Table of Contents
Modern security operations centers face a critical challenge: making dozens of security tools work together seamlessly. The average SOC uses anywhere from 10 to 50 different security technologies, from SIEM platforms to endpoint detection tools, each generating thousands of alerts daily. Without proper integration, these tools create information silos that blind security teams to sophisticated attacks.
Effective SOC integration requires a strategic approach that prioritizes unified visibility, automated workflows, and centralized orchestration. Organizations that successfully integrate their security stack see dramatically improved threat detection, faster incident response times, and significant reductions in analyst burnout from alert fatigue.
SOC tool integration
SOC tool integration refers to the process of connecting disparate security technologies to enable data sharing, event correlation, and coordinated response actions across your entire security ecosystem. Rather than managing each tool in isolation, integration creates a unified security operations environment where tools communicate through standardized interfaces and share contextual information.
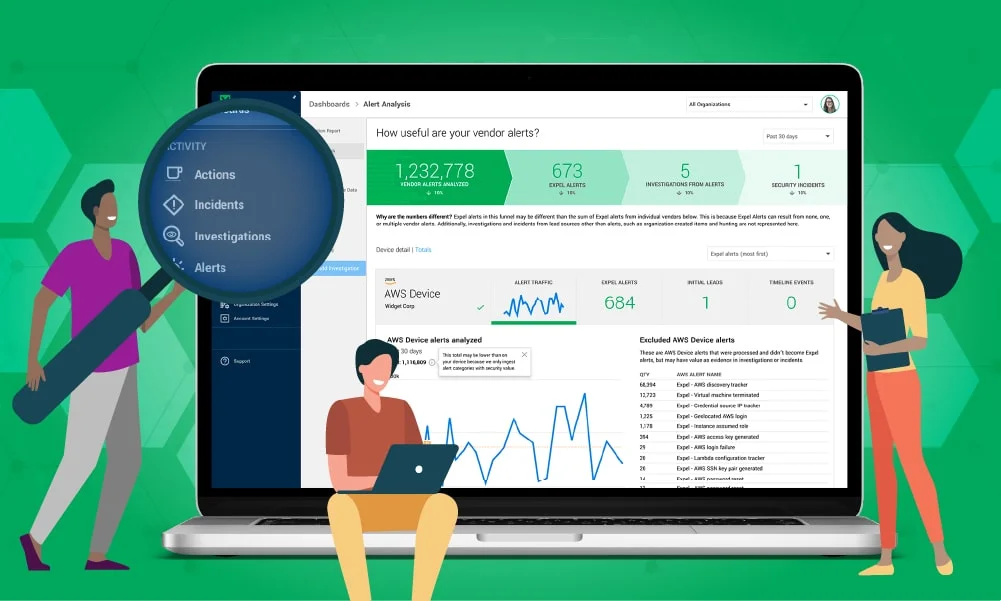
The primary goal of SOC tool integration is achieving what security professionals call “single pane of glass” visibility—the ability to view and manage security across all systems from one centralized location. This doesn’t mean forcing all tools into literally one dashboard, but rather creating the ability to correlate events and coordinate responses across your entire technology stack without analysts manually pivoting between disconnected consoles.
Integration platforms act as the connective tissue between security tools. Expel Workbench™, for example, integrates with over 130 different security technologies across cloud, endpoint, network, and identity layers. This approach allows organizations to leverage their existing security investments while gaining the benefits of centralized orchestration and automated workflows.
The core components of effective SOC integration include:
API connectivity enables programmatic communication between tools, allowing them to exchange data, trigger actions, and share intelligence automatically. Modern security tools typically expose RESTful APIs that support integration with other platforms. Organizations should prioritize tools with robust, well-documented APIs when building their security stack.
Data normalization translates disparate log formats and alert structures into standardized schemas that can be analyzed consistently. When your SIEM receives events from CrowdStrike, Microsoft Defender, and Palo Alto firewalls simultaneously, data normalization ensures all events can be correlated effectively regardless of their original format.
Log aggregation centralizes security event data from across the environment into repositories where it can be searched, analyzed, and retained for compliance purposes. According to Expel’s research on SOC efficiency, most organizations already have access to valuable measurement data through existing security tools—they simply need to aggregate and analyze it systematically.
Event correlation identifies relationships between security events from different sources to detect complex attack patterns that individual tools might miss. A sophisticated attack might begin with a phishing email, progress to credential compromise in your identity system, and culminate in lateral movement detected by network monitoring—correlation ties these discrete events into a coherent incident timeline.
Context enrichment adds business-relevant information to technical security events, helping analysts understand the significance and urgency of each alert. Enrichment might include asset criticality, user role information, threat intelligence context, or previous incident history related to the affected systems.
