Product · 4 MIN READ · JAKE GODGART, CLAIRE HOGAN, DR. XENIA MOUNTROUIDOU, BROCK WRIGHT, DAVID CASAGRANDE, MATTHEW KAY AND EMILY GARTON · JAN 9, 2026 · TAGS: AI & automation / Detections
TL;DR
- We’ve added new AI-generated descriptions to articulate the purpose and logic behind each of our detection rules (in plain English) to improve transparency and understanding.
- Detections that were previously bundled will now reveal the specific underlying rules used to help customers clearly understand each of Expel’s detection strategy rules.
- See exactly how your security coverage evolves as our engineering team continuously adds new rules and sharpens detections.
Imagine you’re driving down a highway and your check engine light turns on. The car detected an issue, but the engine light on your dashboard doesn’t tell you exactly what’s wrong. To learn what the problem is (and fix it), you take the car to a mechanic. After ten minutes behind a closed garage where they hook it up to a diagnostic system and mess around under the hood, they tell you it’s fixed and hand you a bill for $500.
Huh? What did they do? Did they replace a major part or just tightened a loose gas cap? You just know that you paid an expert to fix it, and left with a “trust us” sticker (and possibly an upsold new air filter).
Security companies often treat customers this way. They tell you they’re protecting your organization with thousands of proprietary detections and a unique detection strategy for each attack surface, but they don’t show you the work in a way that makes sense (if they show you at all). Sure, some vendors might provide transparency with a list of detections or even the raw logic—similar to if the mechanic gave you an itemized bill—but what’s actually happening remains a mystery unless you “pop the hood” and dissect every rule yourself. That is, if the provider even gives you access.
To our chagrin, we’ve used a similar approach to our detection strategies at Expel. While our customers have always had transparent access to all of our detections, they haven’t been presented in a way that is easy to understand. So now we’re using Expel AI to make our detection strategy easier to consume for humans (and Expel Workbench™).
The black box problem
For a long time, our detection engineering team has relied on what we call logical containers. Think of these as groups of detections. Engineers used to keep things organized and efficient by bundling a bunch of different detection rules into a logical container under one broad name.
This bundling helps engineers work faster, but it creates a “black box” for you. For example, you might see a single detection in your dashboard called “Microsoft Defender for Endpoint Malware.” It looks simple, but it’s actually hiding 23 separate, granular rules that fire on different types of suspicious behavior. This makes it hard to see the true breadth of the protection you pay for. If you can’t see the logic, it’s harder to verify that it’s actually working for your specific environment. It creates an internal barrier to understanding your own security posture.
“Popping the hood” on Expel’s detection logic
