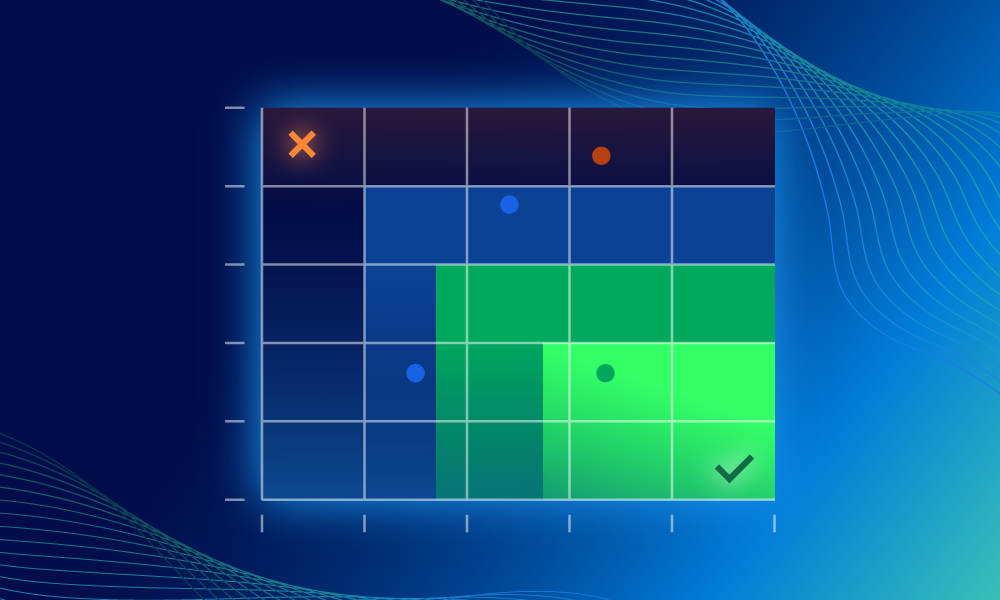
Detections
Data & research | 9 min read
Measuring incident quality to drive detection strategyWe’re sharing our mathematical process on how we calculated incident strength to help identify and prioritize detection improvements.
Product | 4 min read
How we built it: Expel’s latest RMM detectionsExpel is leveling up its detection capabilities against remote monitoring and management tools (RMMs). Here's how we're doing it.
Threat intel | 12 min read
ClearFake gets more evasive with new living off the land (LOTL) techniquesClearFake's latest campaign uses fake CAPTCHAs and social engineering trick victims into installing malware, and it's getting more evasive.
Threat intel | 12 min read
Planned failure: Gootloader’s malformed ZIP actually works perfectlyGootloader malware contains a deliberately malformed ZIP archive to bypass detection, but can also be identified by its unique formatting.
Product | 4 min read
New Expel AI upgrade: “Pop the hood” on our detection strategiesExpel added new AI-generated descriptions to our detection rules, written in plain English, to improve transparency and understanding.
MDR | 4 min read
Expel + AWS Security Hub: Turning findings into actionExpel is a partner for the new AWS Security Hub. We layer detection engineering on top of its finding to solve prioritization problems.
MDR | 3 min read
Stop counting integrations. Start counting what matters.With integrations and security, quantity is not the same as quality. Integration counts are a vanity metric that make you less secure.
SOC | 3 min read
Stories from the SOC: When threats come from inside the houseMDR email coverage is more than just flagging spam to contain threats. Here's what happens when malicious emails come from within an org.