Expel’s quarterly threat intelligence report delivers real-world incident data directly from our SOC, updated every quarter so you always have a current view of the threat landscape. Each edition covers the top attack surfaces—identity, endpoint, malware, and cloud infrastructure—with breakdowns by incident type, attacker technique, and distribution method.
In Q1 2026, identity-related incidents accounted for 58.7% of all incidents handled by Expel’s SOC, endpoint threats reached 38.4% and continued a three-quarter climb, and ClickFix-based delivery became the most common malware entry point for the first time at 43.7%. Unlike a static annual report, this page is a living resource: new data is added each quarter, and older data stays, so you can track how attacker behavior evolves over time.
The latest data
What does Q1 2026 threat data tell us about attacker behavior?
Author: Ben Nahorney | Last updated April 2026
Incident overview
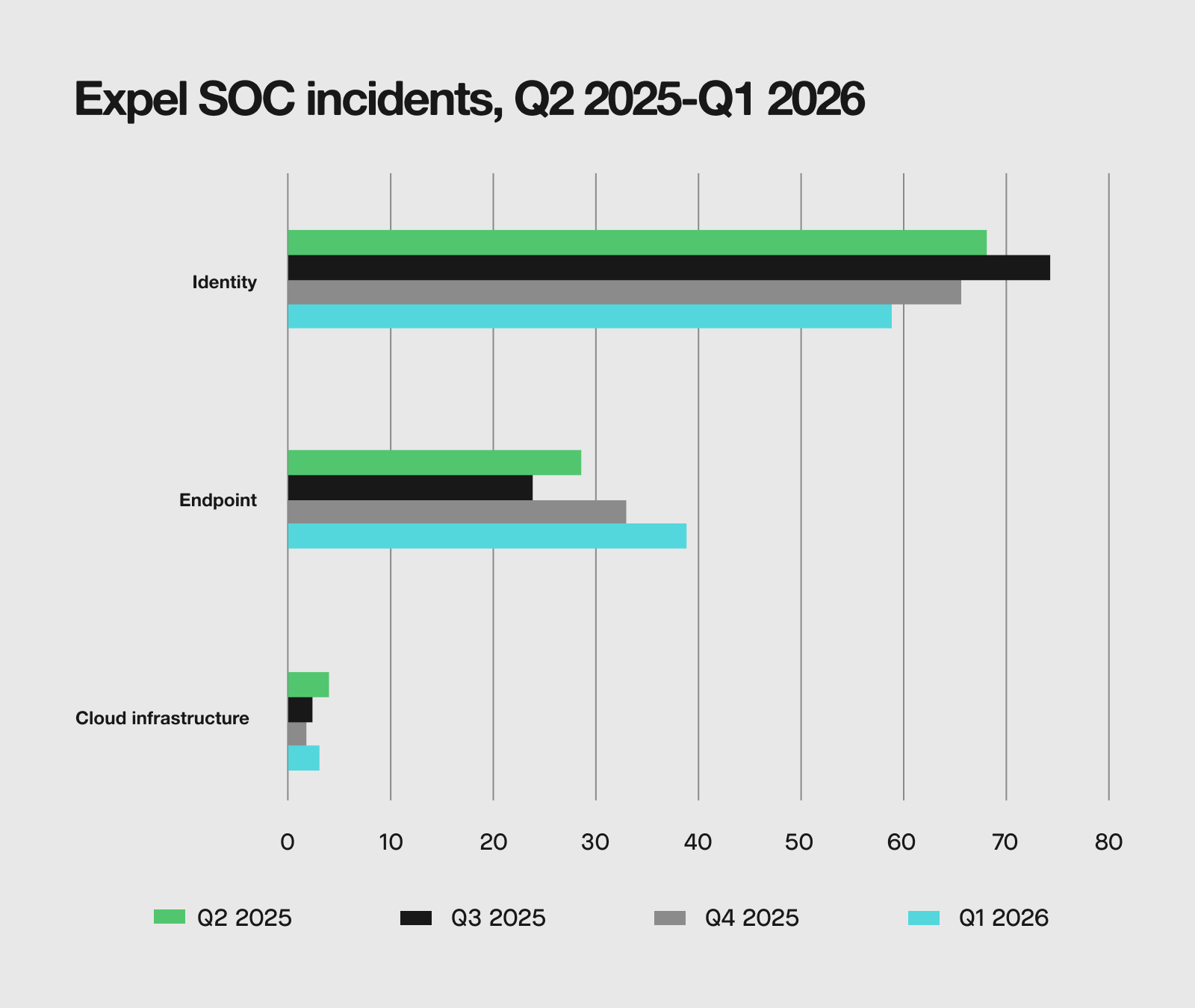
Identity-related incidents remain the dominant attack surface this quarter at 58.7%, but the quarter-over-quarter data tells a more nuanced story. Identity incidents appear to have declined from their Q3 peak in this timeframe.
