Cloud detection and response (CDR) is a security approach that provides continuous monitoring, threat detection, and incident response specifically designed for cloud environments. CDR detects active threats in real time, including credential abuse, cryptomining, lateral movement, and container escape across IaaS, PaaS, and SaaS layers.
Why do cloud environments need dedicated detection and response?
Cloud security is part of any mature security program, and CDR is the detection and response layer within it. Cloud environments generate a fundamentally different type of security telemetry than endpoints or networks. AWS CloudTrail, Google Cloud Audit Logs, Azure Activity Logs, Kubernetes audit logs, and SaaS audit events don’t look like anything a traditional SIEM or EDR was designed to parse.
Without purpose-built cloud detection, attackers exploit this gap. They know that many security teams have strong endpoint coverage but weak cloud visibility, and they target that asymmetry. CDR closes it by continuously monitoring cloud-native log sources and applying behavioral detection logic built specifically for cloud attack patterns.
Dive into the challenges (and solutions) of complex cloud identity security with this candid, expert-led discussion.Expert insights on reigning in cloud identity security
How does CDR work?
CDR operates across the cloud stack using a combination of cloud-native log sources, behavioral analytics, and threat intelligence:
Log ingestion: CDR ingests telemetry from cloud-native sources: CloudTrail API activity, VPC flow logs, Google Cloud Audit Logs, Azure Monitor, Kubernetes audit logs, and SaaS audit events from platforms like Microsoft 365 and Google Workspace.
Behavioral detection: Unlike signature-based tools, CDR applies behavioral analytics to identify anomalous patterns, like an IAM role that suddenly starts creating new users, an EC2 instance making outbound connections to unusual endpoints, a service account accessing resources it has never touched before.
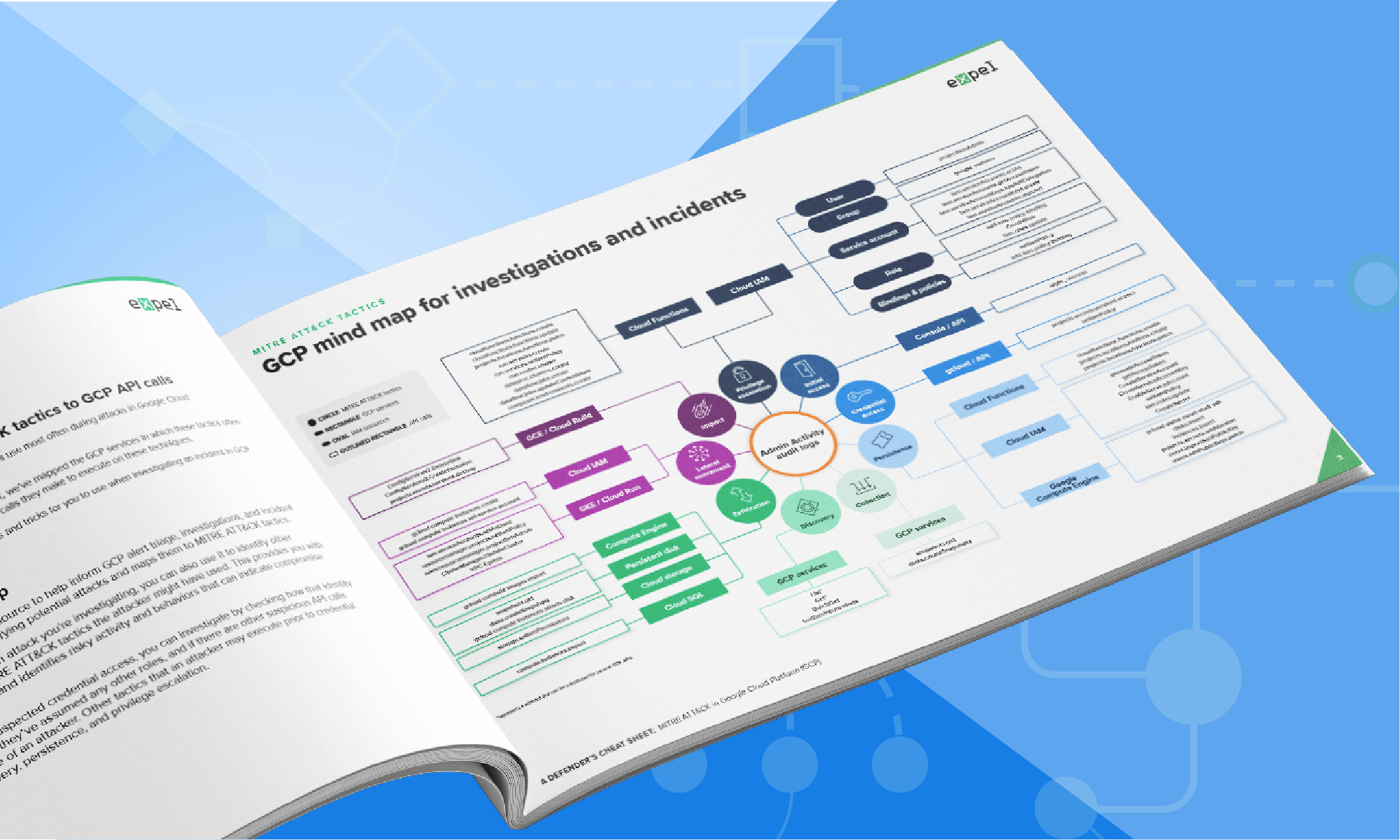
Threat intelligence correlation: CDR correlates observed behavior against known attacker techniques, mapping activity to frameworks like MITRE ATT&CK for cloud to surface the highest-fidelity threats first.