Effective integration architecture typically follows a hub-and-spoke model, with a central orchestration layer coordinating communication between individual security tools. This approach avoids the complexity of creating point-to-point integrations between every pair of tools in your stack.
Security operations platform integration
Security operations platform integration creates the operational foundation for modern threat detection and response. Unlike simple tool-to-tool connections, platform integration establishes a unified environment where security analysts work primarily from a single interface that orchestrates actions across all connected technologies.
Organizations implementing platform integration typically choose between two approaches: building a custom integration layer or adopting a purpose-built security operations platform.
The custom integration approach involves using open-source tools or internal development resources to create connections between security technologies. This provides maximum flexibility and control but requires significant engineering expertise and ongoing maintenance. According to industry research, larger enterprises with dedicated internal SOC teams often prefer this modular approach for greater customization capabilities.
Purpose-built platforms like Expel Workbench provide pre-configured integrations with hundreds of security tools, enabling rapid deployment without custom development work. Expel’s MDR onboarding process demonstrates that organizations can achieve operational security monitoring within seven minutes of starting the integration process through wizard-driven, self-service interfaces.
Bidirectional integration enables both data flow and action execution between platforms and individual tools. Your platform should be able to both receive alerts from your EDR and send containment commands back to isolate compromised endpoints. This two-way communication transforms your security tools from monitoring-only systems into active response mechanisms.
The orchestration layer serves as the command center for your integrated security ecosystem. It manages workflow automation, coordinates multi-tool response actions, and provides the centralized visibility that prevents critical threats from falling through gaps between disconnected systems. Expel’s approach to auto remediation demonstrates how platform orchestration enables automated containment actions across multiple security technologies while maintaining expert analyst oversight.
Unified visibility doesn’t mean displaying every alert from every tool—that approach recreates the alert fatigue problem you’re trying to solve. Instead, effective platform integration provides filtered, prioritized, and correlated findings that help analysts focus on genuine threats. Research on building 24×7 SOCs shows that mature operations filter thousands of raw daily alerts down to 50-200 requiring human review, with only 5-20 representing actual incidents.
Platform integration should also enable seamless analyst workflows. Security professionals shouldn’t need to log into a dozen different consoles to investigate a single incident. Your platform should provide enough context and tooling to complete most investigations without leaving the primary interface, while still enabling deep-dive analysis in native tool consoles when necessary.
How to integrate SOC technologies
Successfully integrating SOC technologies requires methodical planning, phased implementation, and continuous optimization. Organizations that rush integration without proper preparation often end up with unstable connections, incomplete data flows, or worse—false confidence in monitoring that doesn’t actually work.
Start by conducting a comprehensive technology inventory. Document every security tool currently deployed, including SIEMs, EDR platforms, firewalls, cloud security tools, identity systems, and network monitoring solutions. For each tool, identify what data it generates, what APIs or integration methods it supports, and what role it plays in your detection and response workflow.
Prioritize integration based on detection value and operational impact. Focus on technologies that generate high volumes of actionable alerts or control critical response capabilities. Leave lower-priority integrations for later phases.
Establish integration architecture early in your planning process. Will you use a commercial security operations platform, build custom integrations, or pursue a hybrid approach? Your architecture decision significantly impacts implementation complexity and ongoing maintenance requirements.
Validate data flows thoroughly before declaring integrations operational. It’s surprisingly common for organizations to believe they have working integrations when critical data isn’t actually flowing correctly. Expel’s integration approach includes real-time validation that provides immediate feedback on integration health, allowing teams to quickly identify and resolve configuration issues.
Configure bidirectional integration for tools that support response actions. Reading alerts from your EDR is valuable, but the real power comes from enabling your security operations platform to trigger containment actions like host isolation or process termination. Automated response capabilities dramatically reduce time-to-containment for validated threats.
Plan for data normalization challenges. Different security tools use varying terminology for similar concepts—what one platform calls a “critical” alert might be “high” severity in another system. Establish standardized severity levels, event taxonomies, and naming conventions across your integrated environment to ensure consistent analysis and reporting.
Test integrations under realistic conditions before relying on them for production monitoring. Generate test alerts in each integrated tool and verify they appear correctly in your central platform with appropriate context and correlation. Validate that response actions execute successfully and don’t cause unintended disruptions.
Implement monitoring for your integrations themselves. Integration failures can create dangerous blind spots in your security monitoring. Your platform should alert when integrations stop functioning or data ingestion drops unexpectedly.
