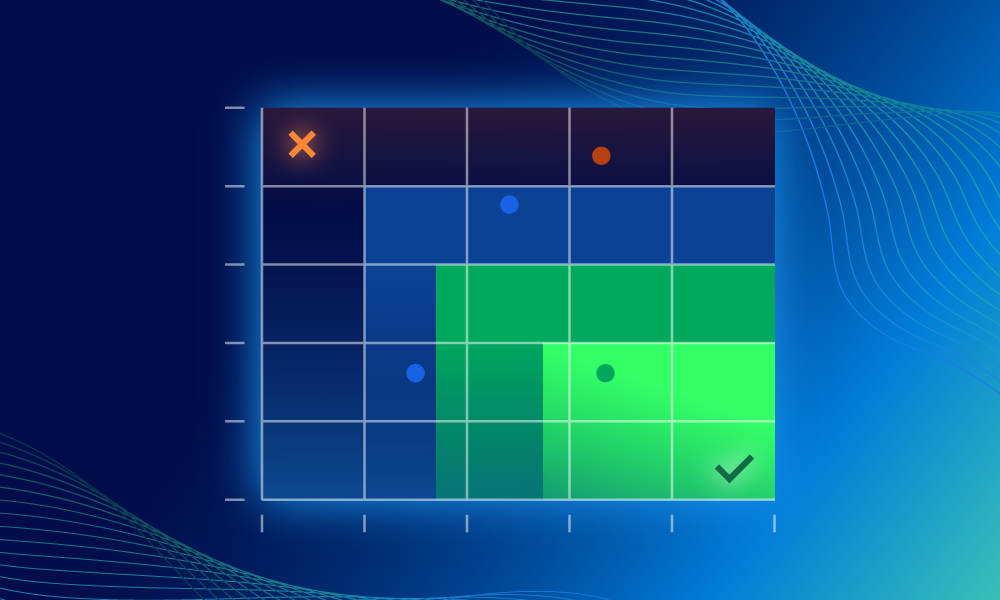
1: Identity-based attacks remain the top threat. Account compromise, account takeover (ATO), and long-lived access key theft accounted for 57% of all incidents identified by our SOC.
You’ve probably heard that “identity is the new endpoint,” and it’s truer now than ever: attackers attempting to access a user’s identity to perpetuate fraud is the predominant threat our SOC sees (time and time and time again). Account compromise and account takeover in Microsoft 365 (M365) accounted for 50% of all incidents.
2: We see more theft of session cookies. Attackers bypassed multi-factor authentication (MFA) in popular SaaS applications like Okta and M365 by stealing session cookies, launching MFA fatigue attacks, registering malicious OAuth applications, and authenticating using legacy protocols. We saw a particular increase when it comes to session cookie theft in M365.
3: Old vulnerabilities remain, well, vulnerable. While we saw the exploitation of a software vulnerability to gain initial access in only a small percentage of Q1 incidents, hackers tended to exploit one- to two-year-old vulnerabilities. This suggests organizations don’t know which vulnerabilities pose the biggest threats to their environments. Pro tip: vulnerability prioritization can help.
Also, there’s some bonus good news: the median alert-to-fix time for critical incidents our SOC handled in Q1 was 21 minutes—one minute faster than Q4 2022. (👍)
Like the legendary Trojan Phish, identity attacks, ATOs, cookie theft, and the other tactics described in this QTR work reliably—unless the targets are informed and vigilant. In that case, the attacks don’t work so well.
This is great for us metaphorical citizens of modern Troy. We have access to lots of tools and resources, and none is more powerful than education. An informed digital workforce is a hacker’s worst nightmare.
We encourage you to download the QTR and give it a few minutes of your time. If you have questions or comments, drop us a line.