Table of Contents
If your organization runs workloads in Amazon Web Services (AWS), Azure, or Google Cloud—or if you’ve adopted Kubernetes for container orchestration—you’re probably wondering how managed detection and response (MDR) handles these environments. Can traditional MDR even work in the cloud? Does it see inside containers? What about serverless functions and microservices?
The cloud presents unique security challenges traditional security approaches weren’t designed to handle. Workloads spin up and down in seconds, containers are ephemeral, identities shift constantly, and your attack surface extends across multiple cloud platforms. Traditional perimeter-based security simply can’t keep pace with this level of dynamism.
The good news? Modern MDR providers have evolved specifically to address cloud-native environments. Let’s explore exactly how MDR monitors, detects threats, and responds to incidents across your cloud and Kubernetes infrastructure.

MDR for cloud security
Does traditional MDR work in the cloud? The short answer is: not really. Traditional MDR was built for on-premises infrastructure with fixed perimeters, static servers, and predictable network topologies. Cloud environments operate fundamentally differently, requiring purpose-built detection and response capabilities.
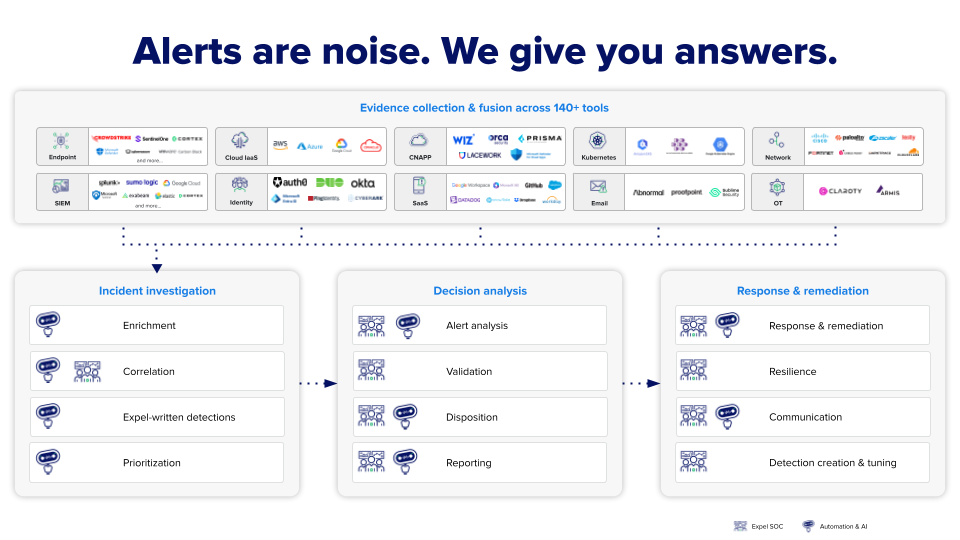
MDR monitors cloud environments by integrating directly with your cloud platforms and security tools to provide continuous visibility and threat detection. Expel Managed Detection and Response (MDR) integrates directly with AWS, Azure, and Google Cloud, as well as additional cloud security technology.
Here’s how cloud-specific MDR works in practice:
Control plane monitoring
Cloud MDR starts with monitoring the control plane—the administrative layer where users manage cloud resources, configure services, and control access. It then ingests events and log data from Google Cloud, AWS, and Azure and enriches it with customer-specific context such as the type of environment (e.g., production, development) or user (e.g., admin) to hone detection based on risk and expected behaviors.
This monitoring catches critical security events like:
- Suspicious login attempts to cloud admin consoles
- Unusual API calls that could indicate reconnaissance
- Changes to security groups or firewall rules
- Creation of new admin accounts or privilege escalations
- Resource sharing with external accounts
API integration
Rather than relying on agents, cloud MDR leverages API connections to cloud platforms. This approach provides comprehensive visibility without requiring software installation on every cloud workload.
Cloud-native detection rules
Generic detection rules don’t work well in cloud environments. Expel layers on our own detections, ingesting security signal from cloud-native services and writing custom detections tailored to each cloud provider from the logs in the cloud admin control plane. In fact, 98% of cloud security incidents seen by Expel’s SOC analysts were caught by Expel-written detection rules.
Multi-cloud visibility
Most organizations don’t use just one cloud platform. Approximately 80% of organizations operate in multi-cloud or hybrid cloud environments, and many lack the internal expertise needed to effectively manage the security of their cloud configurations. MDR addresses this by providing unified monitoring across all your cloud platforms, presenting security data in a single interface for faster analysis and response.