Document integration configurations, dependencies, and troubleshooting procedures. When an integration breaks at 2am during an active incident, you need clear documentation to restore functionality quickly. Include API credentials, endpoint URLs, required permissions, and common failure scenarios in your documentation.
Plan for ongoing maintenance and optimization. Security tools release updates regularly, sometimes introducing breaking changes to APIs or data formats. Budget time for testing integration updates before deploying them to production, and establish processes for monitoring integration health over time.
SIEM EDR XDR integration
SIEM, EDR, and XDR integration represents the cornerstone of modern threat detection and response capabilities. These three technology categories serve complementary purposes—SIEM provides centralized log management and correlation, EDR delivers deep endpoint visibility and response, while XDR extends detection across multiple security layers.
What’s the best way to integrate SIEM with EDR?
Integrating SIEM and EDR creates a powerful combination where comprehensive endpoint visibility feeds centralized correlation and analysis. The most effective integration approach depends on your SIEM’s native capabilities and your architectural preferences.
Native integrations often provide the deepest feature support when your SIEM vendor offers purpose-built connectors for your EDR platform. Expel’s integration with multiple SIEM providers demonstrates how organizations can maintain their existing SIEM investments while adding enhanced detection and response capabilities through proper integration architecture.
API-based integration offers maximum flexibility when native integrations aren’t available or don’t meet your requirements. Modern EDR platforms expose RESTful APIs that enable custom integration development. This approach requires more technical expertise but provides complete control over what data flows to your SIEM and how it’s formatted.
Consider what EDR data actually provides value in your SIEM. Not every EDR event belongs in centralized log storage—that approach generates massive data volumes and associated costs without proportional security value. Focus on ingesting high-fidelity alerts, process execution data for unusual activity, and network connection information that aids lateral movement detection.
Bidirectional integration enables your SIEM to both receive EDR alerts and trigger EDR response actions. When your SIEM correlation identifies a compromised endpoint, bidirectional integration allows automated or analyst-initiated host isolation through your EDR platform without switching consoles.
How do you avoid tool sprawl?
Tool sprawl—the accumulation of redundant or underutilized security technologies—creates significant operational challenges. Integration helps mitigate tool sprawl, but only when accompanied by strategic technology decisions.
Evaluate whether new tools genuinely address detection gaps or simply duplicate existing capabilities. Research on SOC tool selection indicates that organizations often purchase XDR platforms while maintaining separate SIEM and EDR tools, creating unnecessary overlap.
Consolidate around platforms with broad native integrations rather than accumulating specialized point solutions. A security operations platform that natively integrates SIEM, SOAR, and XDR capabilities often provides better outcomes than three separate products requiring custom integration.
Establish clear criteria for technology retirement. When you add new capabilities through integration or consolidated platforms, actively sunset redundant tools rather than leaving them in place “just in case.” Maintaining unused or redundant tools wastes licensing costs and creates confusion about which systems analysts should trust.
Should SOC tools share a common platform?
The single-vendor versus best-of-breed debate continues in security operations. Single-vendor approaches like Microsoft’s integrated stack (Sentinel SIEM, Defender EDR, and Defender XDR) offer native interoperability and simplified management but limit flexibility and create vendor lock-in risk.
Best-of-breed approaches provide maximum choice and customization but require more complex integration work. Expel’s model of integrating with 130+ different technologies demonstrates that best-of-breed can work effectively when you have strong integration architecture and dedicated resources for maintaining connections.
Most organizations benefit from a hybrid approach—standardizing on a single platform for core SIEM/SOAR/XDR functions while integrating best-of-breed solutions for specialized needs like cloud security posture management or identity threat detection.
What about cloud security tool integration?
Cloud security introduces additional integration complexity because cloud-native tools often don’t fit traditional integration patterns. Your AWS security alerts, Azure Defender findings, and Google Cloud Security Command Center events all use different formats and delivery mechanisms.
Cloud SIEM solutions designed for cloud-native environments often handle cloud security integration more gracefully than traditional on-premises SIEMs. Consider cloud security posture management (CSPM) integration as a distinct requirement from runtime detection integration. CSPM tools identify misconfigurations and compliance drift but generate different alert types than runtime detection tools. Your integration architecture needs to handle both.
How do you maintain integrations over time?
Integration maintenance often receives insufficient attention during initial implementation planning. Vendors release API updates, change authentication methods, or modify data formats—any of which can break existing integrations.
Establish automated monitoring for integration health. Your security operations platform should actively verify that expected data volumes are flowing from each integration and alert when connections fail or data streams stop.
Create integration runbooks that document configuration settings, authentication credentials, and troubleshooting procedures. When an integration breaks during an incident, you need immediate access to restoration procedures.
