We’re often asked about the biggest threats we see across the incidents we investigate for our customers. Where should security teams focus their efforts and budgets? To answer these questions, we’re sharing monthly reports on the top attack vectors, trends, and resilience recommendations identified by our Security Operations Center (SOC). Our goal is to translate the security events we’re detecting into a security strategy for your org.
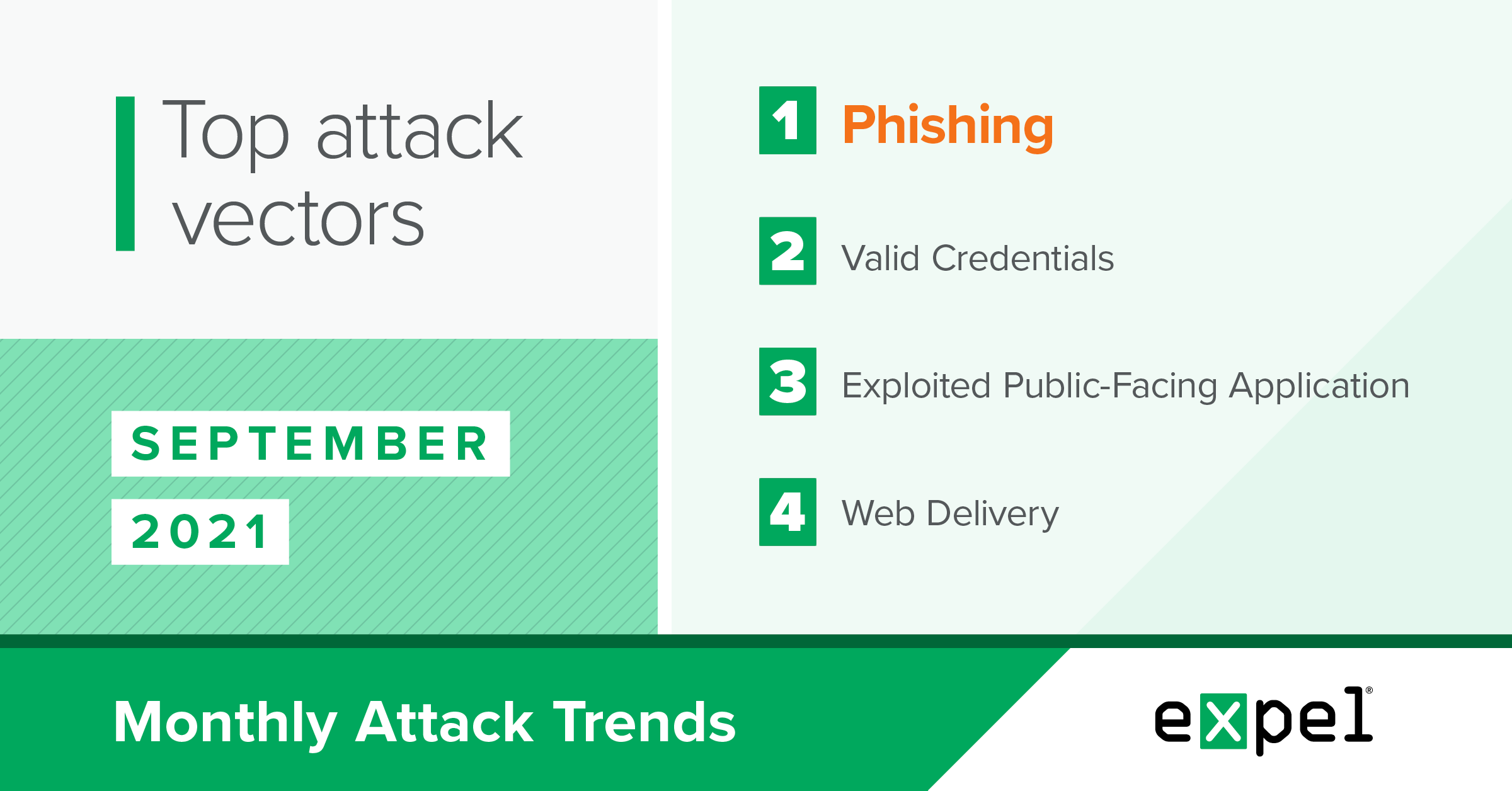
For this report, our SOC analyzed the incidents we investigated in September 2021 to determine the top attack vectors used by bad actors. Here’s what’s ahead:
- How bad actors are exploiting public-facing vulnerabilities for crypto mining
- The PowerShell/DotNet combo bad actors are using for malware
- The growing Business Email Compromise (BEC) target that can give attackers access to a variety of apps
- What to do about all of the above
Public-facing vulnerabilities and cryptojacking
TL;DR: Threat actors are continuing to find and exploit public-facing vulnerabilities, with a focus on deploying cryptocurrency mining software.
The exploitation of public-facing vulnerabilities continues to be a top infector vector for threat actors as this category made up 42 percent of the critical incidents we responded to in September.
Of these incidents, 80 percent deployed the XMRig cryptocurrency mining software after the initial compromise. This program uses up a vast amount of the compromised system’s resources as it tries to earn cryptocurrency for the threat actors before the software’s detected. This use of compromised computing assets for blockchain mining to earn rewards is known as cryptojacking.
Securing potential entry points should be your first focus for preventing cryptojacking and other impactful attacker payloads. In September, we observed the following CVEs for these exploited web applications:
| CVE-2020-36239 | Jira Data Center |
| CVE-2021-26084 | Confluence Server |
Next, system alerts for resource usage can serve a dual purpose for both your operations and security teams. These alerts are normally used by operations teams to automate monitoring system health, but the intense resource demands of cryptocurrency mining software makes it highly likely that cryptojacking will also activate alerts set up to detect when systems are running at their maximum capacity. This monitoring process can be streamlined in the cloud, with built-in solutions like AWS CloudWatch, Azure Monitor and GCP Cloud Monitoring.
