TL;DR
- Co-managed SIEM promises transparency and control, but usually just adds coordination overhead—the “too many cooks” problem is real and persistent.
- The technology has improved since 2020, but the core challenges (role confusion, internal resource burden, detection gaps outside the SIEM) haven’t gone away.
- For most teams without dedicated SIEM expertise, managed SIEM or MDR will deliver better outcomes with less friction.
Maybe you’ve already got a SIEM and you’re looking for help managing it. Maybe you’re thinking of buying a SIEM and concerned it might be too much to handle on your own. Or maybe you’re using an MSSP and thinking of gaining more control of your data by working collaboratively in your SIEM rather than letting them do all the work.
However you’ve arrived at the concept of co-managed SIEM, there are a number of potential pros and cons to consider when making your decision.
It’s important to really understand what you’re going to get out of a co-managed SIEM—it’s a big resource and dollar commitment, and mistakes made early on can take a long time to correct.
Our team encounters a lot of co-managed SIEM myths, and in this post I’ll share the most common ones, along with our perspective on the actual realities.
First, here’s a general idea of how we might assign roles at Expel:
| Roles and responsibilities with third-party security partner |
|---|
| Responsibility | Co-Managed SIEM | Expel |
|---|---|---|
| System upgrades | Provider | You |
| Log source onboarding | Both | You |
| Health monitoring | Both | Expel |
| Rule management | Both | Expel |
| Alert triage & investigation | Both | Expel |
| Reporting | Both | Expel |
| Remediation | You | You |
What are the perceived benefits of co-managed SIEM—and what’s the reality?
Myth: It’s the only way to get transparency.
One of the biggest benefits people want from co-managed SIEM is visibility into their security operations. By working with a partner in your SIEM, you maintain some control over the detection rules that are in place, the sources of data and what your analysts are doing (regardless of whether they’re YOUR analysts or your partner’s analysts).
Reality: There are other (better) ways to get transparency.
We strongly believe that you can’t build trust without transparency. It’s key to being a good partner to our customers. It’s also vital for efficiency and accuracy. So we’ve put a lot of thought into what transparency should look like in practice.
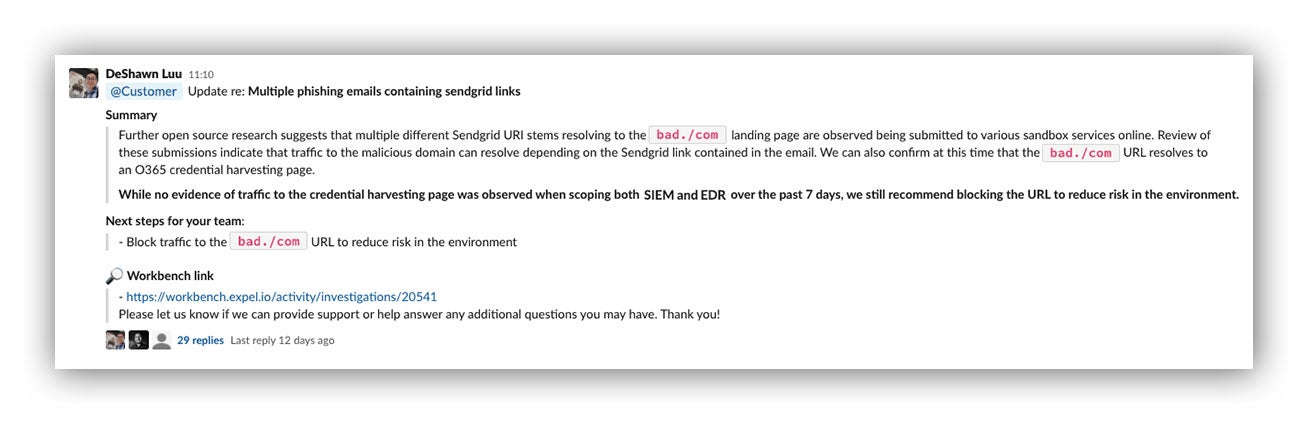
At Expel, we provide our customers with complete visibility into our analysis and investigations—in fact, we invite all our customers to watch what we’re doing in Expel Workbench or talk with us in a dedicated Slack channel as an incident unfolds. We literally work alongside your analysts to prosecute events and respond to incidents.
Example conversation in Expel’s customer Slack channel
Further, you can review all activity to check our work—make sure you agree with what we’ve done and help improve detection and response capability.
We want all third-party security providers to be held to the same account, since this is what we’d expect from any MSSP we deal with (we’re a customer of ourselves, so it works out great for us).
