Managed detection and response
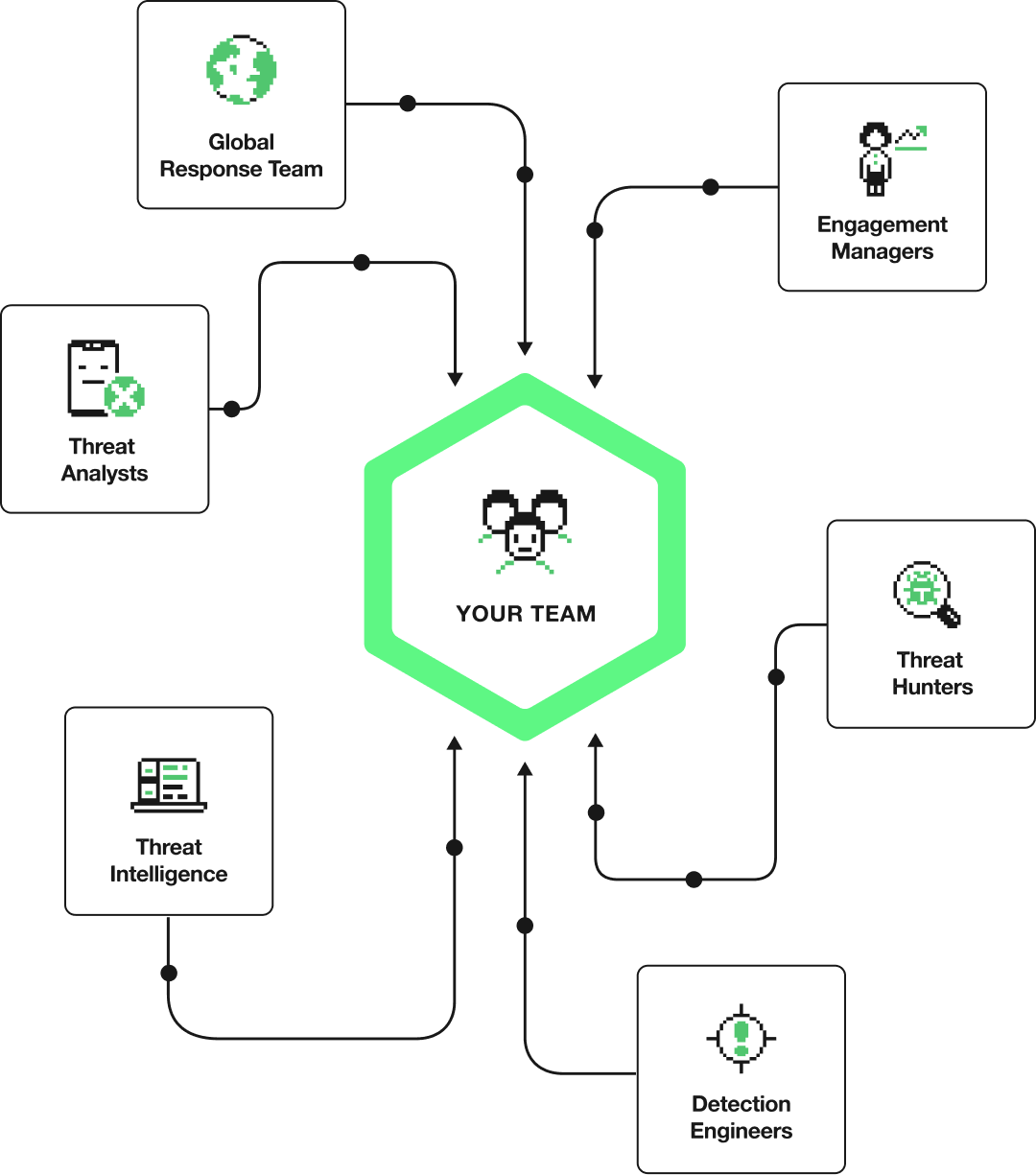
Your tools provide the signal. Our detections, AI, and analysts do the rest. 24x7 SecOps that fits the way you work.
WHAT YOU ACTUALLY GET
Security outcomes without the overhaul
Connect to Expel Workbench™. Ruxie investigates. Our analysts decide. You don't have to rebuild a thing.
HOW WE DO IT
Our tech makes us fast.
Our people make us accurate.
AI for speed. Humans for judgment. Remediated in 14 minutes.
