In our recent report on cybersecurity in the United Kingdom (UK), IT decision-makers (ITDMs) point to a corrosive dynamic threatening the effectiveness of their security operations centres (SOCs) and the well-being of their security and IT teams. In sum, fatigue stemming in large part from a barrage of alerts and false positives is disrupting workers’ private lives, driving burnout and staff turnover at a time when there’s a critical talent shortage in the industry.
The effect is evident across the board, but companies with 250-1,000 employees (what Expel calls the commercial segment) are being hit especially hard.
Let’s review the findings and consider possible reasons why the 250/1k segment is suffering so badly.
Regardless of these findings, we believe there’s hope. At the end, we’ll discuss strategies to help businesses not only survive, but thrive in this environment.
Fatigue and burnout is worst for companies with 250-1,000 employees
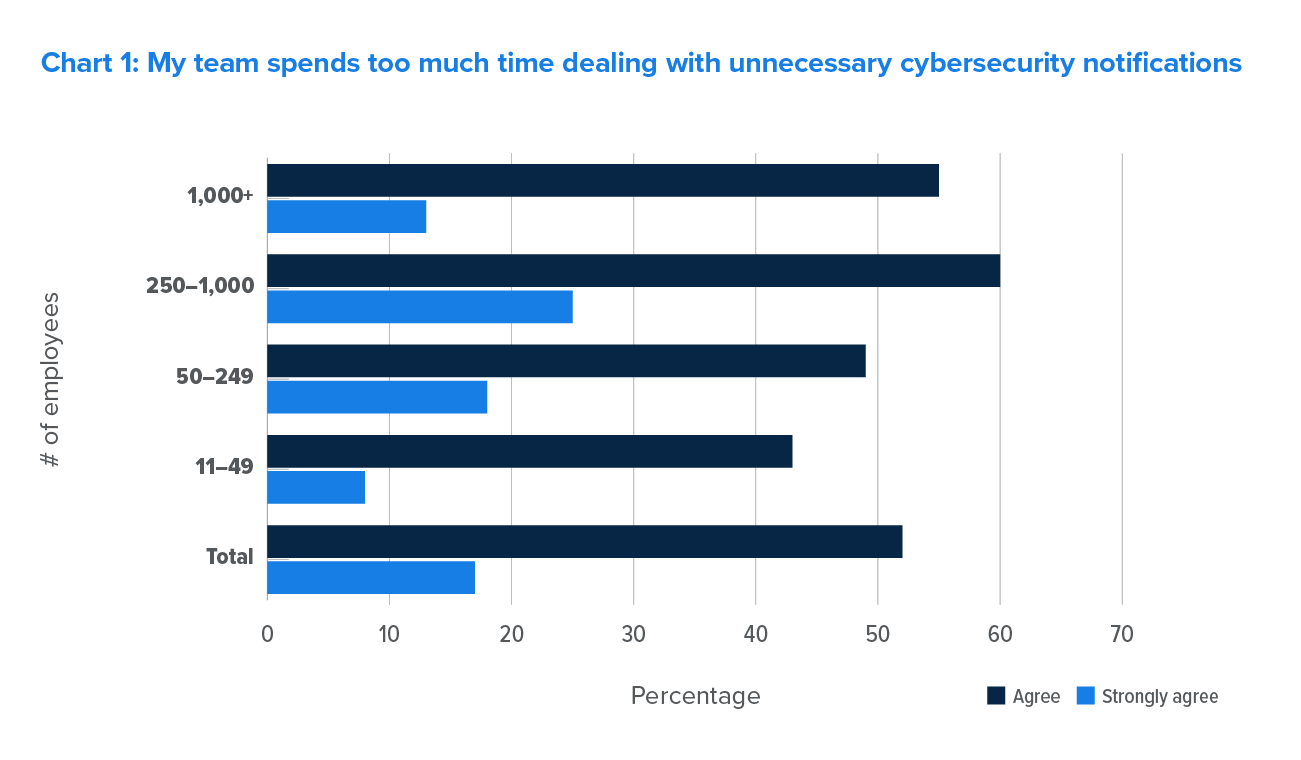
More than half of ITDMs say their SOCs spend too much time on alerts, with larger companies (250+) more likely to call it out as a particular concern. (Problem alerts include low-risk/low priority notifications and false positives.)