Budget time for quarterly integration reviews. Test that integrations still function correctly, verify data quality hasn’t degraded, and update configurations for vendor changes or new feature releases.
Security tool consolidation
Security tool consolidation represents a strategic approach to reducing complexity while improving security outcomes. Rather than simply integrating more tools, consolidation involves actively reducing your security technology footprint by replacing multiple specialized tools with unified platforms that deliver equivalent or superior capabilities.
The business case for consolidation extends beyond technology costs. Organizations building 24×7 SOCs face substantial annual licensing costs—potentially $800,000 to $1.2 million for advanced SOCs with SIEM, EDR, network forensics, SOAR platforms, and threat intelligence feeds. These technology costs compound with implementation expenses, ongoing tuning requirements, and the analyst time required to manage disparate systems.
Alert fatigue drives consolidation urgency. Security teams managing dozens of disconnected tools face overwhelming alert volumes that make effective security impossible. Mid-sized organizations often see 1,000 to 5,000 raw daily alerts from security tools. Without proper consolidation and filtering, analysts spend more time managing tools than investigating threats.
Modern security platforms increasingly offer consolidated capabilities that previously required multiple products. XDR platforms, for example, combine endpoint detection, network visibility, and sometimes cloud security in unified systems. SIEM and XDR platforms consolidate detection and response capabilities that historically required separate SIEM and EDR purchases.
Consolidation doesn’t mean eliminating all specialized tools. Some security requirements genuinely need purpose-built solutions. Cloud security posture management, for instance, addresses different problems than runtime threat detection and may justify separate tooling. The goal is eliminating redundant capabilities while preserving specialized functions that deliver unique value.
Evaluate consolidation candidates based on actual capability overlap rather than vendor marketing claims. Two tools might claim to “detect threats” while addressing completely different attack vectors with minimal practical overlap. Conversely, your SIEM and SOAR platforms might have significant functional redundancy that wastes resources.
Plan for consolidation systematically rather than opportunistically. Organizations that consolidate only when contracts come up for renewal often miss optimization opportunities and perpetuate inefficient architectures. Annual technology strategy reviews should explicitly evaluate consolidation opportunities across your security stack.
Consider whether managed detection and response services might enable consolidation while improving outcomes. MDR providers like Expel deliver comprehensive security operations capabilities without requiring organizations to deploy and manage extensive tool stacks themselves. MDR can consolidate not just tools but the operational expertise required to run them effectively.
SOC technology stack integration
Comprehensive SOC technology stack integration extends beyond core detection tools to encompass the full range of technologies supporting security operations. A complete integration strategy addresses endpoint protection, network security, cloud platforms, identity systems, business applications, and case management tools.
Integration architecture patterns significantly impact implementation complexity and long-term maintainability. The most common patterns include point-to-point integration, hub-and-spoke architecture, and API gateway approaches.
Point-to-point integration creates direct connections between pairs of tools. This pattern works for small environments with few technologies but becomes unmanageable as your stack grows. With just 10 security tools, full point-to-point integration could require up to 45 separate connections—each needing individual configuration and maintenance.
Hub-and-spoke architecture centralizes integration through a common platform or orchestration layer. Tools connect to the central hub rather than directly to each other, dramatically reducing integration complexity.
API gateway patterns add an abstraction layer between your security operations platform and individual tools. The gateway translates between different API formats and handles authentication, rate limiting, and error handling centrally. This approach works well in complex environments but adds architectural complexity.
Data flow architecture determines how information moves through your integrated stack. Real-time streaming provides immediate access to security events but requires more infrastructure and generates higher data volumes. Batch processing reduces infrastructure costs but introduces detection latency that may be unacceptable for time-sensitive threats.
Consider data retention and compliance requirements when designing integration architecture. Your SIEM might need to retain logs for years to meet compliance mandates, while your XDR platform focuses on recent activity with shorter retention periods. Integration architecture should support both requirements without duplicating storage costs unnecessarily.
Integration with business applications increasingly becomes important for comprehensive risk management. Monitoring authentication events, configuration changes, and data access in these platforms provides visibility into threats that purely security-focused tools might miss.
Case management and ticketing system integration ensures security workflows align with broader IT operations. When your SOC identifies issues requiring remediation, integrated ticketing creates tracked work items in systems your IT teams already use rather than generating orphaned alerts in standalone security consoles.
Measurement and optimization of your integrated stack requires consistent metrics collection across all components. According to research on SOC performance efficiency, most organizations already have access to valuable metrics through existing tools—they need to aggregate and analyze this data systematically to identify integration gaps or optimization opportunities.