YOUR SIEM. OUR EXPERTISE.
Managed SIEM services.
No lock-in. No black box.
Your best engineers shouldn’t be stuck tuning SIEM rules. We’ll take it from here. Every rule visible. Every decision explainable. No platform switch required.
WHAT YOU ACTUALLY GET
You paid for enterprise detection. Time to get it.
Get the outcomes you actually expected when you bought your SIEM. We handle the grunt work.
You focus on what matters.
HOW WE DO IT
Our engineers live in your environment.
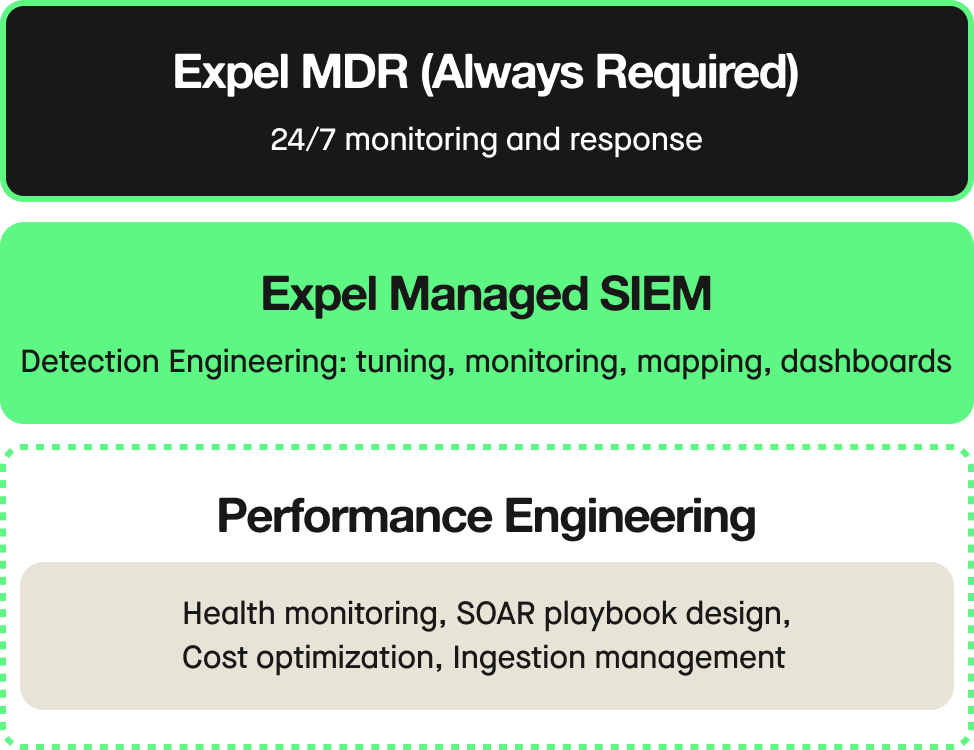
Two service components. One outcome: make your SIEM perform.
BRING YOUR SIEM. KEEP YOUR LOGIC.
We work in your environment. Not ours.
No vendor lock-in, no IP held hostage, no migration risk. Just detection engineering in the SIEM you already own. And the logic we build is yours to keep.
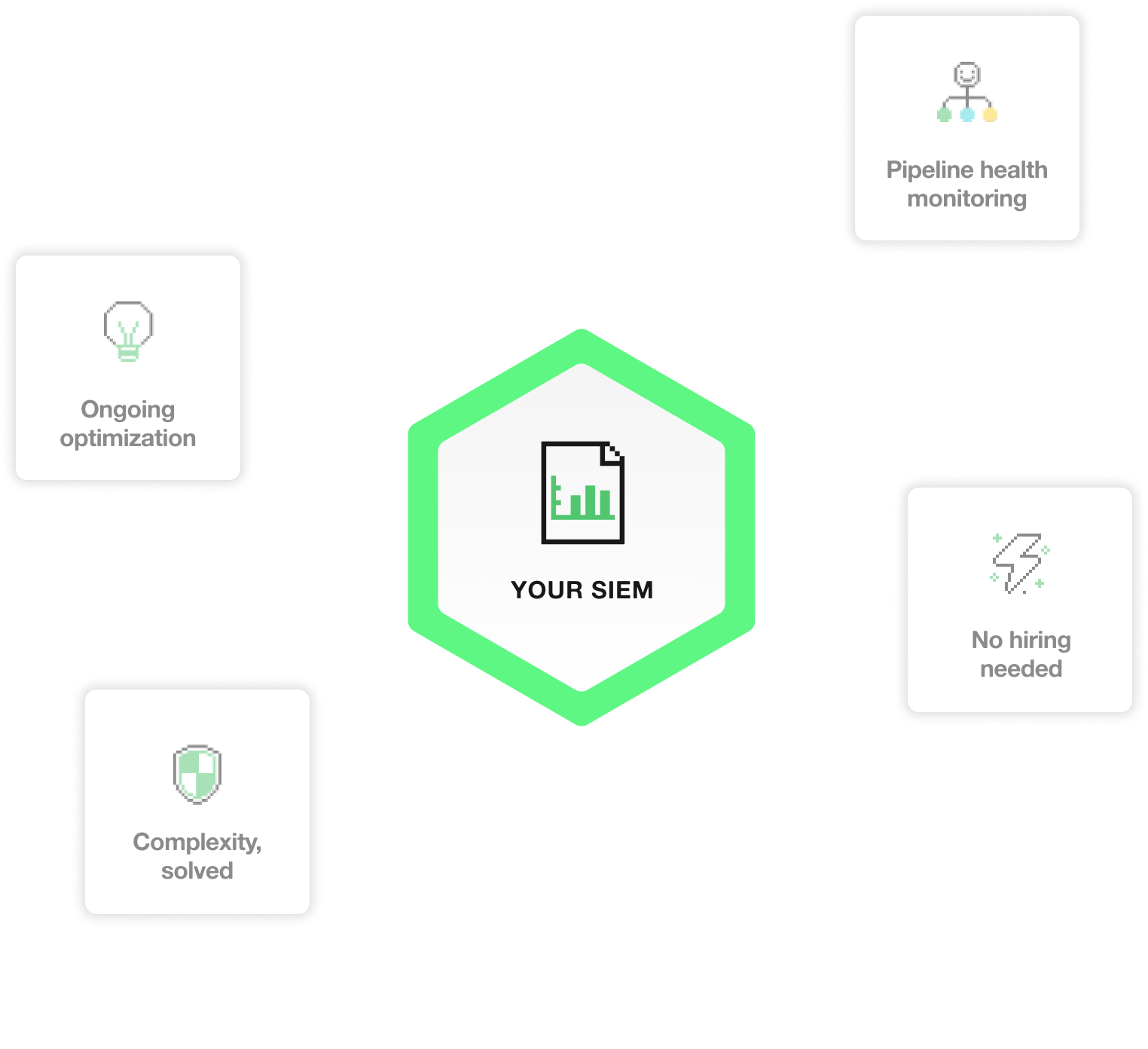
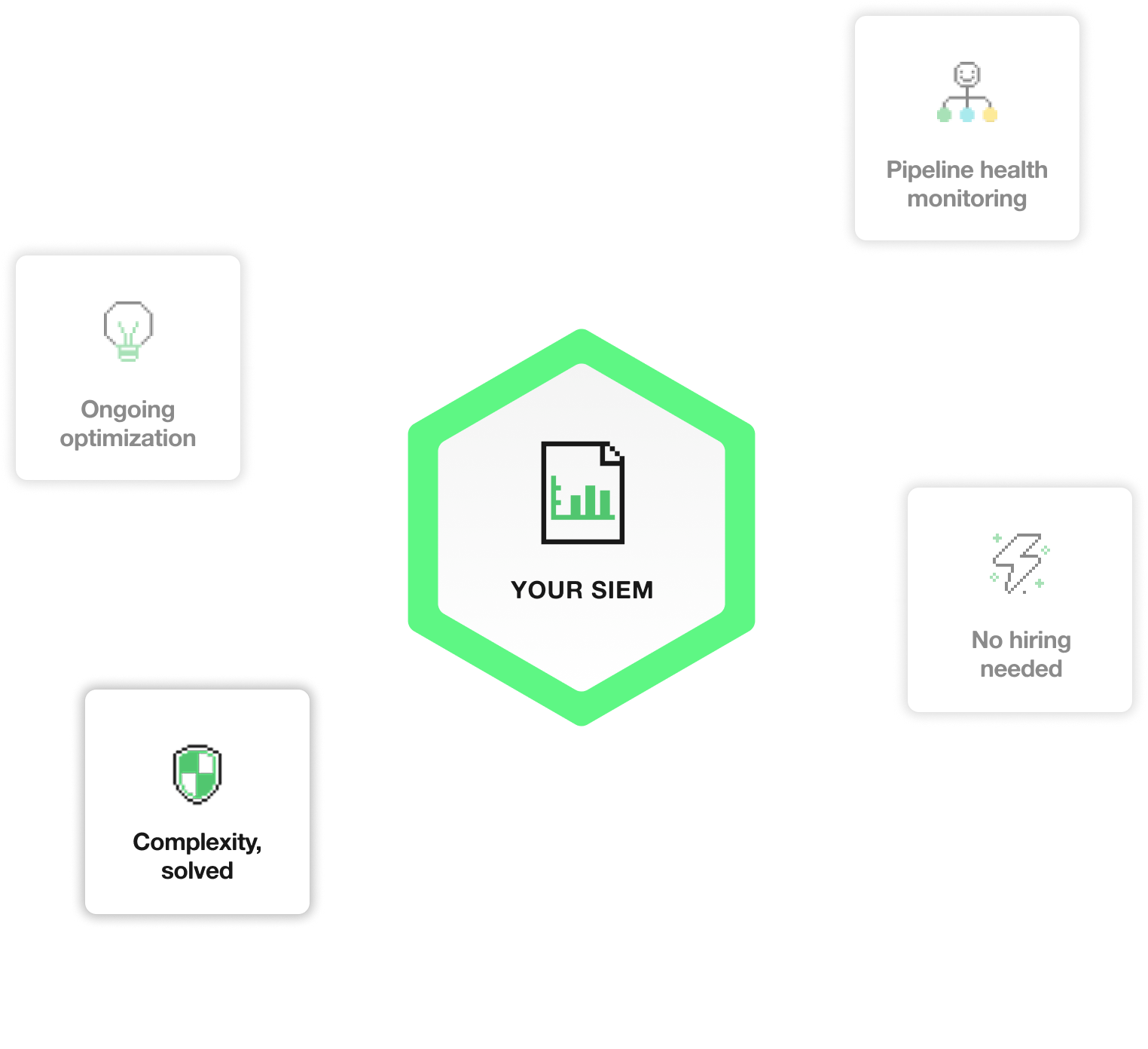
Ongoing Optimization
We don’t just manage your rules. We fix them.
