Table of Contents
When you invest in managed detection and response (MDR), you’re not just getting 24×7 monitoring—you’re gaining access to threat intelligence that helps you understand and defend against the attacks targeting your organization. But what exactly does that intelligence look like? How does MDR threat intelligence differ from generic threat feeds? And most importantly, how does it actually help you stop attacks?
The distinction matters because not all threat intelligence is created equal. Many organizations subscribe to threat feeds that deliver endless streams of indicators of compromise (IOCs)—IP addresses, file hashes, domains—without context about whether those threats are relevant to their environment. The security industry is drowning in threat feeds that sound impressive but don’t actually help you stop attacks.
Quality MDR providers deliver something different: actionable intelligence derived from real-world incident data, tailored to your environment, and integrated directly into your security operations. Let’s explore exactly what threat intelligence capabilities come with modern MDR services.

MDR threat intelligence
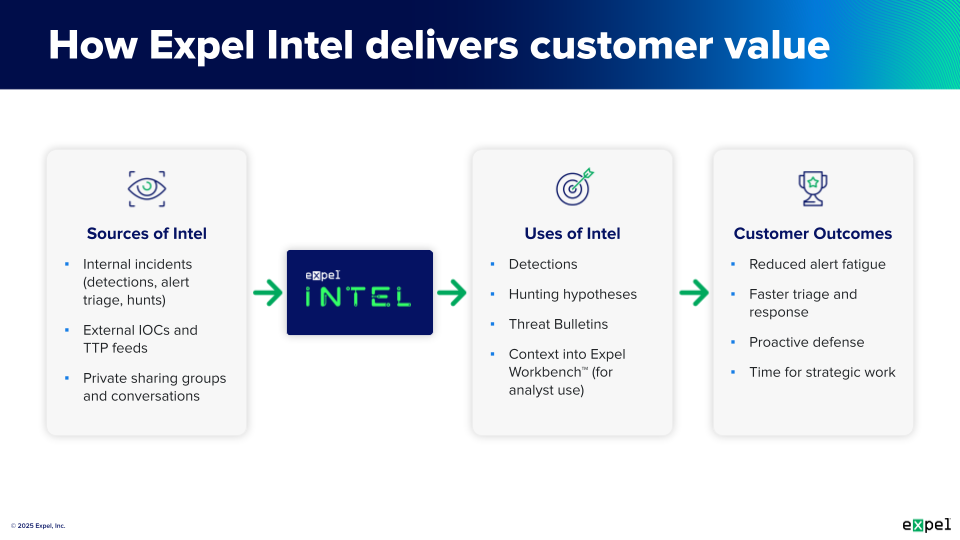
MDR threat intelligence encompasses multiple intelligence types working together to inform both strategic decisions and tactical responses. Unlike standalone threat feeds that simply list indicators, MDR intelligence provides context, analysis, and direct application to your security operations.
At its foundation, MDR threat intelligence comes from a unique vantage point: visibility across hundreds or thousands of customer environments. MDR Providers are in a unique position when it comes to turning threat intelligence into information that can proactively aid their customers.
This intelligence manifests in three primary forms, each serving different stakeholders and purposes:
Strategic intelligence provides high-level insights into the threat landscape that inform long-term security planning and investment decisions. According to external cybersecurity experts, strategic threat intelligence focuses less on technical details and more on the underlying meaning behind technical threat intelligence data. This intelligence helps executives understand which threats matter most to their industry, how the threat landscape is evolving, and where to allocate security resources.
Operational intelligence bridges strategic and tactical intelligence by providing context about attacker campaigns, tactics, techniques, and procedures (TTPs), and the motivations behind attacks. This intelligence helps security teams understand the broader picture of threats targeting their organization, enabling them to prioritize defenses and anticipate the attacker’s next moves.
Tactical intelligence delivers immediately actionable technical details—indicators of compromise, malware signatures, and specific attack patterns that feed directly into detection tools. This is the “meat and potatoes” intelligence that enables real-time threat detection and response.
