Defenders need so much information to make good security decisions in the security operations center (SOC). Situations constantly evolve—employees join and leave the org, new technology gets onboarded, unexpected risks surface, and so much more—it’s hard for the SOC to keep up with ever-changing conditions throughout the organization.
The good news is that all of these changes create contextual information that Expel and our customers use to make smart decisions. The more we know about your environment and your users, the easier it is for our software—and by extension our SOC analysts—to determine which events require remediation. With this in mind, we’ve introduced a new capability which allows you to add business context to Expel Workbench™ that helps our SOC team reduce the time-to-decision on alerts and relieve the burden on your team.
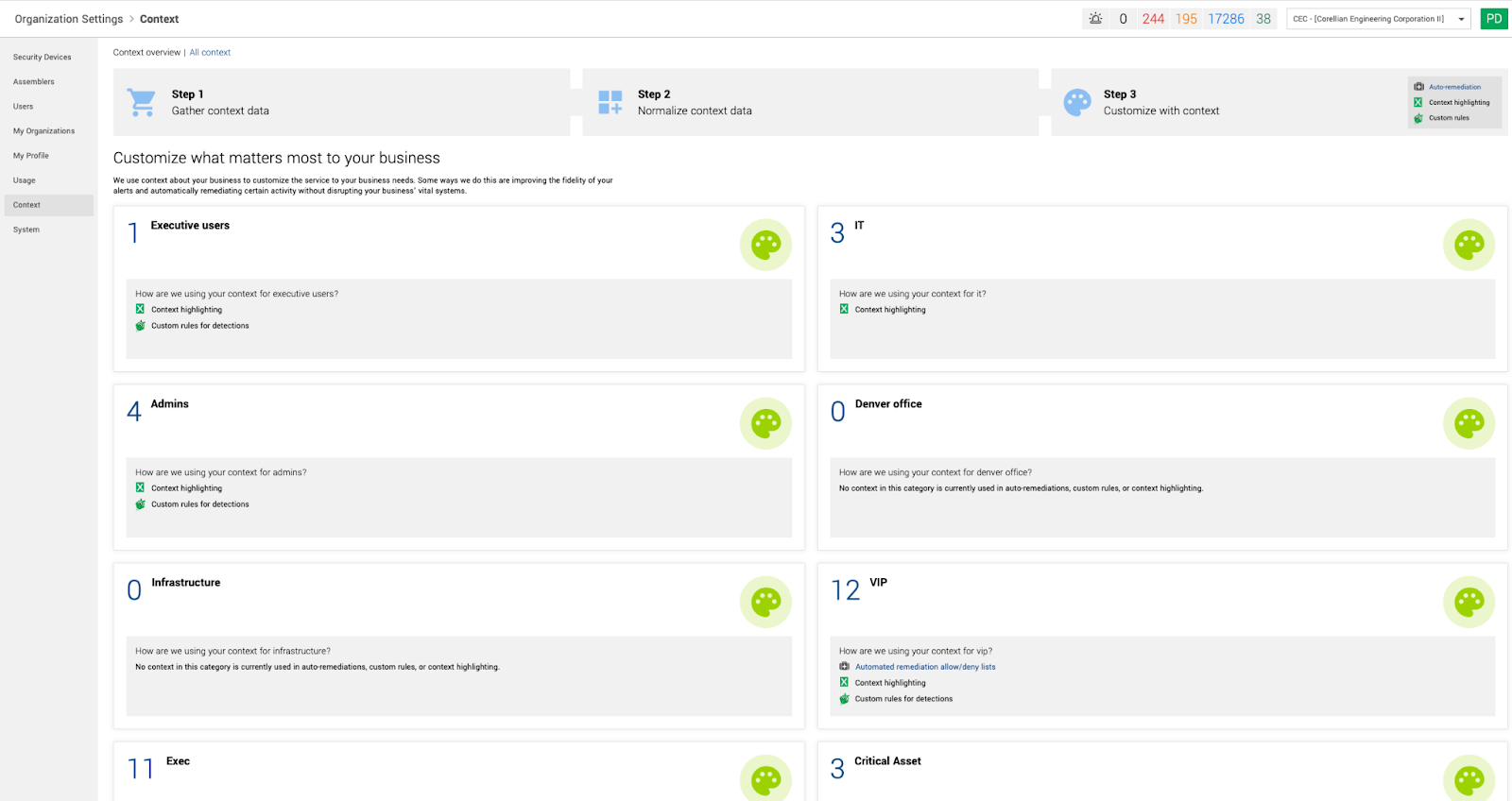
Adding context to Workbench
Here’s how it works: On the “Context” page in Workbench, users can add new context and see all existing context that has been previously added by your organization or our SOC team. Think of context as information about a user or situation that’s helpful to know when making a decision about a security alert. It’s like a virtual sticky note with directions like: Every time you see user X, be aware that they often travel outside the country. This gives Expel important information about the user’s location that could help quickly resolve alerts generated about logins from different countries when traveling.
On this page, you can edit context, add descriptions and notes, change users and more. You can also see a history of who created the context, who updated it, and when, and you can create categories to quickly group and find types of context being added in Workbench.