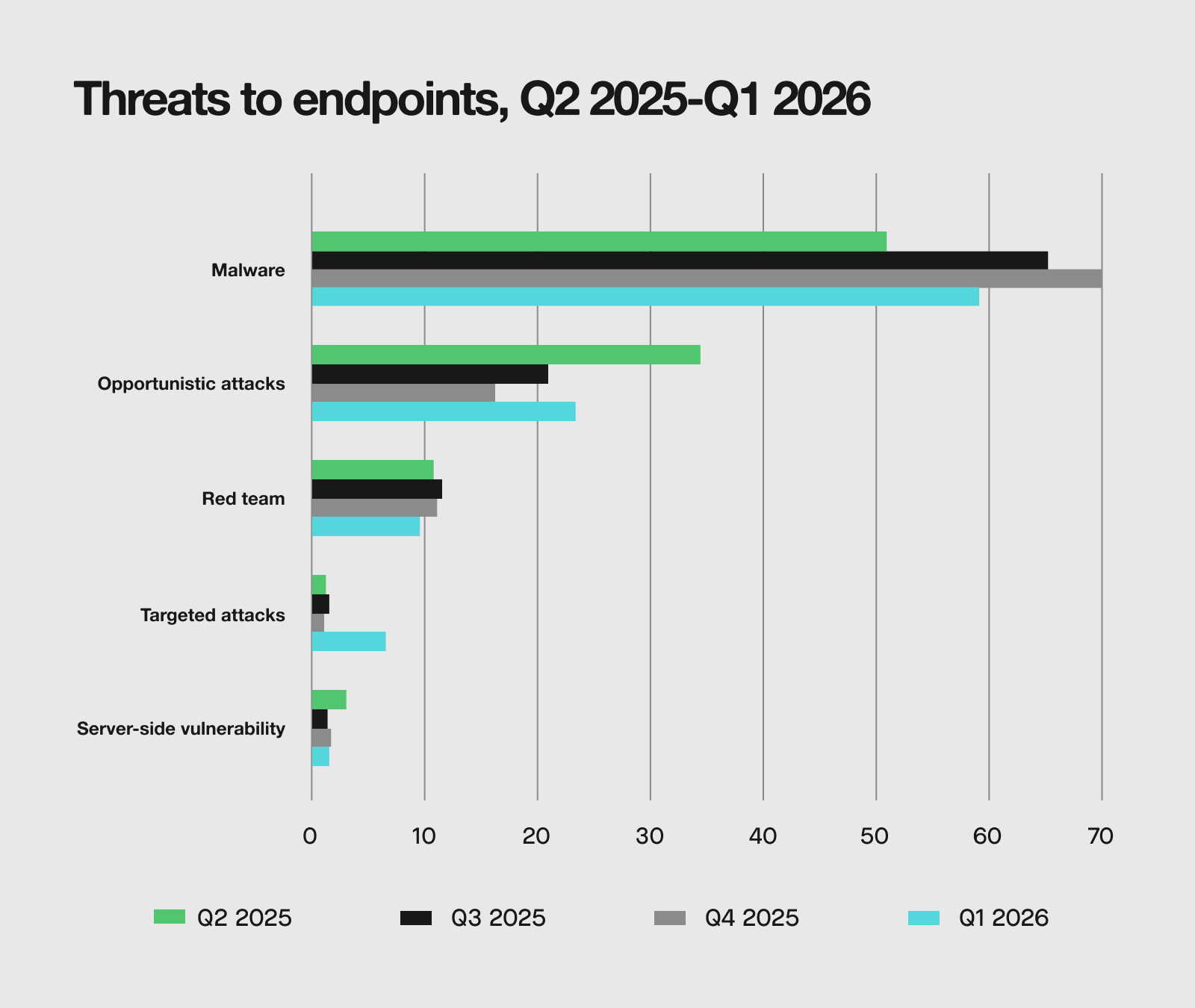
The more notable trend is the sustained rise of endpoint incidents, which have climbed steadily over the past three quarters to reach 38.4% (see below for more on endpoint activity). Cloud infrastructure, though still a small share of the total at 2.9%, has also been ticking upward.
IDENTITY
How are attackers exploiting valid credentials in Q1 2026?
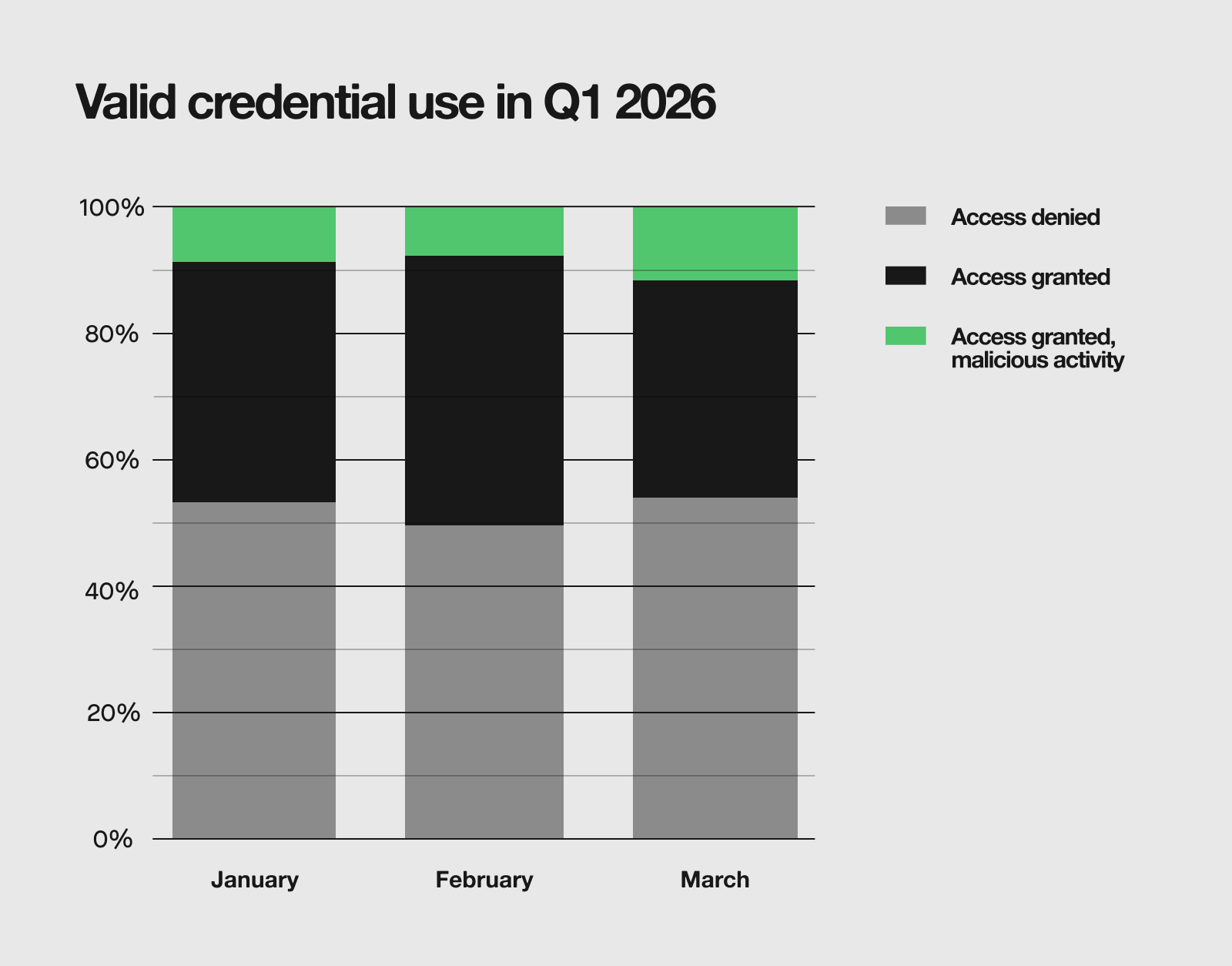
