FOR CORVUS POLICYHOLDERS
Truly transparent managed detection and response (MDR)
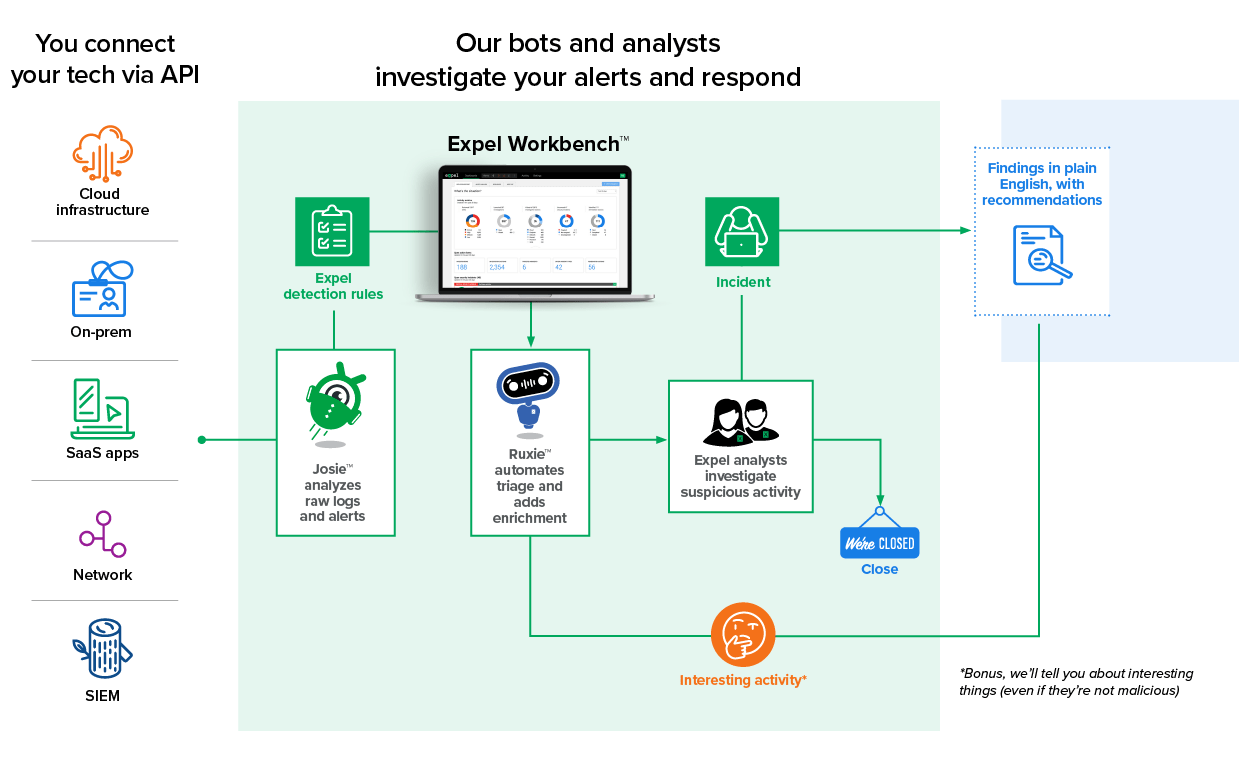
Take control of your business risk with the Expel 24×7 managed detection and response (MDR) offering. With monitoring for everything from cloud apps and infrastructure to networks and endpoints, you have the ongoing awareness needed to protect your business from security vulnerabilities and threats.
Improve security quickly.
- Expel improves your security fast (in hours or days…not months).
- A 96% reduction in threat response time
- When investigations turn to incidents, the Expel median alert-to-fix timelines are shorter than the time it takes to deliver a pizza.
- Your team and the Expel team view the same information to make the best decisions for your business, quickly (partnership AND transparency!)
Get to know Expel
And now a word from legal ... Information submitted on this form may be associated with other information we have collected and used pursuant to the Expel Online Privacy Policy.
Peace of mind is nice. You also get results you can see and measure
Reduce your …
SOC start-up time and cost
Skip the 12+ months and $2M+ to build your own SOC from scratch
Alert-to-fix time
When alerts go to analysts our median triage time is 3 minutes
Alert monitoring costs
Our analysts and bots evaluate each alert (including the ones you don’t have time to look at)
Get more …
Cloud security and visibility
Our detection and response approach is unique to each cloud provider
Response quality
Our roots are in incident response so we know which rocks to turn over and we’ll show you the details
Analyst time for risks unique to you
Since we’re chasing down alerts your team can focus on risks unique to you