Can MDR monitor Kubernetes?
Absolutely—and Kubernetes monitoring has become essential as container adoption accelerates. According to a 2022 report from KBV Research, the container application market is expected to grow to $12B by 2028, with Kubernetes driving the majority of the spend.
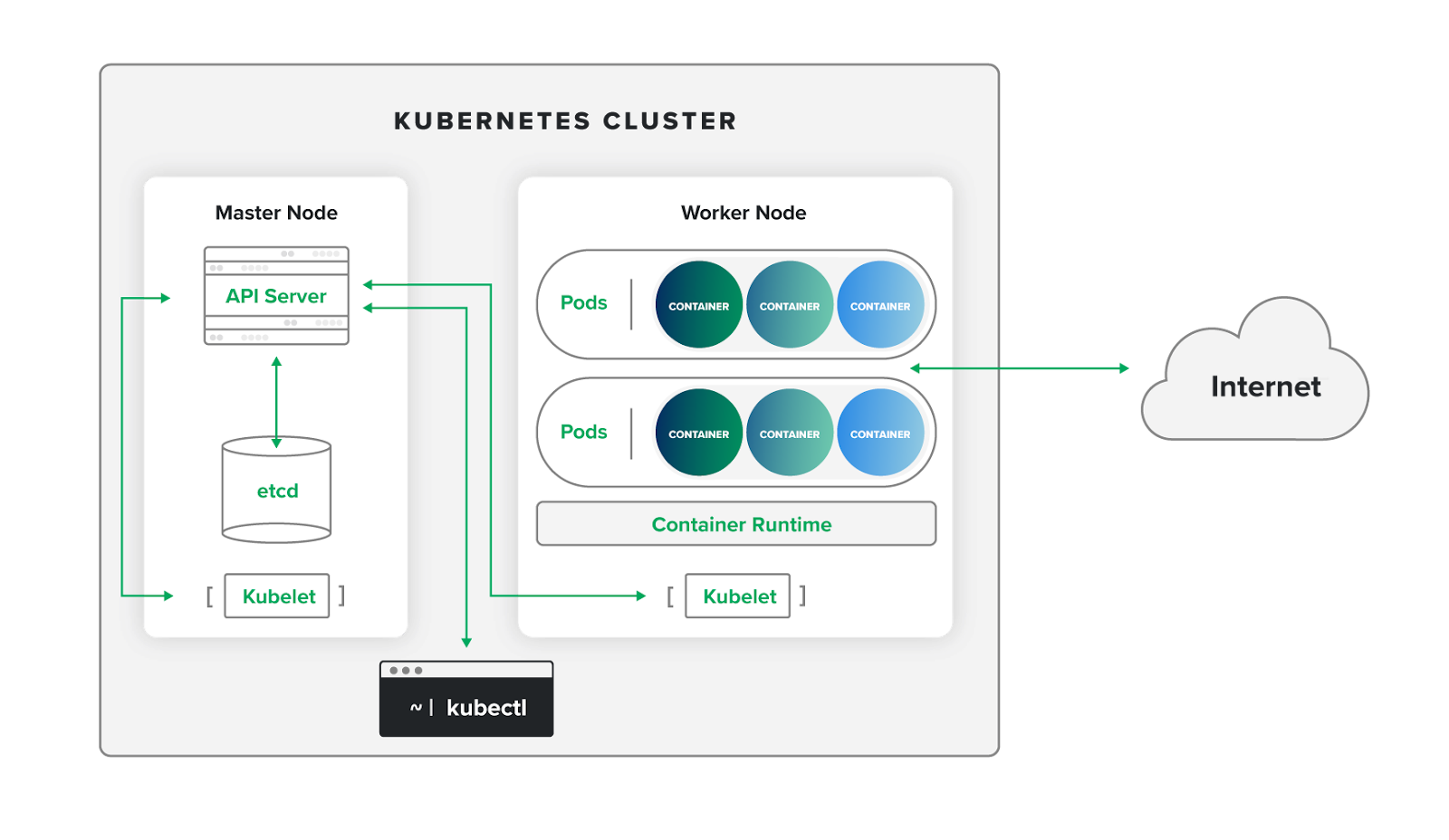
Kubernetes presents unique security challenges that require specialized monitoring capabilities. As a container orchestration platform, Kubernetes provides a versatile environment to build and run cloud-native applications, but given its role in orchestrating communications and moving resources across the network, Kubernetes is a powerful technology with a high potential for misuse.