We write the rules, translate threat intel into working queries, test against real data, and tune as your environment changes. Every week, without fail.
PIPELINE HEALTH MONITORING
You can’t fix what you can’t see.
If a critical log source stops flowing, your SIEM goes blind—quietly, without warning. We catch it before it becomes a gap an attacker can exploit.
THE HIRING PROBLEM, SOLVED
Skip the six-month search.
We’re already here.
Detection engineers are hard to hire and harder to keep. Expel’s team is already proven, rated a detection engineering leader by top analysts.
WE'VE SEEN WORSE
Complex environment? Bring it.
Custom parsers. Legacy rules. Multi-cloud configurations. We adapt to your environment, no matter what you’ve inherited.
BRING YOUR SIEM. KEEP YOUR LOGIC.
We work in your environment. Not ours.
No vendor lock-in, no IP held hostage, no migration risk. Just detection engineering in the SIEM you already own. And the logic we build is yours to keep.
Ongoing Optimization
We don’t just manage your rules. We fix them.
We write the rules, translate threat intel into working queries, test against real data, and tune as your environment changes. Every week, without fail.
PIPELINE HEALTH MONITORING
You can’t fix what you can’t see.
If a critical log source stops flowing, your SIEM goes blind—quietly, without warning. We catch it before it becomes a gap an attacker can exploit.
THE HIRING PROBLEM, SOLVED
Skip the six-month search.
We’re already here.
Detection engineers are hard to hire and harder to keep. Expel’s team is already proven, rated a detection engineering leader by top analysts.
WE'VE SEEN WORSE
Complex environment? Bring it.
Custom parsers. Legacy rules. Multi-cloud configurations. We adapt to your environment, no matter what you’ve inherited.
Frequently asked questions
Managed SIEM is a service where an external team handles the detection engineering work your SIEM requires to actually perform—writing and tuning detection rules, monitoring data pipeline health, assessing coverage gaps, and keeping your detections current as your environment evolves.
The difference from in-house management isn’t the technology—it’s the expertise and bandwidth. In-house teams often have the SIEM but not the dedicated detection engineering headcount to run it well. Detection engineers are expensive to hire, slow to ramp, and hard to retain. Managed SIEM services give you that capability without the hiring timeline, the overhead, or the risk of losing institutional knowledge when someone leaves.
The terms are largely interchangeable—co-managed SIEM is an older label for what’s more commonly called managed SIEM services today. Both describe a model where an external team works alongside your organization to handle detection engineering, rule tuning, and pipeline health monitoring in your existing SIEM environment.
The “co-managed” framing historically emphasized shared ownership and visibility, which remains true of how Expel operates: your team retains control of infrastructure and access management, while Expel owns the security layer—detection logic, coverage assessment, and pipeline monitoring. You see everything we do. Nothing happens in a black box.
No. Expel’s managed SIEM services are built around a bring-your-own-SIEM model—we work directly in the environment you already have. We don’t require you to license a SIEM through us, we don’t profit when your data volume grows, and we don’t have any incentive tied to which platform you’re on. Our job is to make your existing investment perform, not to migrate you onto something we resell. Every detection rule we write lives in your SIEM in native syntax, and it belongs to you—if you ever leave, you keep everything we built.
Most traditional MSSPs deploy out-of-the-box vendor rules and tune reactively—meaning they respond to false positives after they fire, rather than preventing them proactively. Expel’s detection engineering team works continuously and proactively: writing behavioral rules tailored to your environment, assessing coverage against the MITRE ATT&CK framework, and refining detections as your environment changes.
There’s also a transparency difference. With a traditional MSSP, detection logic is often hidden in a black box—you’re told an alert fired, but not why the rule exists or how it’s tuned. With Expel, every rule, every filter, and every tuning decision is visible in Expel Workbench in real time. No “trust us.” Just full visibility into the work being done in your environment.
The initial impact is typically felt in two areas: false positive reduction and coverage gap identification. When Expel’s detection engineering team onboards a new environment, we begin by assessing existing rule coverage against MITRE ATT&CK—identifying gaps, redundancies, and rules that are generating noise without producing true positives. From there, we write new detections tailored to your environment and tune out-of-the-box vendor rules that aren’t performing. The result is a detection program that gets measurably better week over week, without requiring your team to own the engineering work that makes it possible.