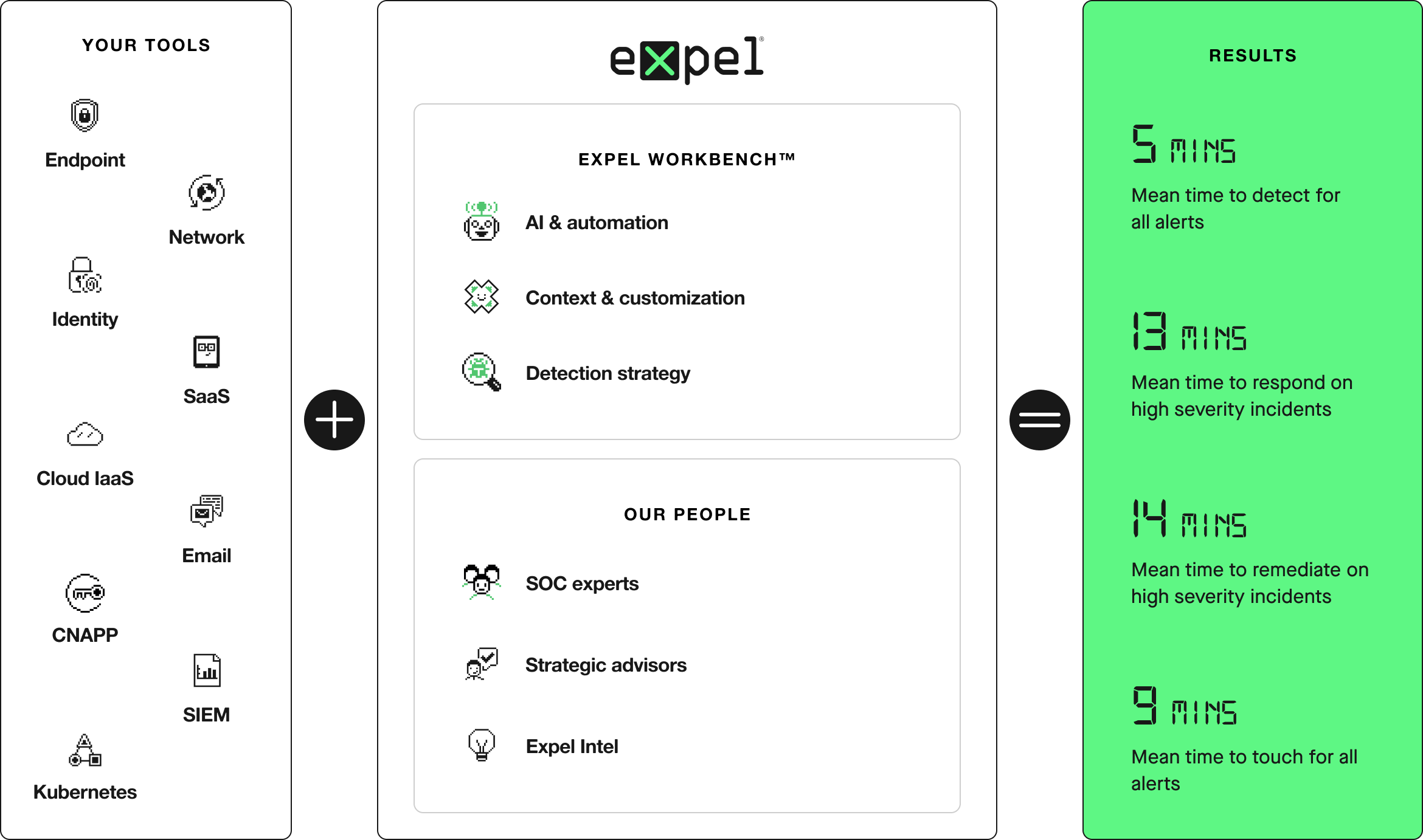
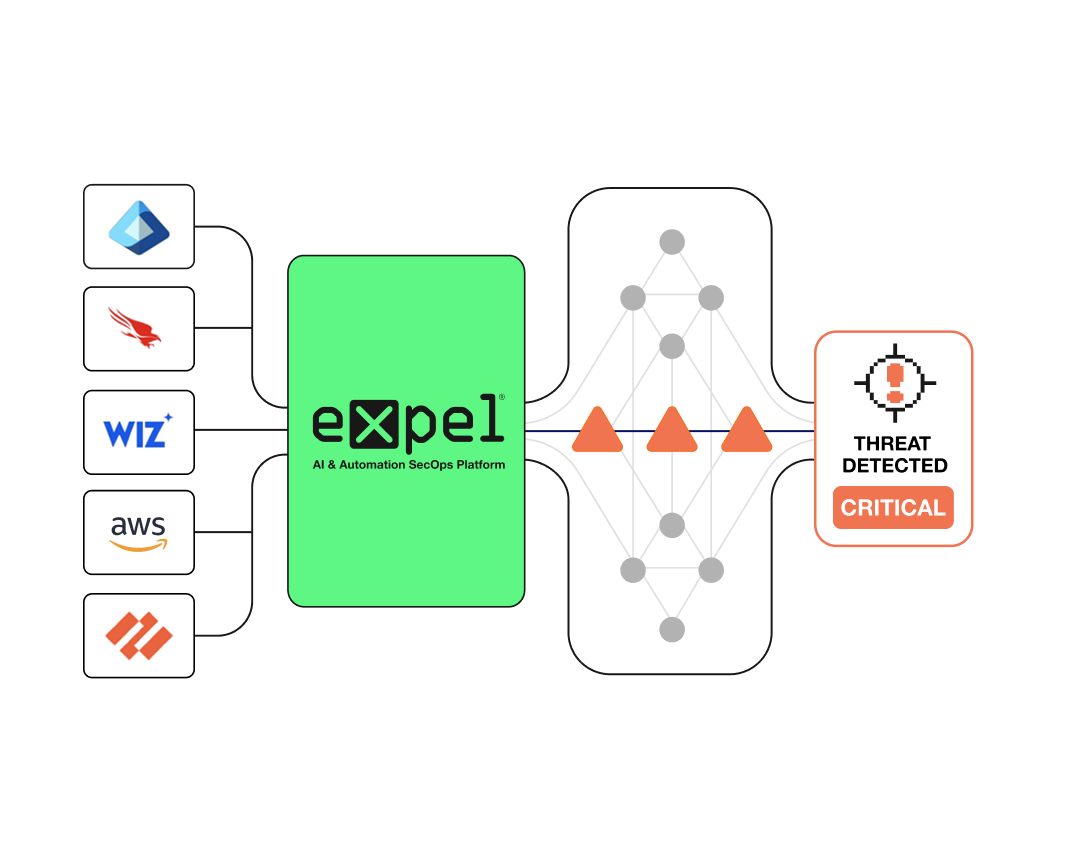
STEP 1: CONNECT
Up and running in minutes with your own tech
No agents. No rip-and-replace BS. Expel plugs into your existing—and future—security stack to cover all your attack surfaces.
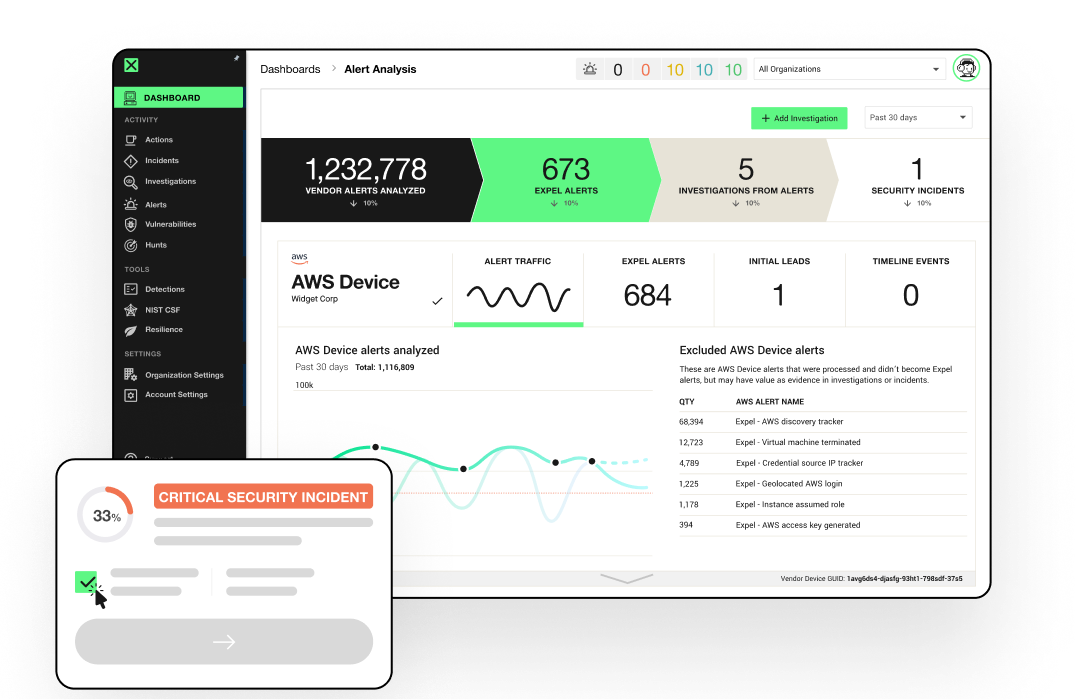
STEP 2: DETECT
No gaps. No blind spots. Nowhere to hide.
Dedicated detection engineers see across all our customers and use AI agents to build rules that correlate across every attack surface. Continuous improvement.
STEP 3: INVESTIGATE
AI that investigates. Analysts who decide.
Ruxie—AI and automation engine—triages millions of events and assembles the context. Our analysts take it from there. Machine speed, human judgment—no shortcuts.
