Kubernetes
Cloud security | 3 min read
Cloud Decoded (part 2): What attackers don’t want you to knowThis is part two of Expel's blog series on decoding the cloud. It dives in to what attackers don't want you to know.
Cloud security | 4 min read
Cloud Decoded (part 1): The cloud security mythbuster—what MDR really means for cloudThis is part one of Expel's blog series on decoding the cloud. The first one covers what MDR really means for cloud.
Cloud security | 8 min read
Comparison of cloud resources (part II): Demystifying cloud security toolsThis is part two of our four-part blog series on comparing cloud resources. Part two defines the types of tools used for cloud security.
Cloud security | 5 min read
Comparison of cloud resources (part I): Securing every layer of your cloud—from the control plane to appsThis is part one of our four-part blog series on comparing cloud resources. Part one covers the layers of the cloud infrastructure.
Cloud security | 8 min read
Cloud security: alert best practices (part II)This is part two of a two-part blog on cloud security alerts, including what makes them unique and best practices for management.
Cloud security | 8 min read
Cloud security: alerts vs. on-prem alerts (part I)This is part one of a two-part blog on cloud security alerts, including what makes them unique and best practices for management.
Cloud security | 6 min read
Part II: Fundamentals of Kubernetes securityLearn about the fundamentals of Kubernetes, including the four Cs of Kubernetes security and how Expel can help protect it.
Cloud security | 8 min read
Part I: Fundamentals of Kubernetes securityLearn about the fundamentals of Kubernetes, including its architecture, challenges, and false positives in part one of this two-part blog series.
Current events | 1 min read
GKE/Gmail vulnerability: notes and tipsSecurity researchers have discovered a new Google Kubernetes Engine misconfiguration. Here’s what you need to know.
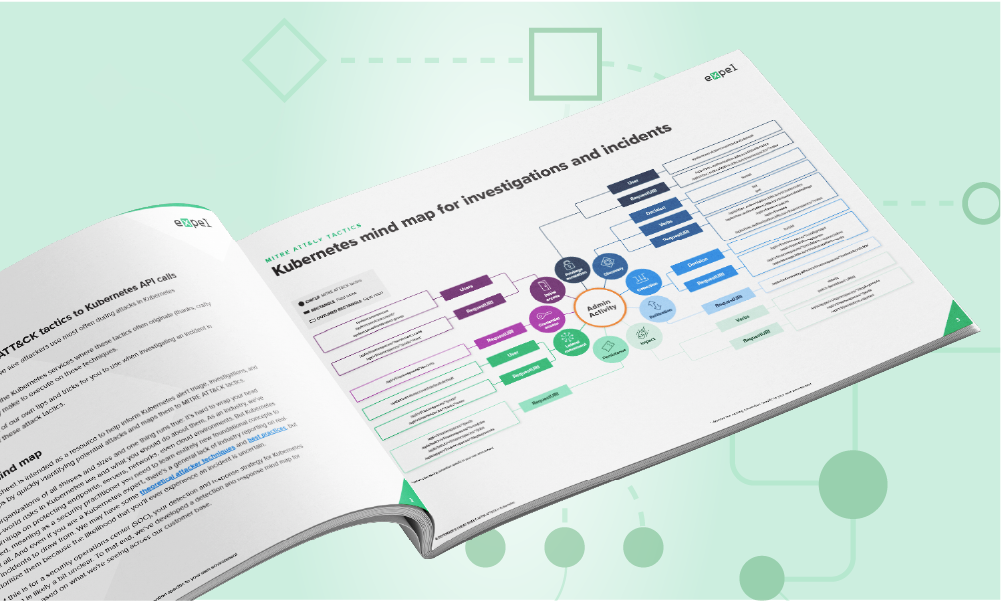
Cloud security | 3 min read
New mind maps & cheat sheets: Azure & KubernetesOur new Kubernetes mind map/cheat sheet show you which API calls are associated with different MITRE ATT&CK tactics in K8 environments.
Cloud security | 3 min read
Kubernetes security checklist: what to look forLearn what to look for and get key suggestions for your future security strategy and tools with this Kubernetes security checklist.
Cloud security | 3 min read
Why MDR is great news for securing Kubernetes environmentsThis post discusses how managed detection and response (MDR) f helps organizations in securing Kubernetes environments.
Cloud security | 1 min read
Understanding the 3 Classes of Kubernetes RiskThe first step toward securing Kubernetes environments is understanding the risks they pose and identifying the ways in which those risks can be mitigated.
Cloud security | 2 min read
Tell Dr. Kubernetes where it hurtsKubernetes is growing fast, but so are its challenges. Get part 1 of our series, where we outline the most common hurdles you'll face.
Data & research | 5 min read
45 minutes to one minute: how we shrunk image deployment timeWe recently figured out how to reduce Kubernetes image deployment time from 45 minutes (way too long) to one minute (really fast). Here’s how we did it.
Cloud security | 3 min read
Three Kubernetes events worth investigatingMonitoring your Kubernetes environment? Learn what to look for and how to use audit logs to secure your production workloads.
Cloud security | 3 min read
Kubernetes: the whale in the roomMore than half of our cloud customers use Kubernetes (k8s) to ship software faster and cut costs with elastic infrastructure.
Cloud security | 6 min read
5 best practices to get to production readiness with Hashicorp Vault in KubernetesFlying blind running Hashicorp Vault in Kubernetes? Get the best practices and tips to accelerate production without compromising on security.
Data & research | 8 min read
Containerizing key pipeline with zero downtimeMigrating to Kubernetes with zero downtime is a tall order. See how Expel’s engineers pulled it off without interrupting analyst workflow.