The Kubernetes security challenge
Why is Kubernetes so difficult to secure? Several factors make it particularly challenging:
Ephemeral nature: Containers and pods are designed to be short-lived and easily replaceable. They’re created and destroyed continuously as needed for scalability and high availability. Along the way, patches and changes get deleted as well. This constant churn makes traditional security monitoring ineffective.
Complex architecture: The same modular design that makes cloud-native development so agile also introduces numerous potential vulnerabilities throughout its architecture. A single compromised element can allow attackers to gain access to data and services across the environment.
False positive volume: Kubernetes monitoring tools often lack the context needed to understand application-specific behaviors such as auto-scaling activity, or short spikes in CPU or memory usage. This leads to overwhelming alert volumes that bury real threats.
How MDR monitors Kubernetes
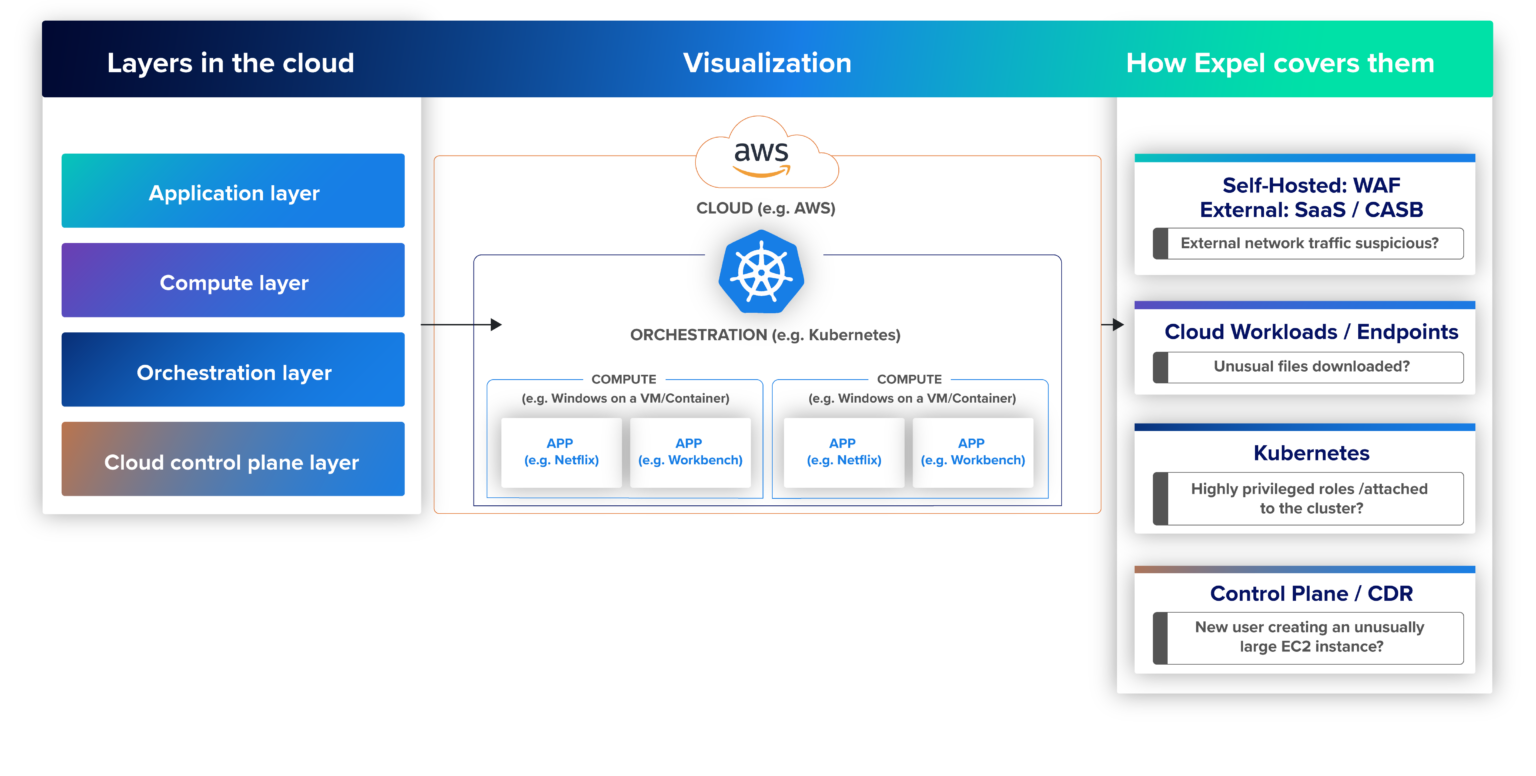
MDR for Kubernetes should monitor your clusters, allowing you to adopt Kubernetes at scale without security concerns. The service provides comprehensive coverage across three critical layers:
Control plane security: MDR integrates with Amazon Elastic Kubernetes Service (EKS), Azure Kubernetes Service (AKS), and Google Kubernetes Engine (GKE) infrastructure, analyzing Kubernetes audit logs and applying custom detection logic to alert on malicious or interesting activity.