- Respondents in the 250/1k segment were most likely to say their teams spend too much time addressing alerts (60%).
- This segment also views the issue as more urgent, with a quarter saying they strongly agree.
ITDMs in the 250/1k segment are also significantly more likely to cite alert fatigue as a problem for their security teams.
The risk associated with fatigue is huge. As we noted in the UK report, an International Data Corporation (IDC) study found that a dizzying number of alerts are ignored—27% among companies with 500-1,499 employees (which includes a big chunk of the segment we’re examining here). This revelation—that more than a quarter of threat alerts hitting the SOC are being ignored—should keep leaders and board members awake all night, every night.
Alert fatigue and the 3CX hack
In the recent 3CX attack, many of the platform’s users had seen their endpoint protection software incorrectly flag known, good software as malicious in the past. Since 3CX’s software was expected in their environment, many analysts assumed the endpoint protection software was incorrect, rather than suspecting the software had been the victim of a supply chain attack. – Greg Notch, Chief Information Security Officer, Expel
Alert fatigue and burnout: the human toll
Alert overload, alongside all the other challenges associated with running a 24/7 SOC (during an era plagued by a 3.4 million-person talent shortage), represents an unsustainable infringement on security pros’ personal lives.
Ninety-three percent of ITDMs surveyed (and 95% in the 250/1k category) say their personal commitments are at least occasionally cancelled, delayed or interrupted because of work. But, as chart 3 indicates, the 250/1k group is affected significantly more often—51% of respondents say it happens all or most of the time, a stunning 15% more than the next highest segment.
Unsurprisingly, then, ITDMs in this key segment say their groups experience substantially higher degrees of burnout—14% higher than the ITDM total.
Staff turnover
The upshot here is that burned-out workers make mistakes (like the missed alerts that happened in the 3CX supply chain attack) or leave (perhaps both). The potential for attrition is especially distressing, given the talent deficit noted above.
Again, companies in the 250-1,000 employee range feel the crush worse than those in other segments.
This cohort feels a greater intensity on this measure than other respondents. Its 27% positive response is eight points higher than the all-segment average.
Why are companies with 250-1,000 employees having a harder time than other segments?
Greg Notch, Expel’s chief Information security officer (CISO), says these companies are “big enough to have big company problems, but lack the structure and funding to build a security program sufficient to defend their enterprise.”
The folks trying to keep those programs afloat are understaffed, so they’re naturally burning out. Also, because they’re stuck doing repetitive work just to keep the lights on, it’s preventing their career growth into more strategic roles. So they leave to find those opportunities elsewhere. And it’s easy for them to do that because of the talent shortage.
He also says it “doesn’t help that ransomware targeting is now going wider and down-market. As a result, these folks are in live-fire situations with bad business outcomes.”
The UK security report makes a couple of things clear. First, SOCs are under tremendous stress as they try to safeguard their organisations, and if CISOs and their teams feel overwhelmed the data illustrates why. Second, the pressure is substantially worse for IT/security teams in organisations with 250-1,000 employees.
And now, the good news
Given the dramatic worldwide talent shortage, it’s naïve to imagine that all organizations can find and afford the people needed to build and run their own SOCs.
Managed detection and response (MDR) addresses these problems. MDRs are fully-managed, 24/7 services staffed by experts who specialise in detecting and responding to a wide range of cyberattacks, including phishing, ransomware, and threat hunting. By marrying human expertise to advanced technologies, MDR analysts can detect, investigate, neutralise, and remediate advanced attacks.
This eliminates an organisation’s need for a large staff. The best MDRs relentlessly research the latest hacker tactics and develop advanced tools to process massive amounts of data and automatically sort signal from noise—meaning a company’s analysts see the important alerts, not all the alerts.
The list of benefits goes on, but the bottom line is that, for many organisations, MDR means broader, deeper, more sophisticated cyberdefense (and fewer headaches) for less money.
If any of this sounds relevant for your business, we encourage you to review the full report and drop us a line.