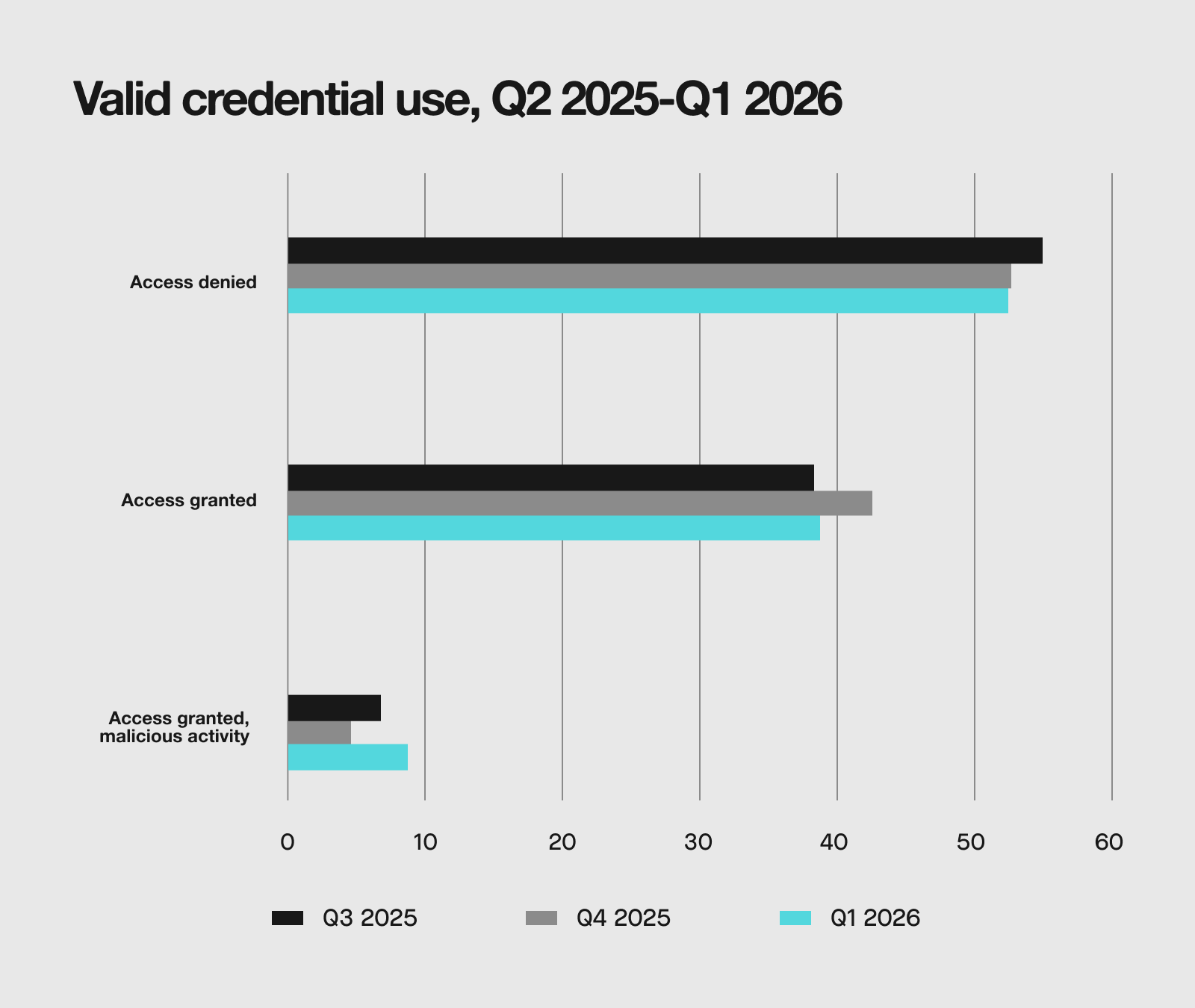
Valid credential use broadly held steady across Q1, but a closer look points at a concerning shift. February stood out as the month where attackers gained the most ground. Combined access granted incidents, which includes those involving confirmed malicious activity, reached 50.4%, meaning more than half of incidents resulted in some level of access.