We built a new feature called AI Detection Explainability to fix this. It translates that list of raw code of complex logic inside our rules into plain English, using large language models (LLMs).
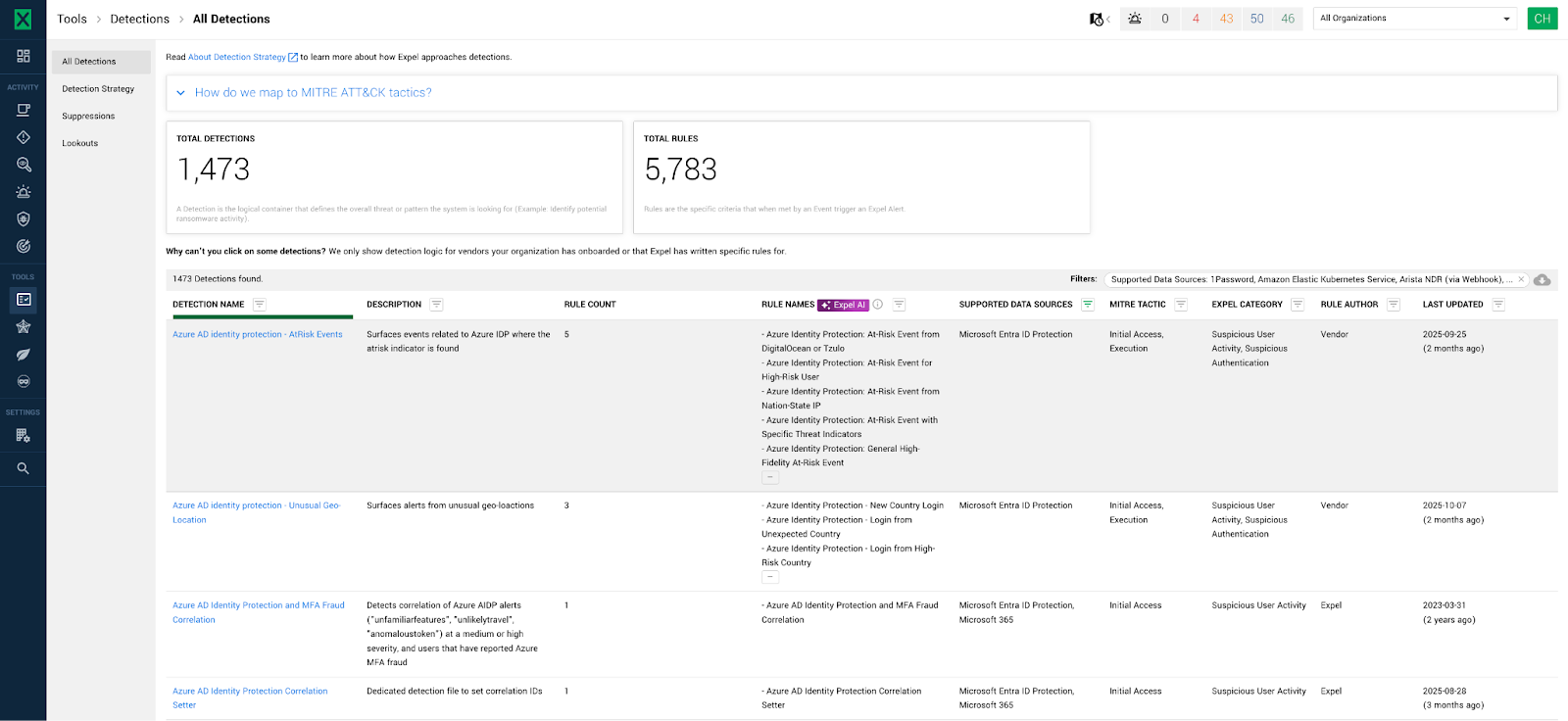
Here is what you will find on your Detection page in Expel Workbench™ now:
- Rule counts: We added a column that shows exactly how many sub-detections live inside each container.
- Clear rule names: You get a list of human-readable names for every single rule generated by the LLM.
- Plain English descriptions: You can read exactly what criteria trigger an alert.
We know that AI can’t just be left to run on its own. That’s why our Detection Engineering team and our SOC analysts continually review these rules to ensure the descriptions are accurate and make sense in a security context.
Why this matters for your team
Transparency is one of our core values at Expel. This move continues to help us move the conversation from “trust us” to “here’s the proof.” Here’s why it matters:
You see the true breadth of your protection
Roughly one third of our detection rules could trigger more than one type of Expel alert. On average, those bundled detection rules contain nine separate sub-detections. Before today, those nine rules were invisible to you. Now, you can see the full scale of the work we’re doing to protect your environment. It proves the value of the detection strategy you have invested in.
Verification becomes a reality
You can’t manage what you can’t see. When the logic is clear and explainable, you can finally “trust and verify.” You’ll know exactly which rules are active and what specific behaviors they’re hunting for. This boosts your confidence in our detections and gives you more transparency.
Security health improves
Complex, hidden rules are hard to maintain and even harder to optimize. By breaking them down into simple, readable pieces, we make it easier to assess the health of your detections. This makes it easier for you to identify new relevant Expel detections in our detection library and automatically apply them to your organization.
Built with a privacy-first mindset
We know that using AI in security requires a high level of caution. We built this feature with appropriate guardrails so your data stays secure and private, including things like:
- Self-hosted systems: We don’t send anything to public AI systems.
- Self-managed tools: The tools we use are managed entirely within our own secure environment to prevent data from leaking externally.
For more information about how we use customer data, see our Expel Workbench and Services Privacy Policy.
Transparent at our core
We’re tired of the black box approach to security, especially when it comes to the detection logic. After all, you’re paying for the added value we place on detecting, investigating, and responding to the threats that live between what your individual tools find.
This way, we aren’t just turning off your check engine light; we’re showing you exactly how the engine is running. We want you to understand your detection strategy so you can be confident in our team’s ability to detect threats in your environment.
Transparency shouldn’t be a feature. It should be the standard.