Myth: Greater control over business logic produces more detection value.
Your SIEM is the codification of business logic you use to detect specific threats inside your organization. Custom rules and configurations allow you to look for attacks tailored to your systems and architectures. A co-managed SIEM allows you to continue to maintain this business logic.
Reality: The vast majority of what you detect is the same as your peers and many other companies.
Orgs think they want more control to write rules and generate alerts, but they don’t realize how much it costs to manage detection content. Unless you invest a lot in this area, you’ll end up with a pile of false positives.
In reality, your rules probably aren’t as unique as you think. Your provider has an advantage since it sees the big picture (aka lots of customers) and has the expertise to manage the detection content. If you’re already running a SIEM, working with a provider who can help you optimize your SIEM is often more impactful than trying to co-manage detection rules yourself.
However…
You should expect your security provider to tailor their detection strategy for you to your business. This could mean fine-tuning rules that already exist, taking advantage of rules you’ve written in your SIEM or working together to build new rules in our platform.
Have a suggestion? No problem. Just let us know and we’ll work to understand the use case and ensure you’re covered. No matter what security provider you work with, once you share your suggestion they should do the rest.
Myth: You’ll get assistance from outside experts.
By going to a co-managed SIEM, you’re hoping to take advantage of the collective knowledge from your service providers. Presumably your provider has seen lots of good and bad and can advise you and your team on doing SIEM better. You’d also think that they will answer general security questions and concerns you may have.
Reality: You should expect this assistance from your third-party security partners.
Once again, your third-party security partner shouldn’t just process alerts. MSSPs have lots of institutional knowledge they can share to help improve your broader security program. We work to push as much information to our customers (and publicly) as we can to help everyone make their organizations more secure. Further, our engagement managers are a window into Expel that can get you answers to tough security questions.
Myth: My SIEM will have all of the data required for detection and response.
Many organizations envision their SIEM as the single place where all data exists for detection and investigation. Thinking about co-managed SIEM as a strategy doubles down on this assumption as you’re paying for a provider to help manage that signal and detection content. The hope is that your SIEM will provide visibility across the entire environment and enable your team to respond to all kinds of threats.
Reality: Storing data in a SIEM is a lot of work.
Getting all the data that you want into a SIEM can be an exhausting process. And making sure it continues to go into a SIEM isn’t much easier.
We’ve built API integrations with more than 100 different vendors. We learned pretty quickly that data sent to a SIEM isn’t nearly as rich as data that can be pulled from an API, which can inhibit detection and response with a SIEM. That’s one reason why managed detection and response services that connect directly to data sources often outperform co-managed SIEM setups, particularly in cloud-heavy environments.
As organizations increasingly use cloud applications and infrastructure, the vision of the SIEM as a single source of truth starts to make less sense. So it’s important to evaluate why you need (or think you need) a SIEM. There will be instances when sending your data to a SIEM is a wise choice. But, for example, you don’t need to store those Office 365 or AWS logs in your SIEM when your cloud provider is already storing them for you and your MSSP can consume them directly.
That’s why we connect directly to cloud providers—meaning that regardless of the choice you make, you’ll always get the visibility you need.
And the reality that’s all too familiar …
This is a big one.
It’s “too many cooks in the kitchen.”
One of the problems with a co-managed SIEM is orchestrating who is doing what.
A SIEM is a big piece of technology and dividing up responsibilities can be confusing. Who handles upgrades? Who’s responsible for rule QA? Who handles device integration? How about analyst shifts?
If the answer is “it depends”—expect friction.
By having a third-party security partner rather than a co-managed SIEM, the roles are clearer for both your staff and the service provider. Avoiding confusion at this stage helps ensure you’re focused on the right issues (like generating good signal, minimizing noise and detecting bad actions) and not wasting time on RACI charts and scheduling.
So when does a SIEM actually make sense?
SIEMs can be a valuable part of an organization’s security architecture. When properly fed, they’re the source of truth for an investigation. The information and analytical capability in your SIEM can be invaluable for analysts and investigators when working through the trail of alerts and data involved with suspicious activity.
Further, SIEMs are great data normalizers. Taking in unstructured data, providing structure and storing it all in an orderly way can open up many more opportunities for signal generation in your company. Data that might otherwise go ignored can be put to great use in your SIEM.
Finally, they’re great tools for your analysts. From experimentation to ongoing operations, a good SIEM and staff that know how to use them can fulfill their promise, serving as a focal point for your security operations.
However, even the best SIEM needs people.
