TL;DR
- Expel’s new AI-powered detection agent automatically identifies coverage gaps in third-party vendor telemetry and proposes new rules so we can find evil sooner.
- Beyond creating new logic, the agent enhances existing detections with new logic to provide clearer, more actionable alerts.
- To guarantee high-fidelity, Expel-validated detections, every generated rule must pass rigorous syntax tests executed by the agent tools and a mandatory review from our expert SOC before going live.
Expel’s philosophy centers on a defense-in-depth model using the technology you already own. We ingest telemetry from across your environment, spanning endpoints, networks, identity, cloud, SIEMs, and more.
While point solutions are fantastic at stopping isolated events, modern threat actors intentionally navigate the spaces between these tools. To see the broader narrative, we actively write and layer our own proprietary, high-fidelity detection rules on top of existing vendor alerts.
These Expel detections have a tremendous impact for our customers. Our 2026 Annual Threat Report showed 78.8% of alerts for critical/high incidents in 2025 were detections written by Expel. Read the full report to learn more.
Maintaining this layered defense at scale across our 160+ connected tools is the challenge. As security vendors constantly update their detections and technology, moving from third-party innovation to our first-party detection strategies requires significant effort from our detection engineering team. During that transition, our SOC analysts do the heavy lifting, providing air cover by finding ways to use this new telemetry as context until new rules are deployed.
Today, we are thrilled to announce a massive leap forward in accelerating how we create new detections: Expel’s new detection agent. Our first agentic AI feature automatically analyzes novel vendor alerts to deliver new detections, faster. The AI identifies coverage gaps and proposes rules to find evil sooner, drafting syntactically correct detection code to layer on top of them.
Agentic AI for detection generation
Adapting to new vendor alerts has historically been a highly manual, labor-intensive process. As alert volumes and complexities grew, relying on humans to manually parse every single newly observed vendor signal became a bottleneck.
Previously, our detection engineering and SOC teams relied on a manual weekly process to review these novel alerts. Due to bandwidth constraints, they primarily focused on the alerts that escalated into full-blown incidents.
We also observed the other alerts—the true positives that didn’t escalate, and the noisy alerts requiring tuning. However, the sheer volume outpaced our capacity to manually layer these new detections on top of every single signal.
Without an automated process, these signals remained underutilized. They were often treated as additional context, even though they served as valuable building blocks for better detection coverage. We needed a scalable way to turn all relevant new signals into high-quality additions to our detection strategies and improve the ability for our team to better support our customers.
What makes this different?