Configuration monitoring: To help organizations stay ahead of pervasive misconfigurations, Expel MDR for Kubernetes identifies cluster misconfigurations and references the Center for Information Security (CIS) Kubernetes benchmark for best practices, for example.
Runtime security: MDR integrates with container security vendors including CrowdStrike, Wiz, Lacework, and Prisma Cloud Compute Edition to provide visibility into what’s happening inside running containers.
Real-world Kubernetes threats
What specific threats does MDR detect in Kubernetes environments? Common attack patterns include:
Cryptojacking: Threat actors frequently breach Kubernetes clusters and hijack their cloud resources to mine cryptocurrency. Tesla experienced this type of attack in 2018, demonstrating that even sophisticated organizations are vulnerable.
Exposed API endpoints: MDR monitors for anonymous requests to Kubernetes APIs, which could indicate reconnaissance or exploitation attempts.
Privilege escalation: Default service accounts are one of the most common ways to escalate privileges in Kubernetes. MDR detects when default service accounts are granted privileged roles like admin or cluster-admin.
Unauthorized container images: MDR monitors for pods running images from untrusted registries, which could indicate an attacker deploying malicious containers in your environment.
Cloud-native threat detection
Cloud-native environments require fundamentally different detection approaches than traditional infrastructure. Here’s how MDR identifies threats specific to cloud and container environments:
Workload protection
Cloud workload protection monitors what’s happening inside your cloud instances, containers, and serverless functions as they run. According to external security experts, runtime security refers to the continuous, end-to-end monitoring and validation of all activity within containers, hosts, and serverless functions.
MDR provides this protection by:
- Monitoring processes running inside containers for suspicious activity
- Detecting unusual network connections from cloud workloads
- Identifying file system modifications that could indicate compromise
- Alerting on privilege escalation attempts within containers
Behavioral analysis
Because cloud environments are so dynamic, signature-based detection doesn’t work well. Instead, MDR uses behavioral analysis to establish baselines of normal activity and detect deviations. This catches threats that wouldn’t trigger traditional security rules, like:
- A container suddenly consuming unusual amounts of CPU (potential cryptojacking)
- Workloads communicating with unexpected external IP addresses
- Admin accounts accessing resources they don’t normally touch
- Rapid resource creation that could indicate automated attack tools
Misconfiguration detection
Cloud misconfigurations represent one of the most common and exploitable weaknesses in cloud environments. Kubernetes is particularly prone to exploitable configuration errors—more than half of organizations using Kubernetes detected a misconfiguration in 2023.
Common misconfigurations MDR detects include:
- Overly permissive IAM roles and policies
- Public-facing storage buckets containing sensitive data
- Security groups allowing unrestricted access
- Containers running with excessive privileges
- Missing encryption on data at rest or in transit
Infrastructure as code monitoring
Modern cloud environments are deployed through infrastructure as code (IaC). MDR can integrate with your deployment pipelines to catch security issues before they reach production, identifying vulnerabilities in Terraform, CloudFormation, or other IaC templates.
Cloud security posture management integration
MDR providers often integrate with Cloud Security Posture Management (CSPM) tools to provide comprehensive visibility into configuration risks. CSPM platforms continuously assess your cloud environment against security best practices and compliance frameworks, identifying misconfigurations before they can be exploited. When combined with MDR’s threat detection capabilities, CSPM findings inform both proactive hardening and active threat response.