This level receded in March, which might appear to be an improvement, but the composition of that decline tells a more concerning story. The share of incidents where access was granted and malicious activity followed grew to 11%. In other words, while fewer incidents overall resulted in access in March, a greater proportion of those that did led to harmful outcomes.
Zooming out to the quarterly trend, incidents where access was granted and malicious activity ensued also appear elevated compared to previous quarters, suggesting this isn’t just noise within Q1 2026. The rate at which valid credentials are being successfully weaponized may be on a gradual upward trajectory worth tracking in Q2.
ENDPOINT
How are attackers targeting endpoints in Q1 2026?
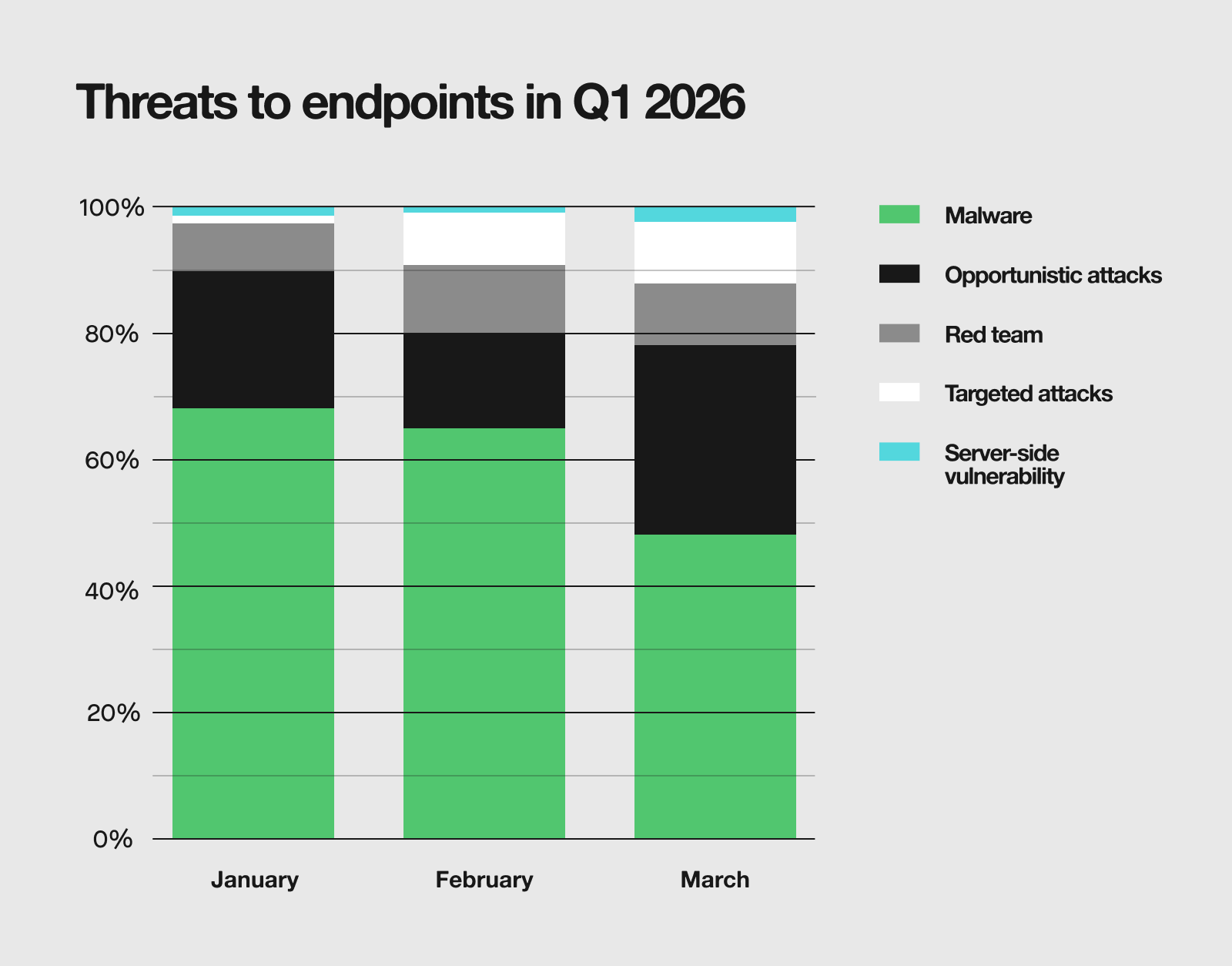
For endpoints, malware remained the dominant threat in Q1 2026. At first glance, malware’s shrinking share as the quarter progressed might suggest a drop in activity. However, the opposite is true—overall endpoint incidents surged in March, with opportunistic attacks more than doubling from February. The volume of malware incidents grew as well. This is a meaningful distinction, because it means organizations weren’t facing less malware, they were simply facing even more of everything else on top of it.