The cybersecurity market is currently flooded with “AI copilots” aimed at supporting detection engineering. Most of these tools rely on an open-ended chat interface, requiring a human engineer to analyze threat intel, type a prompt, and work alongside the AI as it generates code.
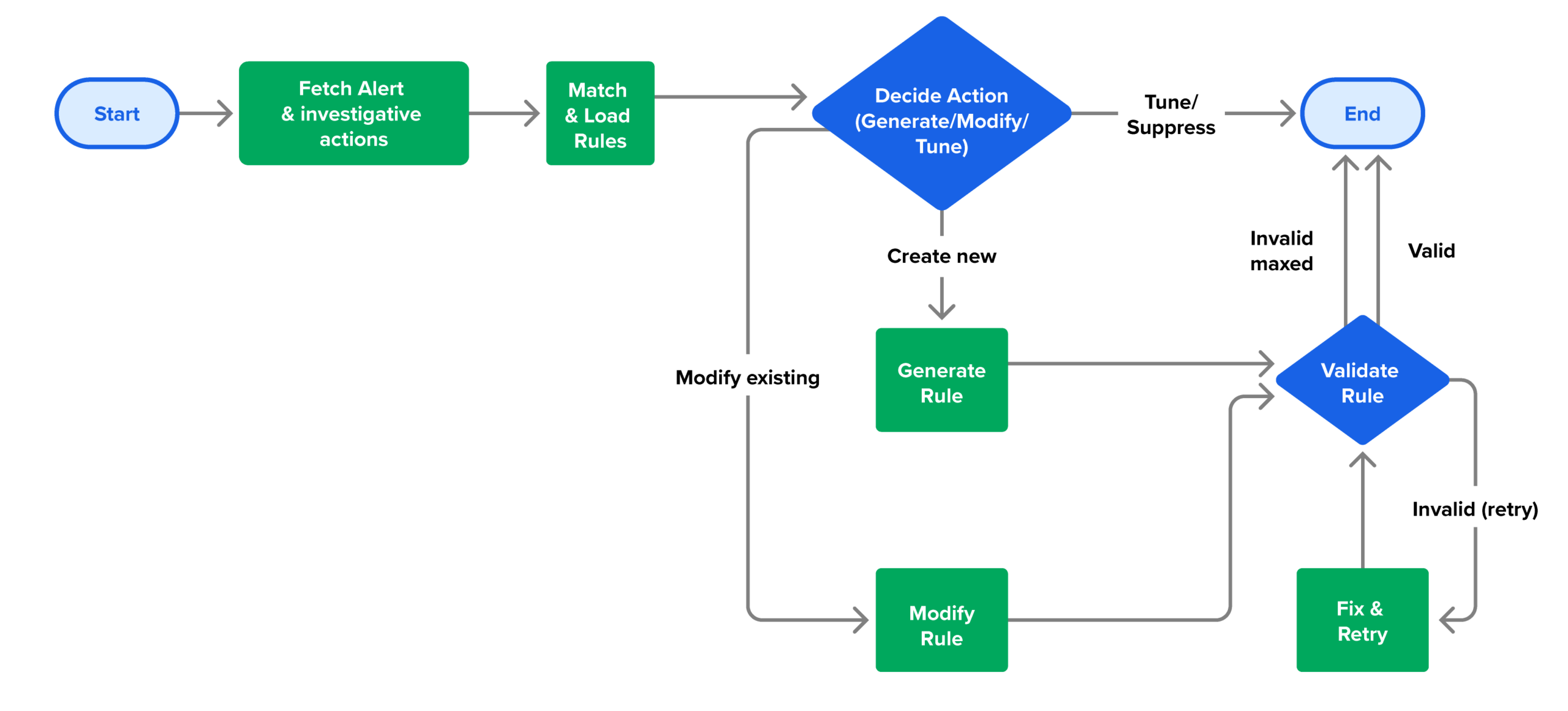
We took a different approach to the problem. Our agent turns detection engineers from writers into editors. We built this new detection agent as an event-driven, autonomous pipeline for detection engineering. It operates with a strict, deterministic logic tree. The moment Expel observes a novel vendor alert, the agent automatically kicks off a precise background workflow that takes three actions:
- Intelligent gap analysis: The agent ingests the new vendor alert data alongside Expel’s existing detection database and recent investigative actions. Using an LLM-powered semantic similarity search, it compares the new alert against our current rules to ask: Do we already have layered logic that covers this specific behavior?
- Decision engine: If a gap exists, the agent navigates a decision tree. It systematically decides whether to generate a brand new detection rule, modify an existing rule to capture the nuance, or ensure redundant detections are consolidated by merging similar rules for clearer alert explanations. It can also generate a recommendation to tune the alert.
- Automated rule drafting: The agent can then write code if it’s required. It generates a syntactically correct detection in a domain specific language YAML rule, maps the behaviors to MITRE tactics and techniques, and automatically calls a validation tool to fix any formatting errors before outputting the final draft for human validation.
Efficacy you can trust
Expel’s high standards for efficacy demand an expert human-in-the-loop to review and validate these changes. To guarantee high-fidelity for any Expel-validated detections, every rule must pass syntax and efficacy tests.
The agent sends every AI-generated candidate to our experts for this final review, ensuring the underlying logic is sound, preventing false-positive floods, and guaranteeing our layered defenses remain highly accurate.
We deliver a comprehensive security outcome. You get the benefits of this machine-speed adaptation without your internal team, or ours, having to learn how to prompt an AI or review YAML code.
What this means for you
We built this agent to drive measurable outcomes for our customers and our SOC. The detection agent is designed to deliver:
- Faster time to coverage: We’re moving from weekly manual reviews to near real-time adaptation. Our goal is to deploy layered coverage for novel vendor behaviors in seven days or less.
- Expanded detection recall: By systematically learning from all relevant new vendor alerts, we’ve seen over a 50% increase in unique vendor alert signatures covered.
- Production-grade reliability: By using a scoped, deterministic workflow, the agent is built to maintain 99% availability with a latency of no more than ten minutes per alert.
With the detection agent, Expel is proactively leveraging vendor innovations to seal gaps in our defense-in-depth strategy faster than ever before—ensuring that as your vendors evolve, your protection evolves right alongside them.