MDR for AWS, Azure, and Google Cloud
Platform-specific coverage matters because each major cloud provider implements security controls differently and generates distinct types of security telemetry. Here’s how MDR handles the three major cloud platforms:
AWS security monitoring
For AWS specifically, MDR monitors:
- AWS CloudTrail logs for API activity and administrative actions
- Amazon GuardDuty findings for threat detection
- AWS Config for configuration compliance
- VPC Flow Logs for network traffic analysis
- S3 bucket access and permissions
- IAM role usage and credential access
Azure security monitoring
Azure environments require monitoring of:
- Azure Activity Logs for subscription-level events
- Azure AD sign-in logs for identity-based threats
- Microsoft Defender for Cloud alerts
- Network Security Group flow logs
- Key Vault access for secret management
- Azure Resource Manager operations
Google Cloud monitoring
For Google Cloud, MDR ingests and analyzes:
- Cloud Audit Logs for administrative activity
- VPC Flow Logs for network visibility
- Security Command Center findings
- IAM policy changes
- Compute Engine instance activity
- Cloud Storage bucket access patterns
Multi-cloud correlation
The real power of cloud MDR comes from correlating activity across platforms. Expel MDR, for example, uses APIs to ingest and normalize security data throughout our customers’ cloud environments. We present it in a single interface for our own security teams and for our customers.
This unified view enables detection of sophisticated attacks that span multiple clouds. For example:
- An attacker compromises credentials in AWS, then attempts to use them in Azure
- Lateral movement from a Google Cloud compromised instance to on-premises infrastructure
- Data exfiltration coordinated across multiple cloud storage services
Oracle Cloud infrastructure
In March 2025, Expel became the first MDR provider to offer coverage for Oracle Cloud Infrastructure (OCI), demonstrating the expanding scope of cloud MDR capabilities.
Container security monitoring
Container security extends beyond just Kubernetes orchestration to include the entire container lifecycle and runtime environment. MDR provides security at multiple stages:
Image security
Before containers even run, MDR monitors for:
- Vulnerable base images from public registries
- Images with known CVEs or outdated dependencies
- Containers with hardcoded secrets or credentials
- Overly large container images with unnecessary packages
Runtime monitoring
Once containers are running, MDR leverages Cloud Workload Protection Platform (CWPP) capabilities and runtime security tools to monitor behavior. According to external security research, runtime security tools monitor and send alerts for suspicious changes in processes, network connections, or file system read/writes within cloud-native infrastructure.
This includes detecting:
- Container escape attempts
- Processes spawning inside containers that shouldn’t be there
- Unauthorized network connections
- File system modifications
- Privilege escalation within containers
Orchestration security
For Kubernetes specifically, MDR monitors the orchestration layer by analyzing audit logs. Just about everything that happens in Kubernetes automatically produces an audit log, and security teams can monitor those logs for anomalous signs.
Key orchestration events MDR watches for:
- Pod creation from unexpected sources
- Role binding modifications granting excessive permissions
- ConfigMap or Secret access by unauthorized service accounts
- Network policy changes that could enable lateral movement
Serverless security
Serverless functions present unique monitoring challenges because they’re extremely ephemeral—they may only exist for milliseconds. MDR handles serverless security by:
- Monitoring function invocation patterns for anomalies
- Analyzing function execution logs for suspicious activity
- Tracking IAM permissions assigned to functions
- Detecting functions accessing unexpected resources
Key takeaways
MDR has evolved far beyond traditional endpoint security to provide comprehensive coverage for cloud-native environments. Modern MDR services integrate directly with AWS, Azure, Google Cloud, and OCI, monitoring control planes, detecting misconfigurations, and correlating threats across multi-cloud deployments.
For Kubernetes environments, MDR provides specialized monitoring across control plane, configuration, and runtime security layers. This addresses the unique challenges of container orchestration, including the ephemeral nature of pods, complex architectures, and high false positive rates.
Cloud-native threat detection relies on behavioral analysis rather than signatures, establishing baselines of normal activity to identify deviations. MDR monitors everything from API calls and admin activity to processes running inside containers and serverless functions.
The most effective cloud MDR integrates with container security vendors and cloud-native security tools you already use, layering additional detections and expert analysis on top of your existing investments. This brings-your-own-tech approach maximizes ROI while providing comprehensive protection across your entire cloud attack surface.
When evaluating MDR providers for cloud and Kubernetes security, look for platform-specific expertise, multi-cloud correlation capabilities, integration with leading cloud security tools, and proven experience detecting cloud-native threats at scale.