Resilience recommendations:
- Consider hiring a penetration tester to gain a better understanding of your external attack surface.
- Have computing resource alarms forwarded to your SIEM.
- Deploy an endpoint detection and response (EDR) tool on web servers.
- Scan and identify public-facing assets using Shodan.
- Ensure public web applications are patched to their latest version.
- Deploy a web application firewall (WAF).
Attacker payloads often use PowerShell and the DotNet framework
TL;DR: Malicious payloads deployed by threat actors take advantage of the PowerShell scripting language and DotNet framework built into the Windows operating system (OS) to obfuscate the true nature of the malware and avoid detection.
In September, 83 percent of the malicious payloads we identified during incidents used the PowerShell scripting language and/or the DotNet framework. Both of these components are installed by default in modern versions of the Windows OS and provide different pathways for attackers to obfuscate the functionality of their malware.
The SolarMarker Malware variant, which made up 33 percent of our identified malicious payloads, is a prime example of malware that uses these two Windows components. We observed a particular SolarMarker variant that was delivered as a Windows installer file.
While its activity on the host was blocked before completion, analysis revealed that the malware first executed a series of PowerShell commands to generate an encoded file on the host. This file was then decoded in-memory into a valid DotNet module containing command and control logic that was then loaded and passed control.
With the continued popularity of PowerShell and DotNet for attackers, consider the resilience recommendations below to prevent malware from being deployed on your systems through these vectors.
Resilience recommendations:
- Consider implementing PowerShell Constrained Language Mode.
- Enable PowerShell Script Block Logging.
- Confirm your endpoint detection and response (EDR) coverage across all of your endpoints.
Phishing
Business Email Compromise (BEC) is still the top threat, but threat actors are looking beyond your inbox.
TL;DR: BEC remained the top threat in September, but attackers are looking to compromise single sign-on (SSO) identity providers, as well.
In September, 61 percent of the critical incidents we responded to were BEC — on par with previous months. Azure AD Identity Protection remained a strong signal for this type of compromise as the source for detecting 56 percent of the BEC incidents we identified.
While we’ve covered the basics of BEC in our previous threat reports, we observed two notable trends in September that are worth calling out.
The first was the use of a Python-based user agent when threat actors attempted to interact with a mailbox after a successful phishing attempt, seen in 5 percent of the BEC incidents. This stood out to us because threat actors typically spoof their user agents in an attempt to blend in, rather than using the default user agent supplied by their tool of choice, like the Python requests user agent seen in these incidents. This type of scripting language-based user agent presents a detection opportunity, especially if its prevalence continues to rise.
Resilience recommendations:
- You know it’s coming – multi-factor authentication (MFA) for everything and everywhere.
- Conditional access policies are a great way to help mitigate geo infeasibility.
- Disable legacy protocols like IMAP and POP3 (these don’t enforce MFA).
- Consider Azure AD Identity Protection to help identify suspicious mailbox logins.
Bad actors are also going after cloud identity provider access.
The second notable BEC trend we observed in September was attackers not only phishing for email access, but also trying to access a user’s cloud SSO provider.
One of the critical incidents we responded to this month had an initial lead of several suspicious logins from the same IP. Further investigation revealed that phishing emails sent to the impacted users contained a link to a credential harvester for the popular SSO identity manager Okta. This wasn’t our first time seeing threat actors attempt to gain access to Okta through phishing.
While the threat actors in this particular incident used the harvested Okta credentials to log into Microsoft Office 365 (O365), compromising a user’s SSO credentials opens up a world of possibilities for an attacker to move into any application provisioned to that user. We think attackers were motivated by this opportunity, as all of the incidents we investigated in September involving cloud identity providers targeted Okta. Of note, we’ve also observed threat actors gaining access to Amazon Web Services (AWS) by way of Okta SSO access in previous months.
Resilience recommendations:
- Implement phish resistant MFA (fido/webauthn).
- Enforce MFA prompts when users connect to sensitive apps through app-level MFA.
- Customize your Okta sign-in page appearances. If a user lands on a phony Okta sign-in page with no customization, it can help trigger their spidey-sense and let them know that something isn’t right.
Takeaways
Phishing and BEC remain the hottest threats we’re observing and the most likely way an attacker will gain a foothold into your environment.
Threat actors are continuing to target cloud SSO identity providers through phishing emails. While inboxes remain an enticing target, this type of access allows attackers to sign into a variety of applications including cloud providers like AWS, Azure and GCP.
Enforcing MFA and disabling legacy protocols should be your first steps to protect against BEC. But when it comes to SSO identity providers, consider customizing your login page to help users visually detect when they’ve opened a fake page like a credential harvester. Then apply additional MFA around any highly sensitive applications and access roles as a second line of defense.
In the realm of malware, 80 percent of the public-facing vulnerability exploits we observed in September were used to deploy the XMRig cryptocurrency mining software. This isn’t a coincidence given the recurring cryptocurrency activity we’ve seen this year.
Start by following proper endpoint guidance, including EDR and patching, and understand your external attack surface to help prevent these exploits. Next, applications used to alert operations teams of overtaxed resources can also help security teams by indicating resources deployed for cryptojacking.
Threat actors are also continuing to deploy malicious payloads that use the PowerShell scripting language and/or the DotNet framework. PowerShell Script Block Logging and constrained language mode can help detect and prevent threat actors using PowerShell.
We’ll be back with insights on October’s top attack vectors. In the meantime, have questions about this month’s data or what it means for your org? Drop us a note.