Human-led investigation and response: When CDR surfaces a confirmed threat, human analysts investigate context, determine scope, and execute a response, containing compromised accounts, isolating affected workloads, or blocking malicious activity.
What is the difference between CDR and CSPM?
This is the most important distinction in cloud security tool evaluation. Cloud security posture management (CSPM) and CDR address different problems and should not be treated as alternatives.
| Cloud detection and response (CDR) | Cloud security posture management (CSPM) | |
|---|---|---|
|
What it does |
Detects active threats in real time | Scans for misconfigurations |
|
When it operates |
Continuously, at run time | Point-in-time or scheduled |
|
What it finds |
Attackers actively in your environment | Configuration risks before exploitation |
|
Response capability |
Investigates and contains active threats | Recommends configuration fixes |
|
Primary use case |
Incident detection and response | Security posture management |
CSPM finds what’s exposed. CDR finds who’s exploiting it. Organizations that rely on CSPM alone have visibility into their configuration risk, but no real-time detection when an attacker exploits that risk or bypasses it entirely through credential theft.
The right approach combines both: CSPM to reduce your attack surface, CDR to detect and respond when threats materialize.
How does CDR relate to MDR?
CDR is a cloud-specific application of the MDR model. MDR providers that offer CDR extend their 24×7 monitoring and response capabilities specifically to cloud infrastructure, workloads, and identities, rather than limiting coverage to endpoints and network.
The key advantage of MDR-delivered CDR is that cloud telemetry doesn’t exist in a vacuum. An alert from CloudTrail becomes more meaningful when correlated with endpoint activity, identity behavior, and network data. MDR platforms that unify these signals provide dramatically faster and more accurate investigation.
How do you choose a CDR provider?
Key questions to ask when evaluating CDR providers:
Can they close your cloud expertise gap? Cloud platforms change constantly. Your CDR provider should have deep, current knowledge of AWS, Google Cloud, and Azure—not generic SIEM expertise applied to cloud logs.
What cloud log sources do they ingest? Confirm specific coverage for CloudTrail, VPC Flow Logs, Google Cloud Audit Logs, Azure Activity Log, Kubernetes audit logs, and SaaS audit events. Generic answers suggest surface-level coverage.
How do they handle data overload? Cloud environments generate enormous log volumes. Ask how the provider distinguishes high-fidelity signals from noise, and what their false positive rates look like in production.
What does their response capability look like? Detection without response is incomplete. Confirm that human analysts investigate alerts 24×7 and can take response actions, not just generate reports.
Frequently asked questions
What is the difference between CDR and CSPM?
CSPM and CDR are often discussed together but solve fundamentally different problems, and understanding that distinction is critical when building a cloud security program. CSPM scans your cloud environment for configuration weaknesses: an S3 bucket that’s publicly accessible, an IAM role with excessive permissions, a security group with port 22 open to the world. It’s a posture tool, and a valuable one. But it operates at a point in time, and it tells you what’s misconfigured, not what’s happening right now.
CDR provides continuous runtime monitoring. When an attacker uses a phished credential to log into your AWS account at 2am and starts spinning up EC2 instances for cryptomining, CSPM won’t catch that. CDR will, because it’s watching CloudTrail activity, correlating API calls against behavioral baselines, and flagging anomalies in real time. Both layers matter: CSPM reduces your attack surface, CDR detects when it’s being actively exploited.
What cloud environments does CDR cover?
Comprehensive CDR covers the full cloud stack, not just IaaS. That means IaaS environments like AWS, Google Cloud, and Azure for infrastructure-level threats; Kubernetes for containerized workload attacks; and SaaS applications for account takeover and OAuth abuse. The reason coverage breadth matters is that attackers move across layers. An attacker who compromises a SaaS credential may pivot to cloud infrastructure through OAuth integrations. Comprehensive CDR monitors these connections, not just individual layers in isolation.
How does CDR relate to MDR?
CDR is a cloud-specific extension of the MDR model. An MDR provider that offers CDR applies the same 24×7 human-led, AI-assisted detection and response model to cloud infrastructure that it applies to endpoints and networks. The advantage of MDR-delivered CDR is correlation: a suspicious CloudTrail event becomes far more meaningful when correlated with endpoint activity, identity behavior, and network data from the same environment. MDR providers with genuine cloud expertise—not just generic SIEM analysis applied to cloud logs—provide meaningfully better detection quality.
What threats does cloud detection and response detect?
CDR is designed to catch the attacks that traditional tools miss in cloud environments: credential compromise and API abuse (attackers using legitimate credentials to access cloud services), cryptomining (compromised compute resources used to mine cryptocurrency), data exfiltration (bulk access to cloud storage buckets or database exports), lateral movement across cloud accounts and services, container escape from Kubernetes workloads to underlying infrastructure, and privilege escalation through IAM manipulation. The common thread is that these are runtime behaviors, not configuration issues, which is why CDR’s continuous monitoring approach is necessary.
Do I need CDR if I already have CSPM?
Yes, and the reason is straightforward: CSPM and CDR protect against different attack scenarios. CSPM finds configuration risks before they’re exploited. CDR detects attacks that succeed despite good posture (which is most attacks) because the most common initial access technique in cloud environments is credential theft, not exploitation of misconfigurations. An attacker with valid credentials looks like a legitimate user to CSPM. CDR’s behavioral detection is what catches them. The right answer is both layers working together.