The quarterly chart also highlights a notable trend: targeted attacks increased sharply in Q1 2026. That rise has a clear driver—74% of targeted attacks involved Microsoft Teams-based phishing, pointing to a deliberate and increasingly organized effort to exploit collaboration platforms as an entry point. Combined with the increase in opportunistic attacks, attackers appear to be expanding both the volume and the range of methods they’re willing to deploy.
MALWARE
What malware should security teams watch in Q1 2026?
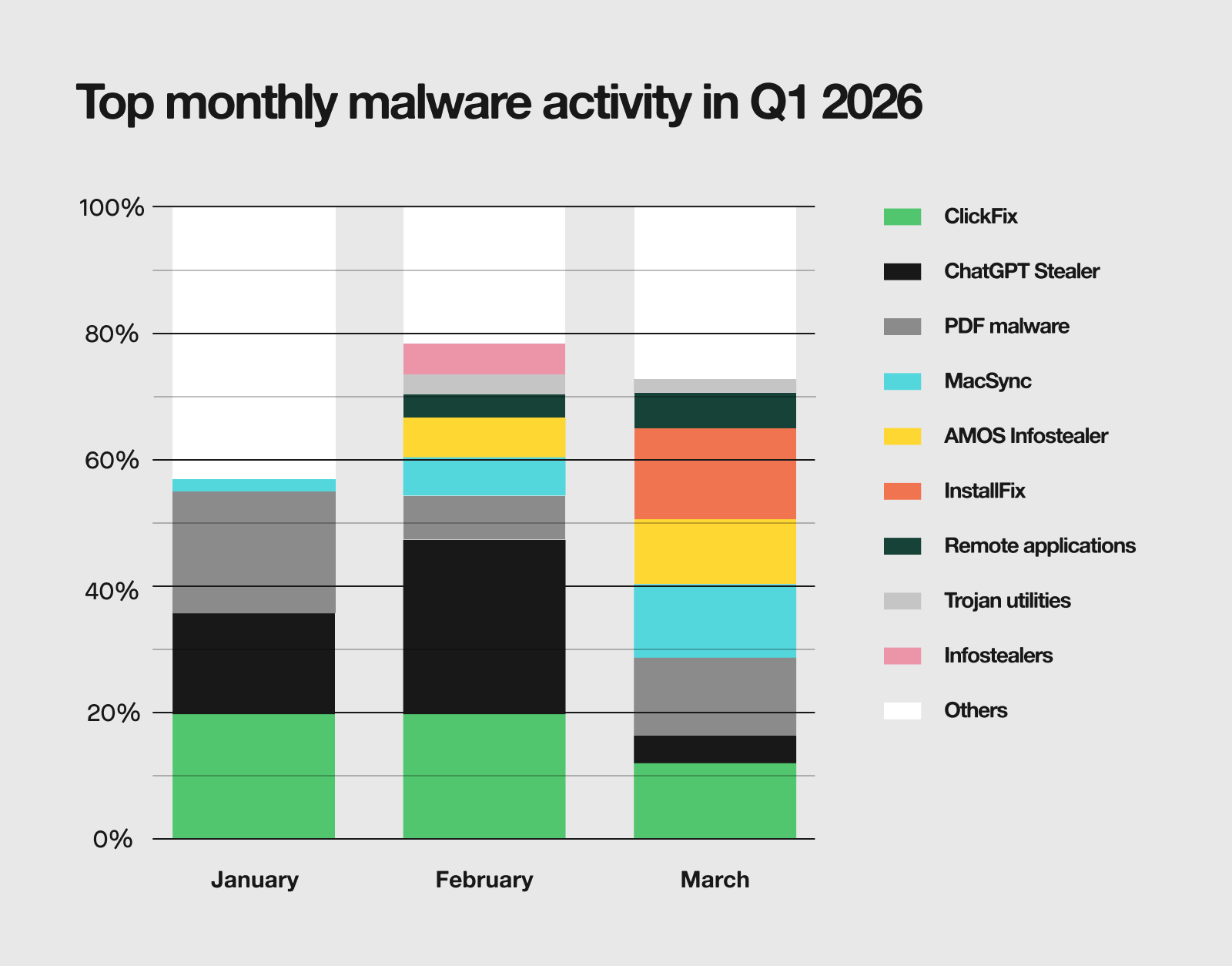
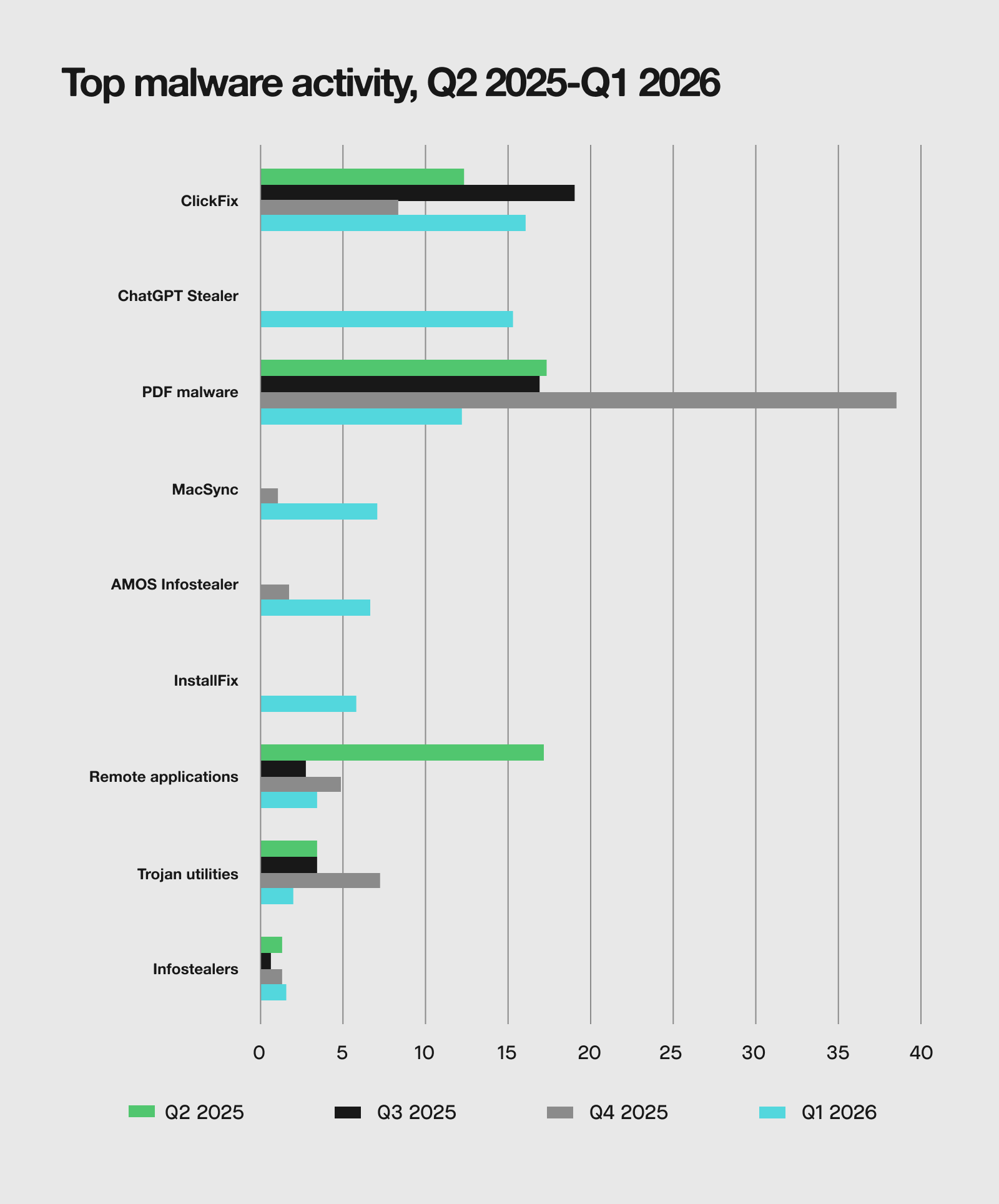
The malware landscape in Q1 was initially dominated by ClickFix and ChatGPT Stealer, which together accounted for a third of all malware incidents in January, and then