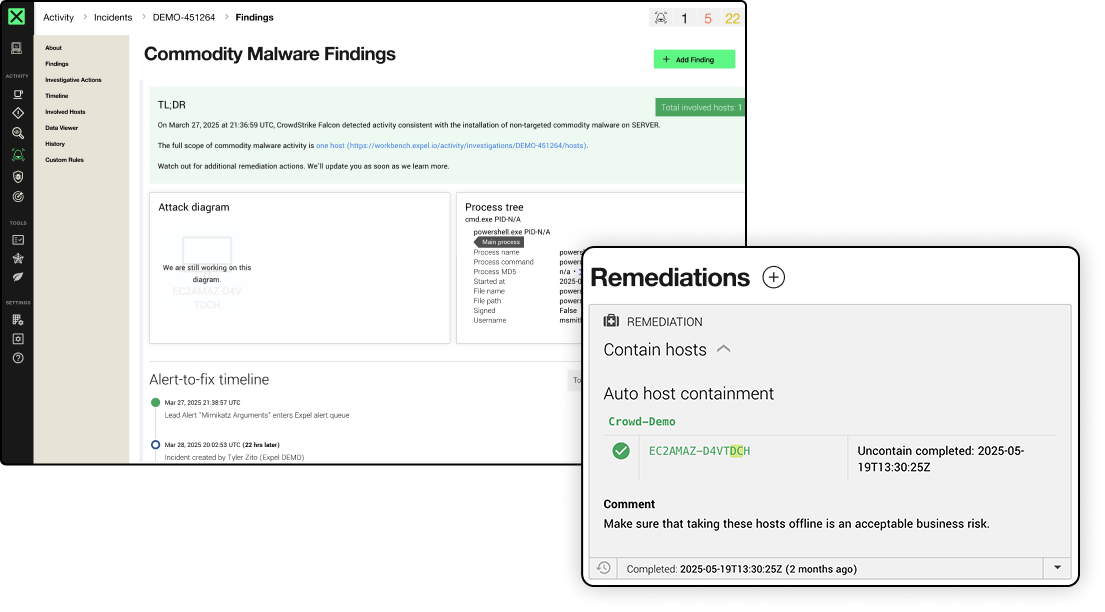
STEP 4: RESPOND
Remediated. Not just flagged.
Our team and technology don’t stop at the alert. Automated remediation, human-executed response, full audit trail.
STEP 5: IMPROVE
Security that gets stronger every day
Every incident makes your detections sharper. Every review makes your posture stronger. We don’t just run your SOC. We help you build a better one.
STEP 1: CONNECT
Up and running in minutes with your own tech
No agents. No rip-and-replace BS. Expel plugs into your existing—and future—security stack to cover all your attack surfaces.
STEP 2: DETECT
No gaps. No blind spots. Nowhere to hide.
Dedicated detection engineers see across all our customers and use AI agents to build rules that correlate across every attack surface. Continuous improvement.
STEP 3: INVESTIGATE
AI that investigates. Analysts who decide.
Ruxie—AI and automation engine—triages millions of events and assembles the context. Our analysts take it from there. Machine speed, human judgment—no shortcuts.
STEP 4: RESPOND
Remediated. Not just flagged.
Our team and technology don’t stop at the alert. Automated remediation, human-executed response, full audit trail.
STEP 5: IMPROVE
Security that gets stronger every day
Every incident makes your detections sharper. Every review makes your posture stronger. We don’t just run your SOC. We help you build a better one.
On-demand
See Expel MDR services in action.
Watch exactly how we find and contain threats before they become your problem. No sales pitch. Just the real thing.
STRAIGHT FROM THE SOC
Don’t take our word for it.

“Expel stood out immediately because it isn’t a black box—we can see exactly what they see. This transparency, along with how Expel interacts with our logs directly through Workbench, represented a significant advantage for us.”

“Out of a million events, I would say 99.5% of them are filtered out in triage by AI and machine learning [and the Expel team] before we actually need to have eyes on the actual issue.”
“Our engineers manage 50% fewer investigations than they previously handled, allowing them to focus on higher-value work.”
OUR FEATURES
What you get with Expel
managed detection and response
Real security operations, not just alert forwarding
24×7 SOC monitoring
Real-time triage and investigation around the clock. Answers without noise.
AI-powered investigation
Ruxie triages millions of events so analysts can focus on the work that requires human judgment.
Auto remediation
Automated containment stops lateral movement before it spreads.
Threat intelligence
Bulletins and on-demand investigations from our intel team track real adversaries.
SIEM coverage
Your SIEM, your call. We can simply pull your data into Workbench or manage your SIEM entirely.
Metrics and reporting
Real-time visibility on every alert, plus monthly reports that show security posture improvement over time.
Threat hunting
Hypothesis-driven hunts across your environment. Find threats before they find you.
Strategic guidance
Regular reviews, resilience recommendations, and honest advice on reducing risk.