Protect Microsoft Environments
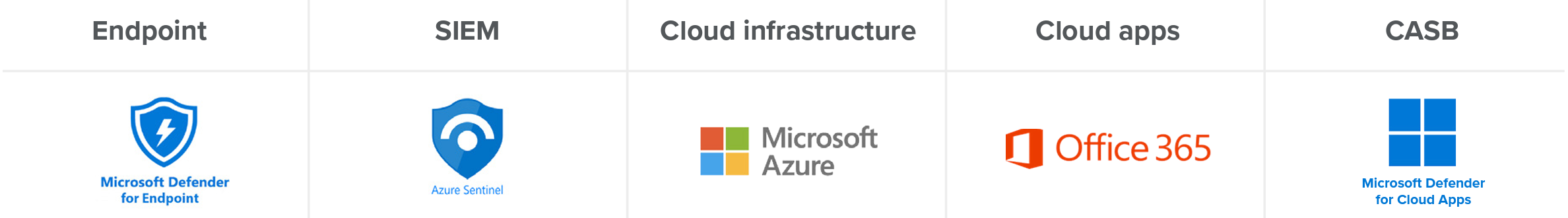
24x7 detection and response for Microsoft Defender for Endpoint, Azure (Sentinel & Active Directory) and O365

Securing your Microsoft environment is challenging
Attempting to secure multiple attack surfaces within Microsoft (devices, cloud infra, identity, SaaS apps)
Overwhelmed sifting through large amounts of logs and alerts to identify what matters
Trying to keep up with a constantly changing and growing environment
Wanting to detect, investigate and respond to incidents quickly
How does Expel MDR protect your Microsoft environment?
Expel is built with the cloud in mind to support you today and in the future. We understand the Microsoft environment. With so many tools out there, it can be tough to know where to start and what to look for. We apply our detection strategy for each of Microsoft’s top services, so the value from your investments is as clear as the sky is blue. (Did someone say Azure?) Here are just a few of the things we’ll do for you:
- Ingest logs and alerts from your Microsoft environment including O365 audit logs, Azure platform logs, Azure Log Analytics
- Correlate signals and use Microsoft-specific detections to identify anomalous activity, and/or incidents
- Alert and provide you with next steps (via Microsoft Teams if you use it) or auto-remediate for you
- Proactively analyze data to identity weak spots in your environment through threat hunting and suggest mitigation steps
What do we cover for Microsoft?