almost half in February. March, however, brought a notable reshuffling. That top spot was claimed instead by InstallFix, a newly observed variant of the ClickFix technique, which accounted for 14.3% of March incidents.
Looking at the longer quarterly trends, PDF malware stands out. After a major increase in Q4 2025, it receded in Q1, but still remains a top threat. MacSync and AMOS Infostealer are also worth watching, as they have appeared more prominently in Q1 than in prior quarters, pointing to an increase of interest in macOS environments.
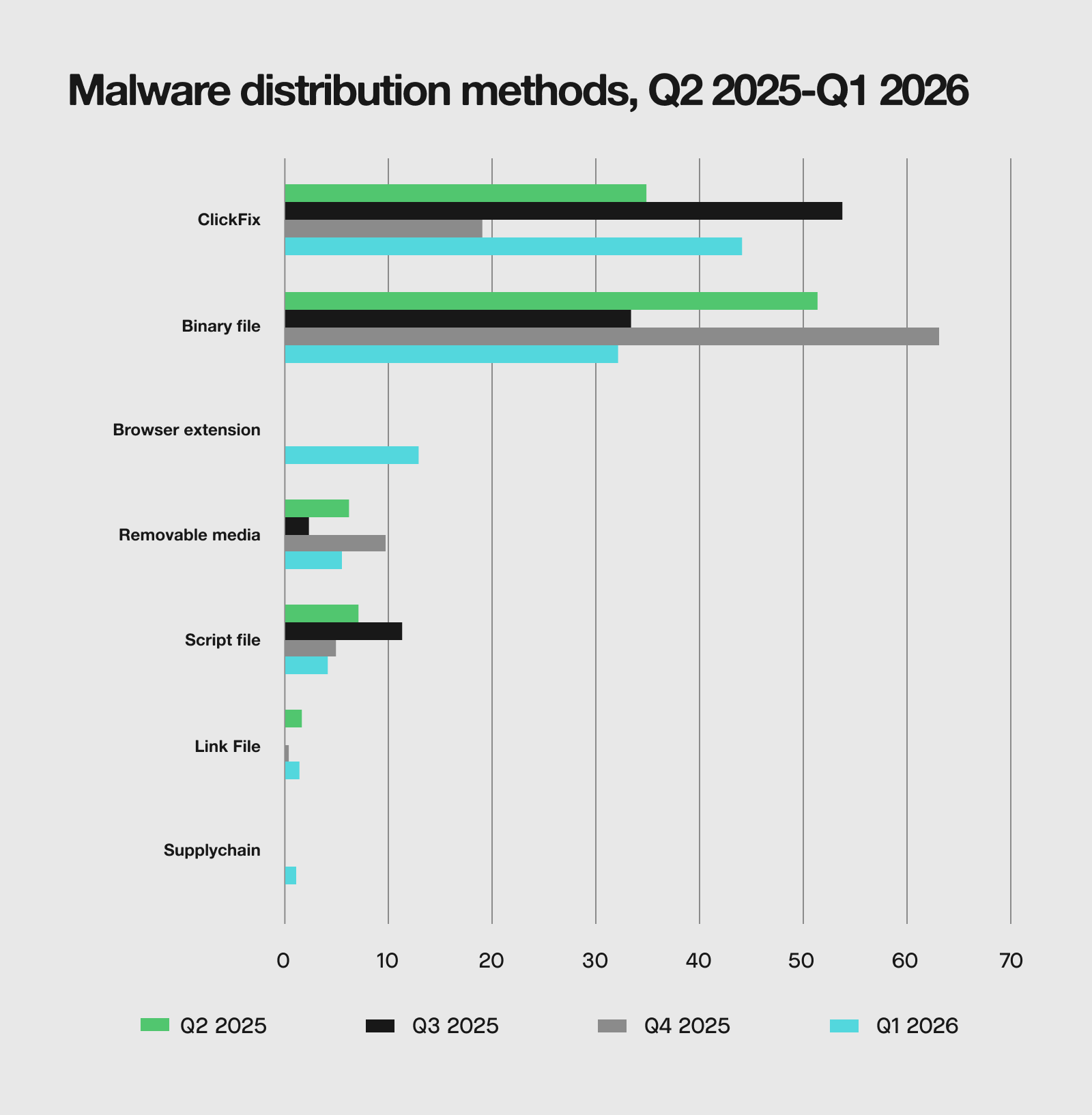
At 43.7%, ClickFix was the most commonly encountered malware delivery mechanism of Q1, overtaking binary files for the first time. This is a significant change reflecting how threat