MDR providers deliver all three intelligence types, but the real value comes from integrating them into your daily operations rather than just sending reports that sit unread in inboxes.
What threat research does MDR provide?
MDR providers conduct continuous threat research that directly improves your security posture. This research takes multiple forms, from analyzing malware samples to tracking attacker campaigns to developing new detection logic based on emerging threats. For well-rounded coverage, your MDR provider should offer standing threat intelligence reporting on a regular cadence, as well as breaking news and updated information as events happen in real time.
Expel, for example, provides quarterly threat reports, annual threat reports, threat bulletins, and ongoing threat intelligence via our blog. Quarterly and annual reports, much like quarterly business reports, reflect data and statistics from a select time period. They’re great for spotting long-term trends, and predicting what we might see next. It also provides customers with transparency on what kind of data your MDR provider is able to collect (and share) with you, to make our overall cybersecurity stronger together. It should cover all facets of cybersecurity, from specific threat types, threat groups, and all attack surfaces, like cloud infrastructure, for example.
When new vulnerabilities emerge—particularly critical ones like Log4j—MDR providers research the threat, assess risk to their customer base, and develop detection and response guidance. We notify our customers about big events as quickly as possible through a threat bulletin (essentially an urgent notice for things we hear about or see hitting our customer base).
Threat intelligence research is a blend of the two. Quality MDR providers will also maintain threat intelligence teams, whose job is to focus on diving into their data, the trends provided by news within the community, and provide guidance on how to protect yourself in real time. It may also include building profiles of threat actors targeting their customers, documenting their capabilities, preferred targets, typical TTPs, and indicators associated with their campaigns. This intelligence helps security teams understand not just what is attacking them, but who and why.
Vulnerability intelligence
When new vulnerabilities emerge—particularly critical ones like Log4j—MDR providers research the threat, assess risk to their customer base, and develop detection and response guidance. We notify our customers about big events as quickly as possible through a “threat bulletin” (essentially an urgent notice for things we hear about or see hitting our customer base).
How does MDR stay current with threats?
The threat landscape evolves constantly, with new attack techniques emerging weekly and major vulnerabilities appearing without warning. MDR providers stay current through multiple mechanisms that ensure their intelligence and detections remain effective against the latest threats.
Real-time incident data
The most powerful intelligence source is real-world incident data from across the customer base. When MDR analysts investigate and respond to attacks, they capture indicators, document attacker behavior, and identify new TTPs. This intelligence immediately informs detection engineering and gets shared across all customers.
Dedicated threat intelligence teams
Leading MDR providers maintain dedicated threat intelligence teams. These teams continuously analyze the threat landscape, research emerging threats, and translate their findings into improved detections and response playbooks.
MITRE ATT&CK alignment
The MITRE ATT&CK framework provides a common language and framework for understanding adversary behavior. MDR providers align their detections, threat hunting, and intelligence reporting to this framework, ensuring comprehensive coverage across the attack lifecycle.
By mapping their capabilities to MITRE ATT&CK, MDR providers can identify coverage gaps and prioritize development of detections for techniques commonly used by attackers. Our approach includes comprehensive detection coverage where we align our detection engineering with the framework to ensure broad coverage across the attack lifecycle.
Continuous detection updates
Threat intelligence doesn’t help if it just sits in reports. MDR providers continuously update their detection logic based on new intelligence. We’ve authored hundreds of user authentication detections and add more regularly, so our analytics are always current with the latest attacker TTPs.
External intelligence sources
While the most valuable intelligence comes from real-world incidents, MDR providers also leverage external threat intelligence sources, security research from the broader community, and collaborative intelligence sharing with other security organizations.
Threat bulletins from MDR
When significant threats emerge—zero-day vulnerabilities, widespread attack campaigns, or critical security incidents—MDR providers issue security advisories in the form of threat bulletins that provide immediate, actionable guidance. These advisories go beyond generic vulnerability announcements by including specific recommendations tailored to your environment and technology stack.
What threat bulletins include
Threat Bulletins outline information on emerging threats or zero-day attacks, either through our regular course of business, or when there’s a major industry threat announced.