If you don’t have in-house expertise and are thinking about co-managed SIEM as an option, consider these common myths and what you could accomplish by asking more of your third-party security partner.
Myth: Co-managed SIEM has evolved enough to solve the original problems.
A lot has changed since this post was first written in 2020. Bring-your-own-SIEM (BYOS) models have given organizations more flexibility. Tooling has improved. Pricing has become more transparent. If you looked at co-managed SIEM back then and passed, the argument goes, it might be worth a second look now.
Reality: Some things have genuinely improved, but the core problems haven’t gone away.
Let’s be honest about what’s better. BYOS models have made it easier for organizations to retain ownership of their data while still getting expert help. Providers have gotten better at scoping engagements and communicating what’s included. And the tooling ecosystem around SIEMs—integrations, dashboards, automation—has matured considerably.
But here’s what hasn’t changed: co-managed SIEM still requires significant internal investment. Someone on your team needs to own the relationship, manage integrations, review rule changes, and stay current on the platform. If your team has the bandwidth and the SIEM expertise to do that well, the model can work. If they don’t, you’re back to the “too many cooks” problem, just with newer software.
Role confusion hasn’t gone away either. Even the best-run co-managed engagements require constant coordination on who owns what—and when something falls through the cracks (and it will), the question of accountability gets complicated fast.
Detection coverage gaps remain a real concern too. Co-managed SIEMs are generally strongest at log-based detection. As organizations have expanded into cloud, identity, and SaaS environments, providers that aren’t MDR-native may struggle to deliver the same depth of coverage across those surfaces.
What does “good” look like in 2026? It looks like a provider that integrates detection across your entire environment—not just what’s in the SIEM—and takes clear ownership of outcomes, not just operations. That’s where we see the model heading and what we built Expel Managed SIEM around. The distinction we’d draw isn’t co-managed vs. fully managed. It’s whether your provider takes clear ownership of the security layer, not just operations. Detection engineering that works across your environment. Full visibility into every rule and every decision. You keep control of your infrastructure. We’re accountable for the outcomes.
If you’re evaluating whether co-managed SIEM has improved enough for your organization, the honest question to ask isn’t “has the technology gotten better?” (it has). It’s “does my team have the capacity to make this work, and is this provider MDR-native enough to cover more than just my SIEM?” If the answer to either is no, MDR is likely the better fit.
Frequently asked questions about co-managed SIEM
What are the biggest problems with co-managed SIEM?
The most common issues are role confusion, internal resource burden, and detection coverage gaps. Co-managed SIEM requires ongoing coordination between your team and your provider—and when responsibilities aren’t clearly defined, things fall through the cracks. It also assumes your team has bandwidth and SIEM expertise that many security teams simply don’t have.
Is co-managed SIEM better than MDR?
For most organizations without a dedicated SIEM team, MDR is the better fit. Co-managed SIEM gives you more control and visibility into your SIEM environment, but it requires significant internal involvement. MDR offloads more of the operational burden and typically provides broader detection coverage across cloud, identity, and SaaS—not just what’s in the SIEM.
What’s the difference between co-managed SIEM and fully managed SIEM?
With co-managed SIEM, your team and the provider share responsibilities—things like rule management, log onboarding, and alert triage. With fully managed SIEM, the provider handles nearly all of it. The tradeoff is control vs. burden: co-managed gives you more say, but it also means more work on your end.
How much internal team time does co-managed SIEM require?
More than most organizations expect. Even in well-structured engagements, your team will typically need to own log source integrations, review rule changes, coordinate on incidents, and manage the vendor relationship itself. Security teams that are already stretched thin often find that co-managed SIEM adds workload rather than relieving it.
When does co-managed SIEM make sense vs. MDR?
Co-managed SIEM tends to make the most sense when you have a dedicated SIEM team, strong in-house expertise, and a specific need to maintain direct control over your detection environment—for example, due to compliance requirements or highly custom detection logic. If you don’t have those things, an MDR provider that can work alongside your SIEM will generally deliver better outcomes with less friction.
Has co-managed SIEM improved since 2020?
Yes—BYOS models, better tooling, and more transparent pricing are real improvements. But the underlying challenges around role clarity, internal resource requirements, and detection coverage outside the SIEM haven’t been solved by the technology alone. Whether those improvements are enough depends on whether your team has the capacity and expertise to hold up your end of the arrangement. You may also notice the terminology shifting—”co-managed SIEM” is increasingly being replaced by “managed SIEM” as providers take on clearer ownership of the security layer.
Not sure where to get started? Check out our free SIEM whitepaper: The ROI of “right-sized” logging: Getting value from your SIEM.