You can also upload lists of context, like IP addresses or emails that belong to specific groups.
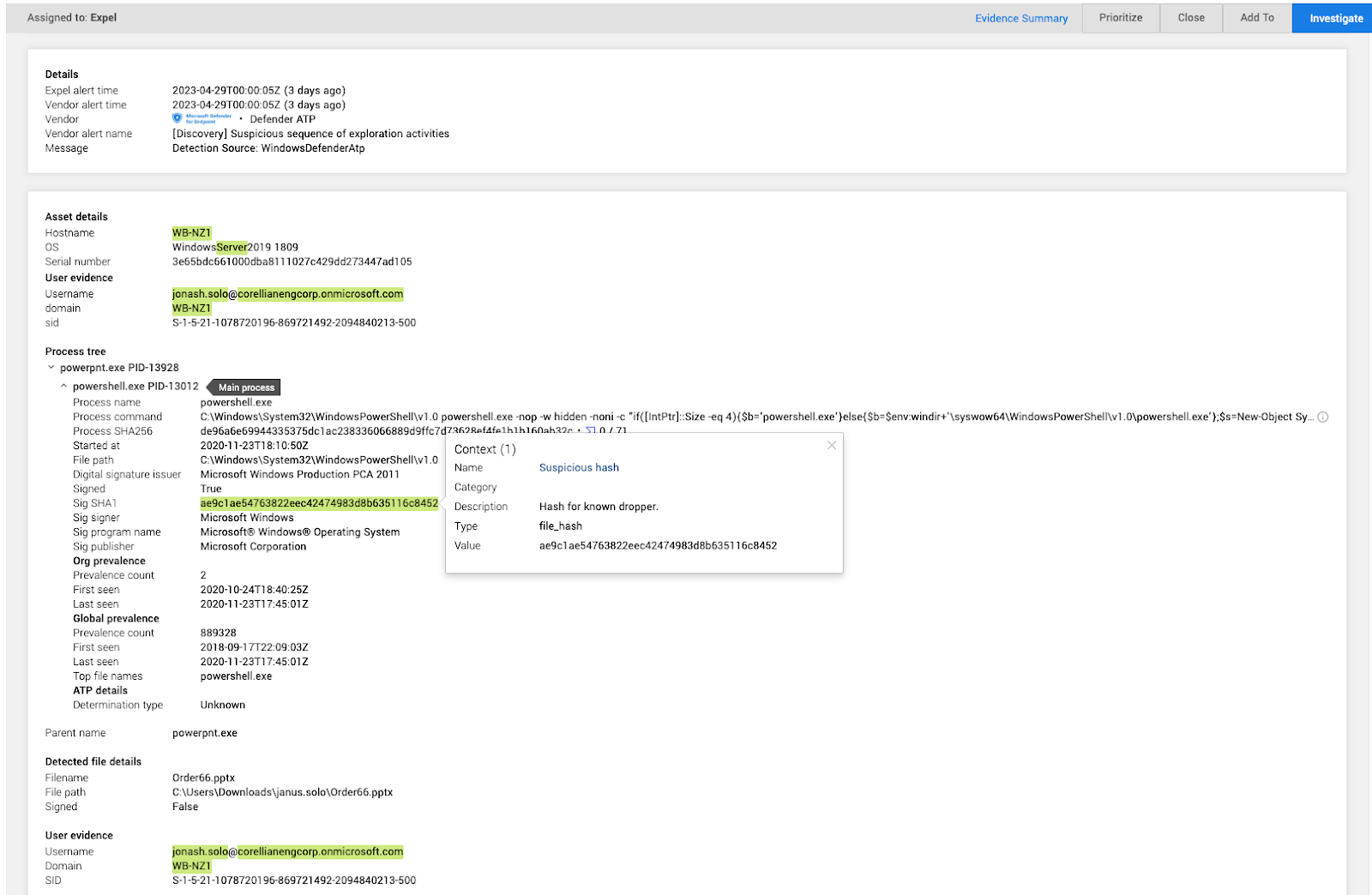
Highlight essential information
Once added, you can highlight this context in Workbench to call attention to important pieces of information. This serves as a digital sticky note for analysts to share information and learnings about an environment. For example, if we know that specific prefixes are used for admin hosts, we can add context calling out that host is an admin to provide situational awareness so analysts can make the right call on whether and how to act on an alert.
This is visible to Expel SOC analysts and customers, meaning you have insight into how analysts work alerts, investigations, and incidents.
More valuable ways to add context
Context allows you to easily make updates as employees leave the organization or change roles. For example, you can add context for the CEO’s email address along with specific intel into Workbench, knowing that CEOs are often targets of phishing attacks. If the CEO leaves the org, you can update or remove the email address and all the associated detections and workflows update automatically.
Another way to use context is to make note that specific indicators of compromise (IOC) have been linked to a threat actor within the environment. For example, the SOC can take note that the auto host containment remediation action needs to be taken immediately if a specific IOC is seen as alert. For example, if they see the domain faceb00k.com using zeroes instead of O’s.
Making Expel work for you
Context is just one more way to customize Expel to your specific environment. Be sure to check out the Context page under Organizational Settings to see what context you already have in place and consider additions that would be helpful.