actors are focusing on social engineering-based delivery over more traditional execution methods. Its dominance is due to how many distinct malware families utilize ClickFix tactics: InstallFix, KongTuke, MacSync, and NetSupport RAT, to name a few. Browser extensions also emerged as a trend worth noting, accounting for 12.7% of malware entry points in Q1 2026. This growth is largely attributed to ChatGPT Stealer incidents.
CLOUD INFRASTRUCTURE
How are attackers compromising cloud infrastructure in Q1 2026?
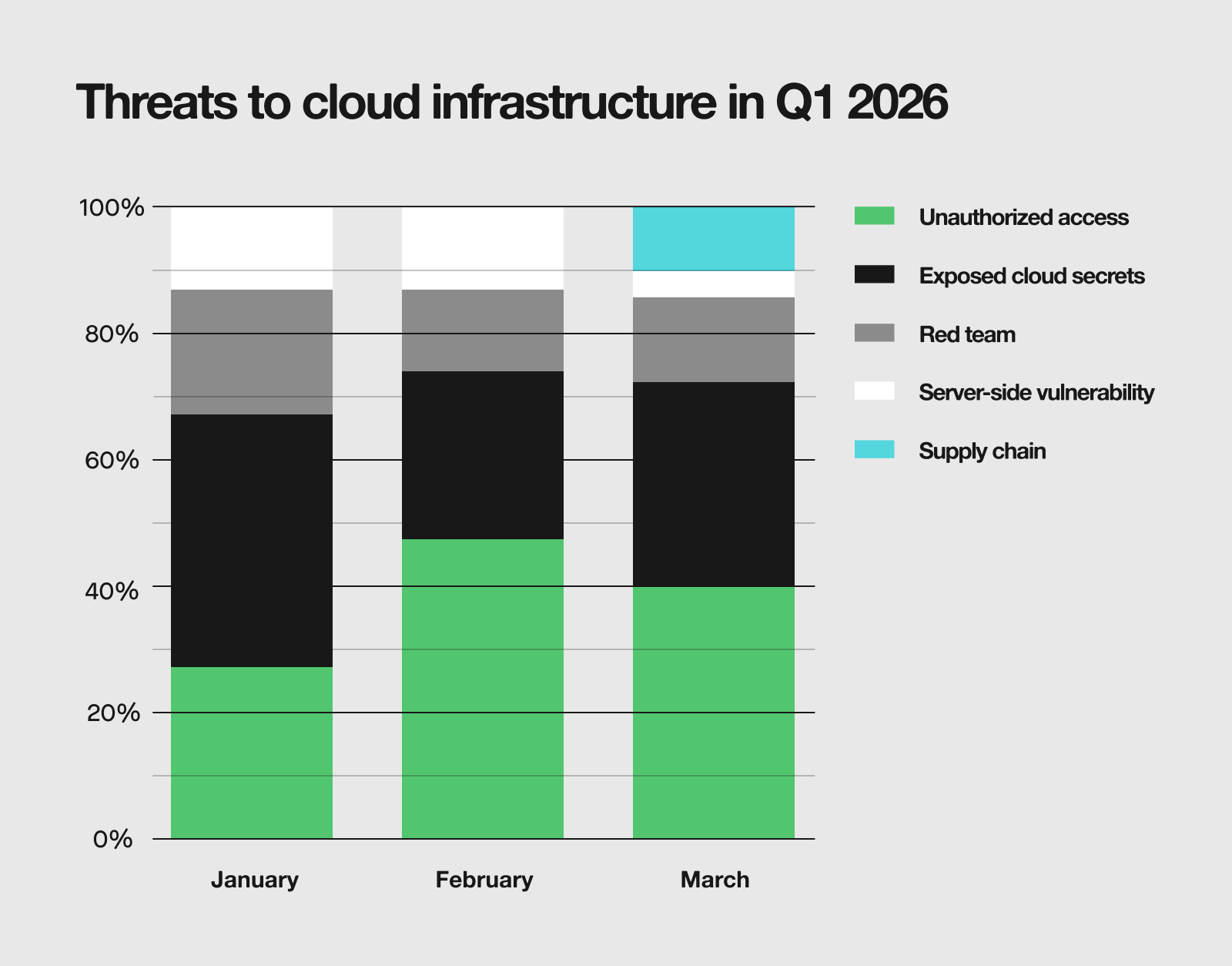
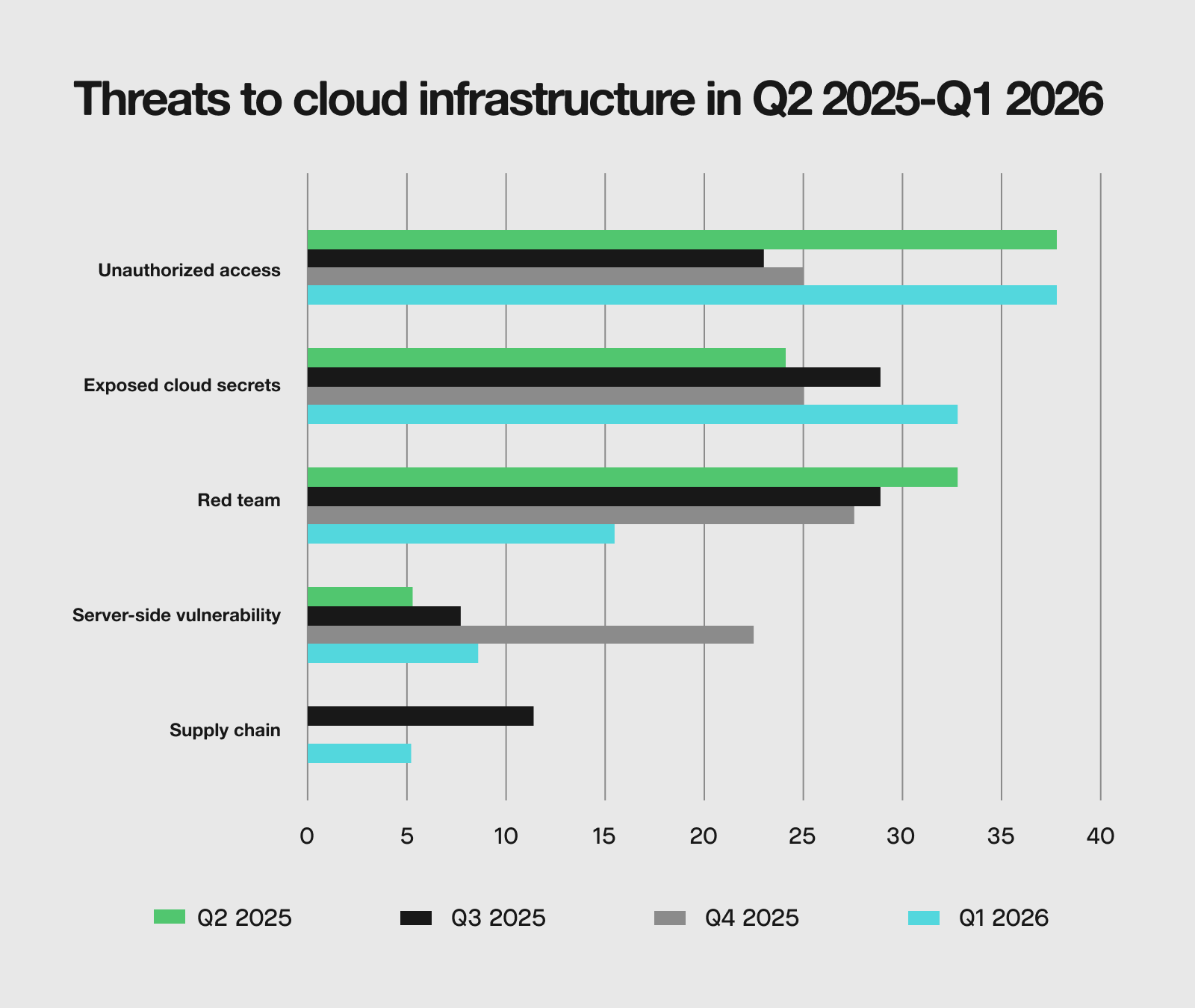
Unauthorized access and exposed cloud secrets were the two main methods used by attackers to gain entry to cloud infrastructure during the quarter. In March, supply chain attacks accounted for 10.7% of incidents, largely attributable to the Axios npm compromise that emerged toward the end of the month. A single third-party library incident accounting for a meaningful slice of an entire month’s cloud threats is a pointed example of how quickly supply chain events can translate into widespread exposure.
Zooming out to the full quarterly view, unauthorized access leads in Q1 at 37.9%, and sits notably high relative to Q3 and Q4 2025. Similarly, exposed cloud secrets remain elevated compared to previous quarters. The category to watch heading into Q2 is supply chain. The Axios npm compromise resulted in a measurable increase after only appearing at the end of March, suggesting it deserves to be on the radar going into Q2.
Historical Data