TL;DR
- We are officially launching a transparent, co-managed service for Splunk and Microsoft Sentinel customers that injects our elite MDR expertise directly into your existing environment.
- Our service eliminates the hidden operational burden of manual tuning and pipeline monitoring with MDR-caliber engineering that reduces false positives and closes coverage gaps.
- How are we different? We’ve removed the conflict of interest common in legacy MSSPs; you get full visibility into every rule we write, you own all the IP, and we never profit from your data volume.
You bought Splunk or Microsoft Sentinel because you needed visibility. You’re not getting the results you were expecting.
Not because the platforms are bad—they’re not. The problem is what happens after the contract is signed. Someone has to keep the data pipelines healthy, tune the detection logic, and make sure broken schemas don’t quietly create blind spots. That work is constant, technical, and easy to deprioritize when your team is already stretched thin. So rules go stale. Alerts spike. Engineers spend their time maintaining the SIEM instead of using it.
Legacy MSSPs offer to take some of that load—but their model creates new problems. They hide their detection logic. They charge per custom rule. And in most cases, they have a direct financial incentive to let your data volume grow rather than optimize it. You’re paying more and still not sure if your coverage is any good.
Expel Managed SIEM is built to fix that.
What we actually do
We don’t replace your SIEM. We work in it—bringing the same detection engineering behind Expel’s core MDR service into your existing Splunk or Sentinel environment.
That means writing detection rules tuned to your environment, not generic ones copied from a content pack. It means monitoring your data pipelines so we catch schema drift and ingestion gaps before they become coverage gaps. And it means continuous tuning to keep false positives from drowning your analysts.
Everything we do is visible to you. Every rule, every filter, every tuning decision—you can see it in real-time. No black box, no “trust us” logic hidden behind a vendor portal.
We also don’t take a cut of your data volume. Our incentive is to make your SIEM more effective and less expensive to run—not to watch the bill go up.
And any detection logic we build in your environment is yours. If you ever move on, you take your detections with you. No lock-in, no “customization tax.”
Two service components
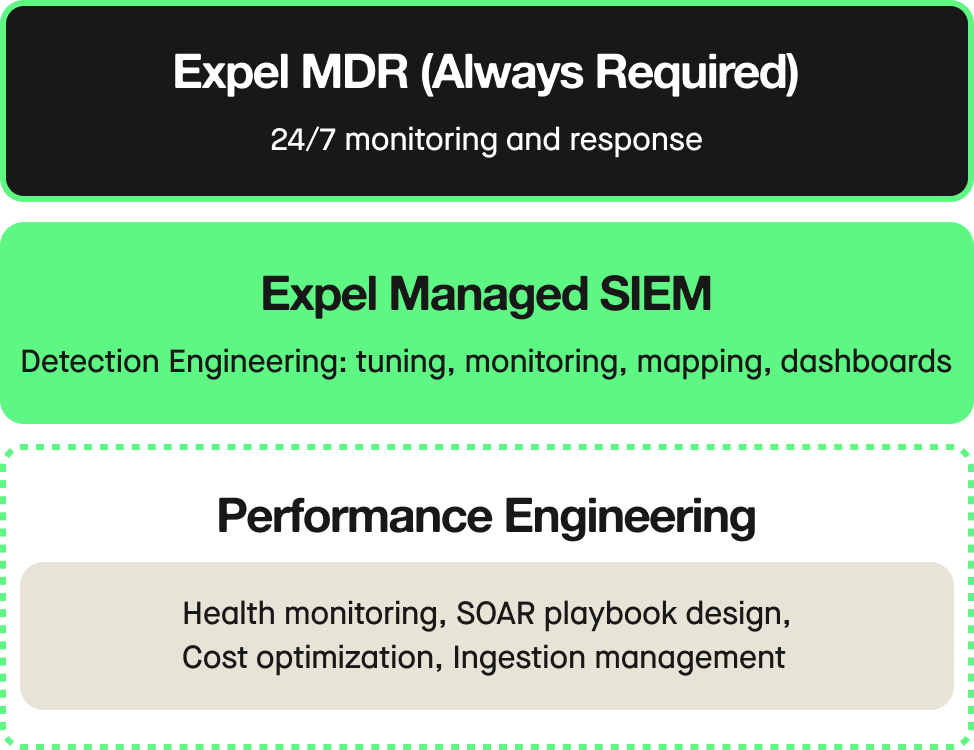
We know every security journey is different, which is why we’re offering two tiers of support to match your SOC’s maturity:
Detection engineering is for teams that need help getting more out of their existing setup. We handle rule development, logic tuning, false positive reduction, and pipeline monitoring—the ongoing work that keeps your detection program healthy.
Performance engineering goes deeper. In addition to everything in detection engineering, we take on active health remediation, SIEM cost optimization, and optional add-ons like SOAR playbook design and SIEM logic migration. This is for teams that want a hands-on operational partner, not just a service layer.
Why it matters now
Most security teams aren’t failing at detection because they lack talent. They’re failing because their SIEM has become a maintenance burden that crowds out the actual work. Rules age out. Pipelines break quietly. And the team that was supposed to be threat hunting is instead troubleshooting data ingestion.
Expel Managed SIEM is designed to take that operational load off your plate—so your team can focus on what they were actually hired to do.
If you’re running Splunk or Sentinel and want to see what your SIEM is actually capable of, let’s talk.
You can learn more about Expel and managed SIEM here, or check out our free guide to getting the most out of your SIEM (spoiler alert: it’s about detection quality).