TL;DR
- When an alert fires, our Expel analysts need to act fast on your behalf—but digging through a mountain of uncontextualized vendor data to understand the full story takes time.
- Our new AI-powered related alert summaries feature uses LLMs within Expel Workbench™ to automatically analyze and transform disparate source alerts into a clear, chronological narrative.
- By shifting the heavy lifting of data correlation to Ruxie, our analysts get immediate insight into attack stages and severity, allowing us to respond to your threats faster while giving you full transparency into our investigations.
An alert drops into Expel Workbench™, and the clock immediately starts ticking for our MDR analysts. They see the lead alert, but to understand the real scope of the threat to your environment, they have to answer the hardest questions manually: What else happened before this? Are these other source alerts actually related, or just noise? What MITRE ATT&CK stage are we looking at?
Historically, finding those answers meant our team had to pivot through raw logs, jump between disparate tools, and squint at a wall of uncontextualized investigative action outputs. It’s a race against time where the friction of gathering scattered data actively fights against the ability to make a rapid, accurate decision on your behalf.
Amplifying our experts with AI-powered related alert summaries
Gathering and parsing raw data is the exact opposite of decisiveness; it drains cognitive load and slows down response times. That’s why we built our newest Ruxie power-up: related alert summaries.
This extends Ruxie’s capabilities to automatically transform that raw data into a clear, human-readable, chronological narrative right at the start of the workflow instead of handing our analysts a buried, chaotic list of related source alerts. It tells the story of the attack immediately, so our team doesn’t have to piece it together manually before taking action to protect your business.
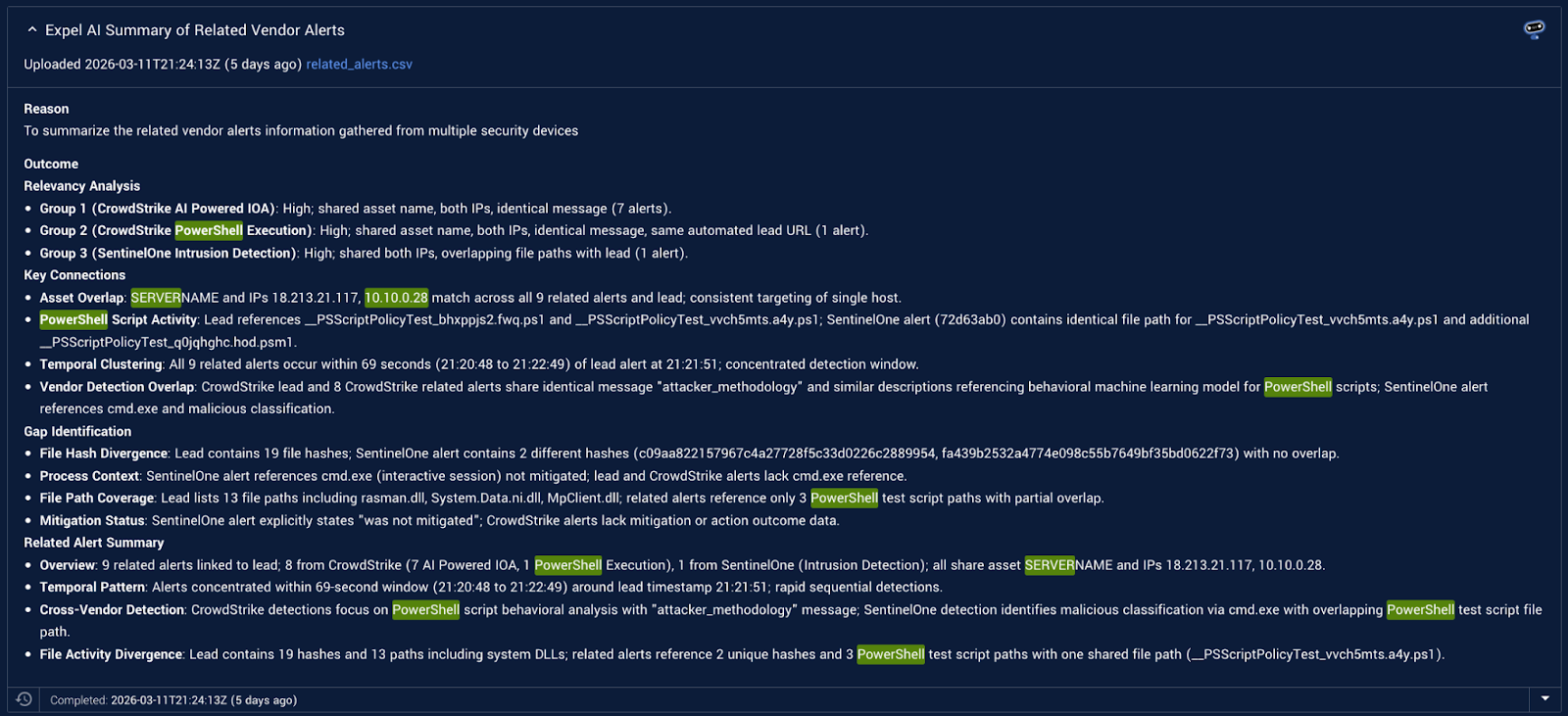
Now, when a lead alert fires, Ruxie automatically identifies and retrieves all relevant alerts from your connected vendor technologies. An LLM then processes this data with curated prompt engineering, specifically focusing on identifying the intent, risk level, and timeline of events.
The output is a concise narrative—including a chronological timeline and a gap analysis of your visibility—populated directly in Workbench in place of the old, uncontextualized alert lists.
Faster context means better decisions
By automatically surfacing the who, what, and when of an attack for our SOC, this new power-up directly enhances your security posture and empowers your team with unmatched visibility.
- Speed and understanding: Moving from raw, scattered source alerts to deep understanding in seconds drastically lowers our mean time to decision (MTTD), allowing us to contain threats in your environment faster.
- Noise reduction: The LLM automatically sifts through the chatter, separating false alarms from real threats while acting as a trusted advisor to highlight critical visibility blind spots or gaps in your coverage.
- Transparency and trust: The AI provides a clear, human-readable explanation directly in the Workbench alert details. Because you have access to Workbench, you see the exact same narrative and facts our analysts used to make their decisions.
The bottom line
At Expel, our core philosophy remains unchanged: while others use AI to cut corners or replace human judgment, we use it to sharpen our tools and amplify human intuition. Related alert summaries handles the monotonous, time-consuming grunt work of log analysis. This ensures that our MDR experts have the exact context they need to see, stop, and explain threats to you instantly.
What’s next
This launch is just one piece of our ongoing mission to integrate high-quality, trustworthy AI components into Ruxie. Our AI engineering team is already in the lab cooking up even more power-ups designed to reduce triage times and eliminate false positives, with new capabilities rolling out in the coming weeks. Stay tuned.