The bulletin content typically includes:
- Attack information: Details about the threat, how it works, and what makes it dangerous
- Attacker attribution: When known, information about who is behind the attacks and their motivations
- Vulnerability details: Technical information about exploited vulnerabilities, including CVE identifiers and affected versions
- Indicators of compromise: Specific IOCs associated with the threat when available—domains, IP addresses, file hashes, network signatures
- Protective guidance: Concrete steps customers can take to protect their environments, including configuration changes, patches to apply, and detection opportunities
- Hunting results: For threats with available IOCs, MDR providers often run retroactive threat hunts across customer environments looking back in time (typically two weeks) to check for any compromise
Speed of response
Time matters when major threats emerge. Quality MDR providers issue bulletins within hours of learning about significant threats, not days or weeks later. This rapid response is only possible because MDR providers maintain dedicated teams monitoring the threat landscape 24×7.
MDR threat hunting
Threat hunting represents proactive threat intelligence in action—actively searching for threats that may have evaded automated detections rather than waiting for alerts to fire.
How MDR threat hunting works
The hunting process typically follows this workflow:
- Data collection: MDR providers collect 30 days worth of specific raw logs from your security tools
- Automated analysis: Using automation in the MDR platform, they produce a group of initial leads targeting specific areas of interest for further hunting and analysis
- Expert investigation: Human threat hunters identify abnormal activity, gather insights on blindspots, and analyze time ranges, behaviors, and activity patterns
- Immediate response: Any malicious activity discovered is instantly routed to the SOC team and yours for immediate response
- Reporting: All hunt findings and gaps uncovered are shared in a monthly report
Hunt techniques and intelligence
Hunt techniques aligned to your unique risks and MITRE ATT&CK, spanning from indicators of compromise (IOC) to new cloud user hunts. This means hunting isn’t random—it’s informed by:
- Current threat intelligence about active campaigns
- TTPs commonly used by threat actors
- Known vulnerabilities in your environment
- Behavioral anomalies that could indicate compromise
- Hypotheses developed from analyzing recent attacks
Intelligence from hunting
Threat hunting generates intelligence that flows in multiple directions. When hunts uncover threats that slipped past automated defections, that finding informs detection engineering to close the gap. When hunts reveal misconfigurations or blind spots, that intelligence helps improve defensive posture.
The role of human expertise
Human analysts are essential to threat hunting, leveraging their experience and instincts to improve cybersecurity efforts. Detecting threats also requires comprehensive data intelligence, both internal and external, including historical attack data, indicators of compromise, and threat feeds. This robust intelligence base enables security professionals to prioritize and focus on the most critical and high-risk threats.
Key takeaways
MDR threat intelligence is fundamentally different from generic threat feeds. Instead of overwhelming you with decontextualized indicators, quality MDR providers deliver strategic insights that inform security planning, operational intelligence about active threats targeting your industry, and tactical details that directly improve detection and response.
This intelligence comes in multiple forms: quarterly and annual threat reports that reveal patterns across the threat landscape, threat bulletins issued within hours when major threats emerge, continuous detection updates that keep your defenses current, and proactive threat hunting that uncovers threats your tools missed.
The intelligence is actionable because it’s integrated directly into your security operations—informing what the MDR provider monitors, how they detect threats, what they hunt for, and how they respond. You’re not left to figure out what to do with a list of IOCs; the intelligence automatically improves your protection.
Frequency varies by intelligence type. Threat bulletins arrive immediately when significant threats emerge. Quarterly reports provide regular analysis of trends and patterns. Detection updates happen continuously as new threats are identified. Threat hunting typically occurs monthly, though critical hunts may be triggered by specific threats or incidents.
When evaluating MDR providers, ask about their threat intelligence program. Do they conduct original research? How quickly do they issue threat bulletins? How is intelligence integrated into detections? Do they provide threat hunting, and if so, how is it informed by current intelligence? The answers reveal whether you’re getting true threat intelligence or just another feed.